We speak with Ravi Iyer, the Head of Product Management talks to us about the “democratization” of software development, as more and more companies become software publishers. Ravi and I talk about Polaris, a new software integrity platform that integrates a wide range of software testing and analysis tools into a common platform.
application security
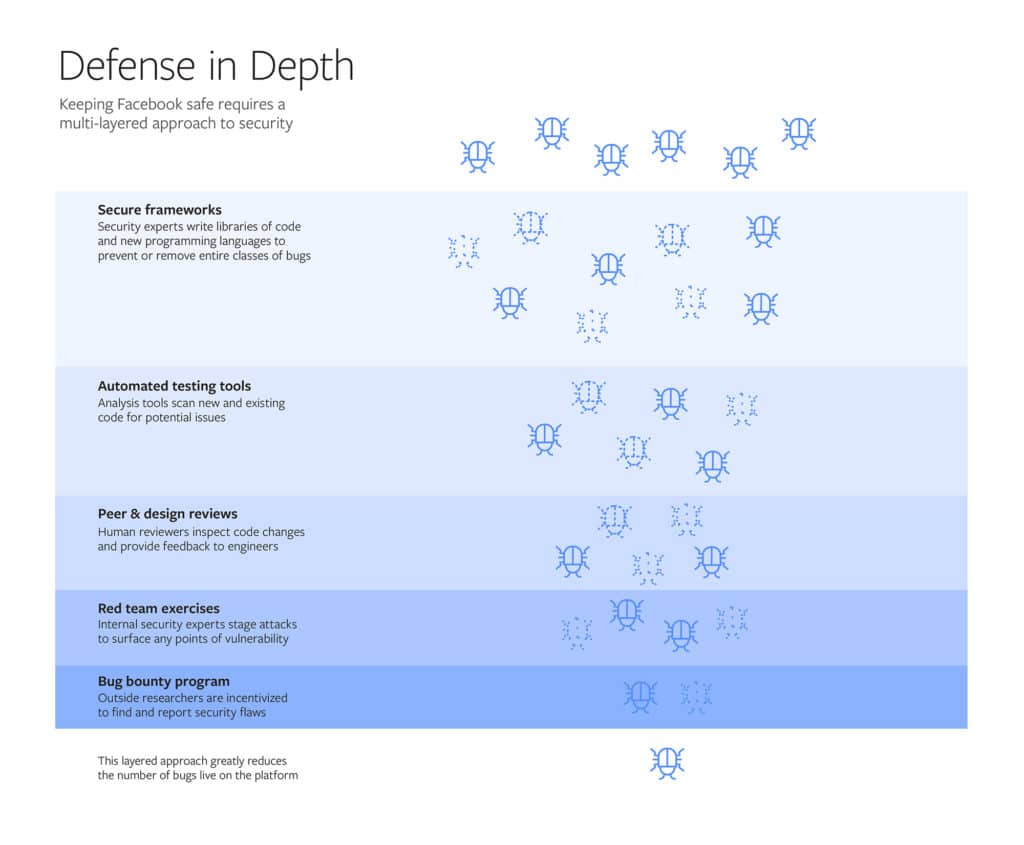
Facebook opens up on System that ‘protects Billions’
Facebook used a blog post on Friday to describe, in detail, the systems that it uses to secure its vast social network, including custom designed tools and so-called “red team” hacks.
Massive Facebook Breach Affects 90 Million Accounts
Facebook forced a reset of more than 50 million user accounts on Thursday and would force another 40 million account resets in the coming days, citing a major breach of the site’s security that allowed unknown attackers to take over people’s accounts.
From Mainframes to Connected Cars: How Software drives the Automotive Industry
Automakers must pay as much attention to the integrity and security of the software running modern vehicles as they pay to areas such as metallurgy, impact protection, seat belts, and materials science argues Gary Mcgraw, the Vice President of Security Technology at the firm Synopsis.
Special Black Hat Coverage: Google’s Parisa Tabriz Says Don’t Be A Jerk
In this special Black Hat edition of the Podcast, sponsored by UL: Parisa Tabriz, Google’s Director of Engineering for the Chrome Web browser, brought some strong medicine to Las Vegas for her Black Hat keynote speech. We talk about why her simple message was so groundbreaking. Also: Ken Modeste of UL joins us from the Black Hat briefings to talk about UL’s efforts to make cyber security as important to consumers in the 21st century as product safety was in the 20th.