Prolexic, a division of Akamai, issued an advisory to Fortune 500 firms on Monday about what it calls “a high-risk threat of continued breaches from the Zeus framework.” The company’s Security Engineering & Response Team (PLXsert) said on Monday that it has observed new payloads from the Zeus crimeware kit in the wild, and that networks of Fortune 500 companies are a prime target. Cyber crime groups are using Zeus to steal login credentials and gain access to web-based enterprise applications, as well as online banking accounts, Akamai warned. “The Zeus framework is a powerhouse crimeware kit that enterprises need to know about to better defend against it,” said Stuart Scholly, senior vice president and general manager, Security Business Unit, Akamai, in a statement. “It’s hard to detect, easy to use, and flexible – and it’s being used to breach enterprises across multiple industries.” A variant of Zeus, Gameover, was the subject […]
Tag: botnet
When The Internet of Things Attacks! Parsing The IoT Botnet Story
I spent most of last week at a conference in Florida going deep on the security of critical infrastructure – you know: the software that runs power plants and manufacturing lines. (More to come on that!) While there, the security firm Proofpoint released a statement saying that it had evidence that a spam botnet was using “Internet of Things” devices. The company said on January 16 that a spam campaign totaling 750,000 malicious emails originated with a botnet made up of “more than 100,000 everyday consumer gadgets” including home networking routers, multi media centers, televisions and at least one refrigerator.” Proofpoint claims it is the “first time the industry has reported actual proof of such a cyber attack involving common appliances.” [Read: “Missing in action at Black Hat: the PC.”] Heady stuff – but is it true? It’s hard to know for sure. As with all these reports, it’s important […]
Juiced: DDoS Attacks 700 Percent Stronger, Iran Joins Top Source Countries
Denial of Service attacks are experiencing a surge in power and duration in the first months of 2013, with Iran joining China and The United States as a top source of the crippling online attacks. The power of distributed denial of service (or DDos) attacks – measured in packets per second – jumped 718 percent in the first three months of 2013, compared to the final three months of 2012, the security firm Prolexic reported on Wednesday. The average bandwidth used in DD0S attacks reached 32.4 million packets per second, overwhelming Internet service providers (ISPs), carriers and content delivery networks designed to mitigate the effects of sudden Internet traffic surges. The data comes from Prolexic’s DD0S Report for the first quarter of 2013. That firm, based in Hollywood, Florida, has become a go-to firm for companies that find their web sites on the receiving end of DDoS attacks. The average attack bandwidth totaled […]
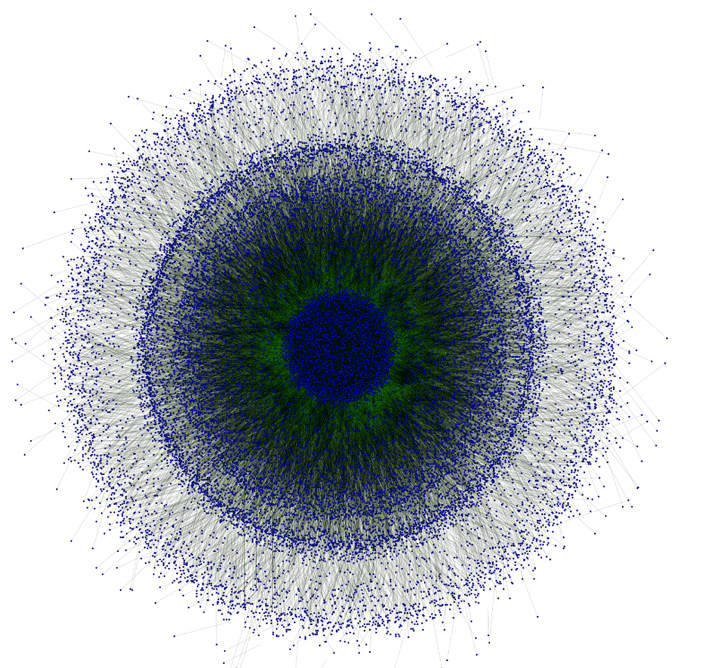
Botnet Of Embedded Devices Used To Map Internet
Botnets are mostly linked with spam e-mail campaigns, denial of service attacks and data theft. But global networks of compromised hosts can be used for a variety of ends – not all of them malicious. That was the idea behind “Internet Census 2012,” a stealth project by an unnamed and unknown researcher/hacker to map the entire IPV4 Internet address space using a massive network of compromised devices. The results, published in the form of a research paper, underscore the problem of unsecured embedded devices, including set top boxes, home routers and critical infrastructure, with the hacker able to locate and compromise these systems, creating a botnet of more than 420,000 nodes. According to a copy of the report, the project grew out of an experiment to locate unprotected devices online using nmap, the open source scanning tool. By compromising each vulnerable host and then enlisting it to scan for other […]