Security researcher and IoT hacker Dennis Giese talks about his mission to liberate robot vacuums from the control of their manufacturers, letting owners tinker with their own devices and – importantly – control the data they collect about our most intimate surroundings.
networking
Why digital certificates are critical to 5G security
As 5G gains traction, service providers need to be able to trust their networks’ security to truly take advantage of 5G’s capabilities. Digital certificates are critical to that, writes Alexa Tahan of Nokia.
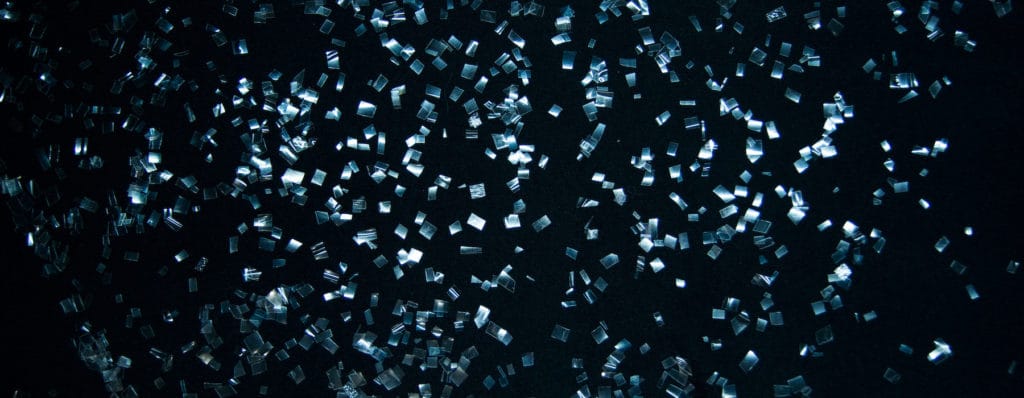
Spotlight: ShardSecure on Protecting Data At Rest Without Encryption
Host Paul Roberts speaks with Marc Blackmer of ShardSecure about that company’s new approach to protecting data at rest, which relies on fragmenting and scattering data to make it impossible to steal.
At Pride Summit: A Warning On Cyber Literacy
Poor cyber literacy is at the root of many of the cybersecurity problems plaguing the U.S. economy, according to Dr. Alissa Abdullah, Deputy CSO at MasterCard.
Episode 216: Signed, Sealed and Delivered: The Future of Supply Chain Security
In this episode of the podcast
(#216) we talk with Brian Trzupek, Digicert’s Vice President of Product, about the growing urgency of securing software supply chains, and how digital code signing can help prevent compromises like the recent hack of the firm SolarWinds.