In-brief: Experts on the security of the Internet of Things warned that lax security and privacy protections are rampant in connected home products, but consumers have no way of knowing whether the products they buy are easy targets for hackers.
BIOS
The Enduring Terribleness of Home Router Security Matters to IoT
Last week, home broadband router maker ASUS was the latest vendor to issue an emergency patch for a critical vulnerability in its products. This, after proof-of-concept exploit code was released for the so-called “Inforsvr” vulnerability that affects several ASUS home routers. That vulnerability -if left unpatched – would allow anyone with access to a home- or small business network that used an ASUS broadband router to, essentially, commandeer the device. The “infosvr” feature is typically used for device discovery by the ASUS Wireless Router Device Discovery Utility, but the service also allowed unauthenticated users to execute commands through it using the “root” permissions, according to researcher Friedrich Postelstorfer, who created a proof of concept exploit for the security hole and released it on January 4. The exploit code finally prompted a patch from ASUS on January 13. The company had spent months analyzing the issue and working on a fix. Patch aside, it has been a worrying month for the […]
Dusting For Malware’s Bloody Prints
Malicious software is nothing new. Computer viruses and worms have been around for decades, as have most other families of malware like remote access tools (RATs) and key loggers. But all our experience with malware hasn’t made the job of knowing when our organization has been hit by it any easier. In fact, recent news stories about breaches at Home Depot, Target, Staples and other organizations makes it clear that even sophisticated and wealthy corporations can easily overlook both the initial compromise and endemic malware infections – and at great cost. That may be why phrases like “dwell time” or “time to discovery” seem to pop up again and again in discussions of breach response. There’s no longer any shame in getting “popped.” The shame is in not knowing that it happened. Greg Hoglund says he has a fix for that latter problem. His new company, Outlier Security, isn’t “next generation […]
Dan Geer’s Other Keynote: Embedded Devices Need A Time To Die
With the Black Hat Conference well under way and DEFCON starting later this week, the security world’s attention will turn to Las Vegas, where some of the cyber security industry’s top researchers and thinkers will be holding court. One of the most anticipated talks is the Black Hat Briefings opening keynote. This year, the honor goes to none other than Dr. Dan Geer, the CISO of In-Q-Tel, the investment arm of the U.S. intelligence sector. Geer’s talk on Wednesday, August 6, 2014 is entitled “Cybersecurity as Realpolitik.” In anticipation of Dr. Geer’s Black Hat, we’re releasing another recent talk he gave: this one a keynote speech at our May, 2014 Security of Things Forum in Cambridge, MA. In this talk, Dan focused on the security of embedded devices and the fast-emerging Internet of Things. (A full transcript of the talk is available here.) “The embedded systems space, already bigger than what is normally thought of as […]
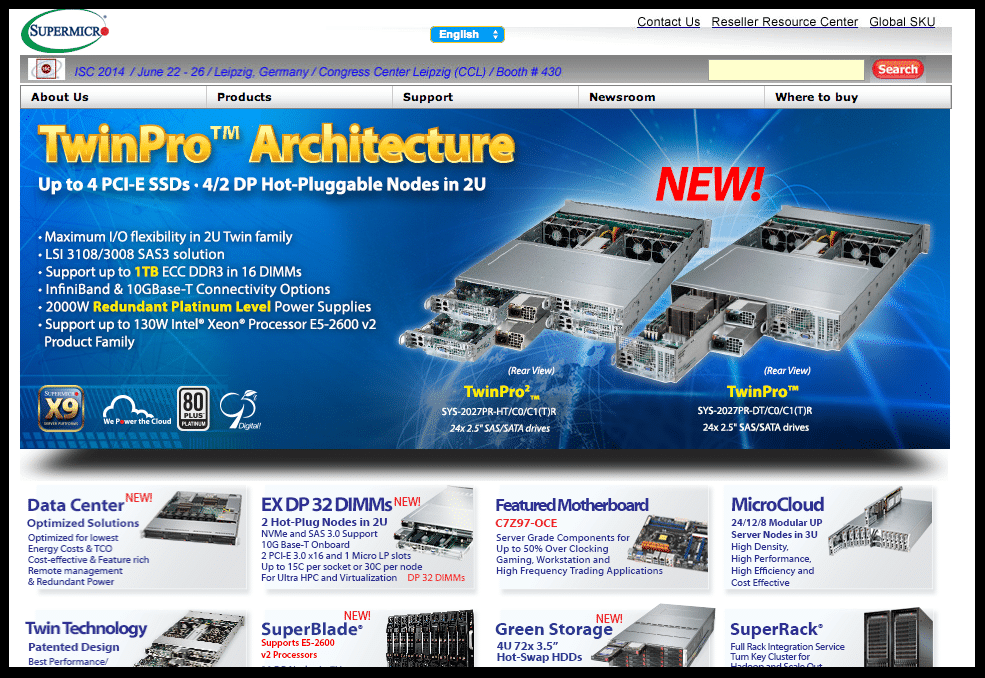
Update: Another IPMI Mishap? Researcher Claims Supermicro Devices Vulnerable
There’s more bad news for companies that rely on the Intelligent Platform Management Interface (IPMI) to manage servers and other hardware in their IT environments. Specifically: researcher Zachary Wikholm over at Cari.net has published evidence of what he says is a head-slapping vulnerability affecting devices that use IPMI Base Management Controllers (BMCs) made by the firm SuperMicro. According to Wikholm, servers equipped with Supermicro BMCs store a password file, PSBlock, in plain text and – making matters worse- leave it open to the world on port 49152. “You can quite literally download the BMC password file from any UPnP enabled Supermicro motherboard running IPMI on a public interface,” he wrote. Baseboard Management Controllers (BMCs) are small, embedded systems attached to a system’s motherboard that manage IPMI communications. Wikholm says that Supermicro has fixed the problem in the latest version of its IPMI firmware. However, companies are often reluctant to flash […]