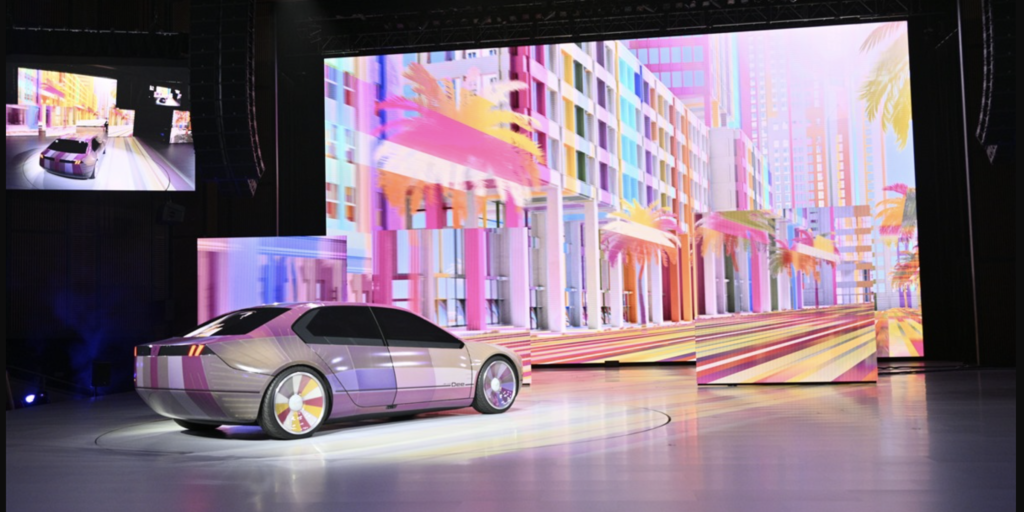
Automakers swear that the security of their connected vehicles is their top priority. So how come researchers just found dozens of software flaws that could give hackers access to millions of cars?
Tag: software
IoCs vs. EoCs: What’s the difference and why should you care?
Security analysts and threat hunters know the importance of IOCs – indicators of compromise. But EOCs – enablers of compromise – are just as important.
Episode 248: GitHub’s Jill Moné-Corallo on Product Security And Supply Chain Threats
In this episode of the Security Ledger Podcast, Paul speaks with Jill Moné-Corallo, the Director of Product Security Engineering Response at GitHub. Jill talks about her journey from a college stint working at Apple’s Genius bar, to the information security space – first at product security at Apple and now at GitHub, a massive development platform that is increasingly in the crosshairs of sophisticated cyber criminals and nation-state actors.
What’s the Future of Detection Teams? Five Predictions for What Lies Ahead
Cyber threats are rampant, but security teams lack the tools, resources, and support to do their jobs effectively today — much less prepare them for tomorrow. In this Expert Insight, Jack Naglieri, the CEO of Panther, writes about where the state of security is currently, and where I see it headed.
Supply Chain Hackers LofyGang Behind Hundreds of Malicious Packages
Researchers at Checkmarx say that a cybercriminal group, LofyGang, has targeted the open-source supply chain with hundreds of malicious packages to steal credit card information, stream accounts, and promote hacking tools.