The hack of U.S. retailer Target put attacks on point of sale systems on the radar, and prompted major retailers to revisit the security of the systems that accept credit card transactions.
Now research from Arbor Networks is warning that hackers and cyber criminals are doubling down on point of sale (PoS) systems with a wide range of specialized PoS malware and targeted attacks. Arbor says it has data suggesting that PoS compromises may be widespread, and undetected.
Arbor’s Security Engineering & Response Team (SERT) issued its findings in a Threat Intelligence Brief (2014-6) report. The company said that “ambitious threat actors” are using targeted attack campaigns against PoS networks. The “longevity and extent” of PoS attack campaigns – even at wealthy and sophisticated organizations – is “a serious concern.”
[Read Security Ledger’s coverage of the Target data breach here.]
“In organizations with security teams and well-managed network infrastructure, point of sale compromises have proliferated for months prior to detection. If attackers are able to launch long-running campaigns in such enterprise retail environments, one can conclude that many other organizations with less mature network and infrastructure management are also at serious risk,” the report reads.
PoS Malware: A Growing Family of Threats
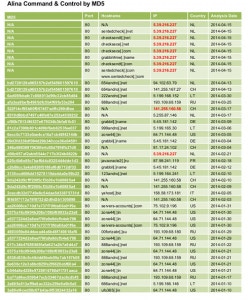
Arbor’s SERT tracks a number of malware families that target Point of Sale systems. In addition to BlackPoS – the malware associated with the Target breach – Arbor said PoS malware families with names like Alina, Chewbacca, vSkimmer, POSCardStealer and JackPoS are active in the cyber underground. Researchers have also documented specialized hacking tools for PoS systems, including software to ‘brute force’ compromise PoS terminals.
Arbor’s data suggests that development of many of those malware families is continuing, and that there is an appetite for such tools in the criminal underground. For example, Arbor said that the JackPoS malware was being developed as late as March 5, 2014 with 33 different variants created between late October, 2013 and early March, 2014.
Each malware exhibits telltale signs of compromise that organizations can use to determine whether a compromise has taken place. However, Arbor said that its research suggests that vulnerable and weakly secured PoS terminals may be common.
The company conducted a test to determine how easy it might be for an attacker to find PoS machines using what it termed “basic scanning techniques.” The ASERT Threat Intelligence team was granted access to NetBIOS scan data provided by the Shadowserver Foundation, a non-profit group focused on battling botnets. The data included the IP address and the NetBIOS name of machines with open TCP port 445 – a telltale sign of a system with weak security or vulnerable configuration. Arbor checked the Shadowserver list against a partial list of known Point of Sale default system names and identified 1,089 point of sale, or point of sale-related systems. Of those, 68 were also running Remote Desktop on TCP port 3389 and 20 were running VNC on TCP port 5900 – two remote management tools that suggest those systems may have already been discovered by hackers.
Arbor is recommending that organizations review their PoS environments both for compliance with Payment Card Industry standards (PCI-DSS). But the company also said organizations with PoS infrastructure should closely review their use of remote monitoring tools to manage those systems and make sure that PoS terminals are hardened and single purpose devices – reducing their attack surface.
A link to Arbor’s (PDF format) report can be found here.