In this episode of Security Ledger Podcast (#164): your car is spying on you. But who owns the data it collects? Also: LastPass’s Dan DeMichele joins us to talk about why password security is still so hard.
Tag: identity
Spotlight Podcast: Breaking Bad Password Habits to Fight Advanced Threats
In this Spotlight edition of the Security Ledger podcast, Rachel Stockton of LastPass * joins us to discuss the myriad of challenges facing companies trying to secure users’ online activities, and simple solutions for busting insecure user behaviors to address threats like phishing, account takeover and more.
Robot Account Apocalypse: RPA Risk Exploding with Adoption
Robotic Process Automation is taking over mundane tasks in the workplace. But those bots may pose a serious security risk, according to researchers from the firm CyberArk.
Podcast Episode 142: On Supply Chains Diamond-based Identities are forever
In this week’s episode, #142: we continue our series on Life after Passwords: the Future of Online Identity as we are joined by Ophir Gaathon, the CEO of the firm Dust Identity.
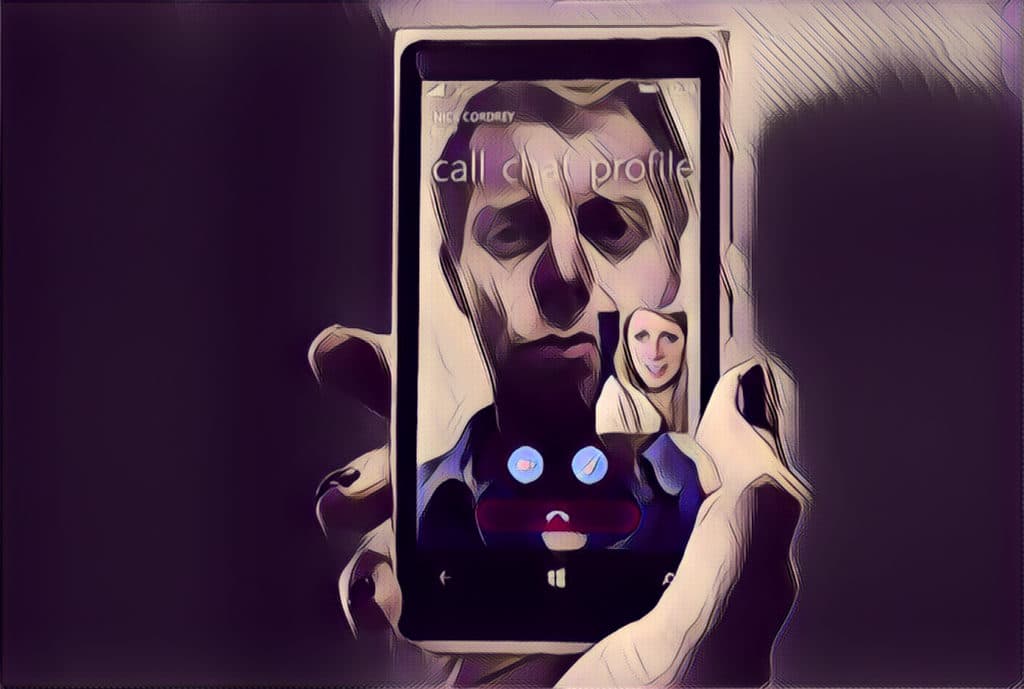
Single Photo uniquely identifies Smartphone that took it
Technology developed by researchers at the State University of New York can create a smartphone “fingerprint” from a single photo captured by the device. The technology may clear the way for a new identity verification system that can secure online transactions or protect smartphone owners from identity theft.