In this Spotlight Podcast, sponsored by Trusted Computing Group*, Dennis Mattoon of Microsoft Research gives us the low-down on DICE: the Device Identifier Composition Engine Architectures, which provides a means of solving a range of security and identity problems on low cost, low power IoT endpoints. Among them: establishing strong device identity, doing device attestation and safe deployment at scale and verifying software updates.
sensor
Episode 81: Hacking IoT with Physics, Poor Grades for Safety Wearables and Peak Ransomware
In this week’s podcast: researcher Kevin Fu of University of Michigan discusses his work on attacks that use physics to manipulate connected devices. Also: Mark Loveless of DUO discusses his research into how poor implementation of wireless protocols make personal security trackers a privacy risk. And have we seen peak ransomware? Adam Kujawa of the firm Malwarebytes joins us to talk about the findings of that company’s State of Malware Report.
Researchers Warn of Physics-Based Attacks on Sensors
Billions of sensors that are already deployed lack protections against attacks that manipulate the physical properties of devices to cause sensors and embedded devices to malfunction, researchers working in the U.S. and China have warned.
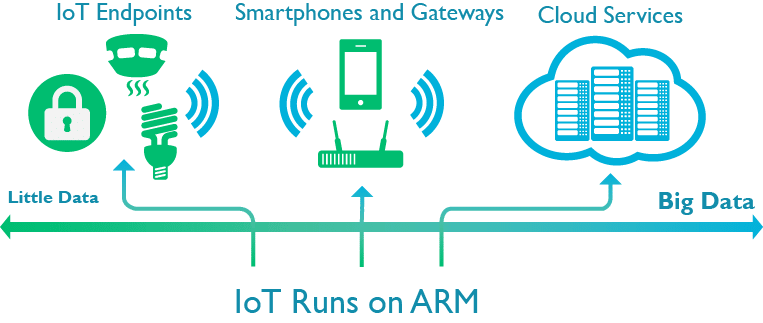
With an Eye on IoT Security ARM buys Simulity for $15m
In-brief: ARM’s purchase of Simulity adds the ability to do over the air updates to embedded SIM chips and highlights ARM’s efforts to build out security and management at IoT scale.
Identity at Scale: how the Internet of Things will Revolutionize Online Identity
In-brief: Far from ‘breaking’ the public key encryption (PKI) model, the Internet of Things is poised to turbocharge PKI adoption and revolutionize online identity, DigiCert CTO Dan Timpson writes.