The data-wiping Shamoon malware resurfaced this week at Italian oil and gas contractor Saipem, where it destroyed files on about 10 percent of company PCs, according to a published report. The attacks may be linked to Saipem’s work with Saudi Aramco, a target of earlier Shamoon attacks.
Tag: energy
Pipeline Attacks highlight Third Party Threat to Critical Infrastructure
Recent attacks on the third-party data system of several U.S. pipeline companies highlight the persistent need for better ways to secure industrial control systems (ICSs), particularly when third-party software is in use, security experts said.
DHS Warns Energy Firms Of Malware Used In Targeted Attacks
The Department of Homeland Security warned firms in the energy sector about new, targeted malware infecting industrial control systems and stealing data. DHS’s ICS CERT, the Industrial Control Systems Computer Emergency Response Team, said it is analyzing malware associated with an ICS-focused malware campaign. The malicious software, dubbed “Havex” that was being spread by way of phishing emails and so-called “watering hole” attacks that involved compromises of ICS vendor web sites. DHS was alerted to the attacks by researchers at the security firms Symantec (which dubbed the malware campaign “Dragonfly”) and F-Secure (“Havex”) -a remote access trojan (or RAT) that also acts as an installer (or “downloader”) – fetching other malicious applications to perform specific tasks on compromised networks. One of those additional payloads is a Trojan Horse program dubbed Karagany (by Symantec) that has been liked to prior attacks on energy firms. According to Symantec, the malware targeted energy grid operators, major electricity generation firms, […]
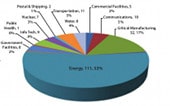
Homeland Security: Hack Attempts On Energy, Manufacturing Way Up in 2013
Attempted cyber attacks on critical infrastructure in the U.S., including energy and critical manufacturing jumped sharply in the first half of 2013, according to a just-released report from the Department of Homeland Security’s Industrial Control System Cyber Emergency Response Team (ICS-CERT). ICS-CERT said that cyber incidents across all critical infrastructure in the U.S. are on pace to double in 2013. The agency has responded to 200 such incidents so far in fiscal year 2013 (October of 2012 to May of 2013), compared to 198 incidents for all of fiscal year 2012. A majority of those incidents – 53% – were against organizations in the energy sector, ICS-CERT reported. The report is just the latest from DHS about threats to the energy sector. The agency warned energy firms after seeing a sharp jump in attacks during 2012, when attacks on energy firms accounted for around 40% of the malicious activity directed […]