In-brief: 2lemetry, a Denver, Colorado-based startup that manages data from Internet connected devices said last week that it had been acquired by cloud giant Amazon.com.
geolocation
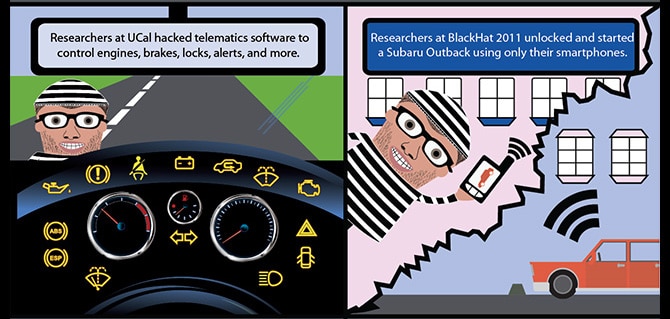
Cyber Lemons: Lawsuit alleges Hackable Cars Pose Risks to Consumers
In-brief: A lawsuit filed in California charges U.S. automakers with endangering their customers by failing to protect ‘connected vehicle’ features from cyber attack.
Automakers Issue Privacy Guidelines For Connected Cars
A group representing some of the leading foreign automakers who sell in the U.S. released guidelines to protect consumer data collected by in-vehicle technologies and make sure that car owners consent to the collection of everything from geolocation data to biometric identifiers. The group, Global Automakers, represents foreign auto manufacturers and original equipment makers (OEMs). The Privacy Principles document (PDF here) include guidance on issues like transparency, anonymity and security and are intended to set ground rules for the collection and use of driver or owner information by increasingly sensor-rich vehicles. “As modern cars not only share the road but will in the not too distant future communicate with one another, vigilance over the privacy of our customers and the security of vehicle systems is an imperative,” said Global Automakers President and CEO John Bozzella in a published statement. The Privacy Principles are voluntary are are based on the U.S. Federal Trade […]
Supply Chain Risk: Raspberry Pi Device Used for War Shipping
An interesting post on supply chain security over at Security Affairs. The post looks at a new approach to supply chain surveillance (and, presumably, attacks): ‘war shipping.’ War shipping is, of course, a play on the ‘war driving’ scene from the early days of consumer wifi, in which cars outfitted with antennae would canvas whole cities, documenting open wi-fi hotspots that could be used to grab some free Internet. In this case, Security Affairs notes a shippable board-sized package designed by security expert Larry Pesce of Paul’s Security Weekly (fka Pauldotcom). The device can be contained in a standard UPS shipping box and delivered to a target network to passively surveil or even attack it. The kit is built on a Raspberry Pi b_ with an AWUS051NH wireless card, a cheap battery charger, kismet and custom software. Pesce demonstrated the device at Derbycon, a Louisville, Kentucky based event last month. The device includes both […]
Ahead of Apple’s Announcement: The Security Implications of Wearables | Trend Micro
The world’s attention will be focused on Apple this week and on the topic of wearables. In an event on Tuesday, the Cupertino company is planning to unveil the latest additions to its popular iPhone line along with a wearable device that most folks are just calling the ‘iWatch.’ But as Apple wrestles with the security of its growing stable of mobile devices and the cloud infrastructure that supports them, what will the impact of wearables be? Well, the folks over at Trend Micro are putting together a series of blog posts that look at that very question. Namely: the (information) security implications of wearables. It makes for some interesting reading. Among other things, Trend There are three very broad categories that we can use to describe what we are talking about. The posts, by Senior Threat Researcher David Sancho, break down the wearables space into three categories: ‘IN’ devices like sensors, ‘OUT’ […]