Tanya Janca of the group We Hack Purple, talks with Security Ledger host Paul Roberts about the biggest security mistakes that DevSecOps teams make, and application development’s “tragedy of the commons,” as more and more development teams lean on open source code.
penetration testing
Is a DEF CON Village the right way to assess AI risk?
The AI industry is pointing to the AI Village at DEF CON as a venue for assessing cybersecurity risk. But is a “village” the best way to test AI risk? Experts have their doubts.
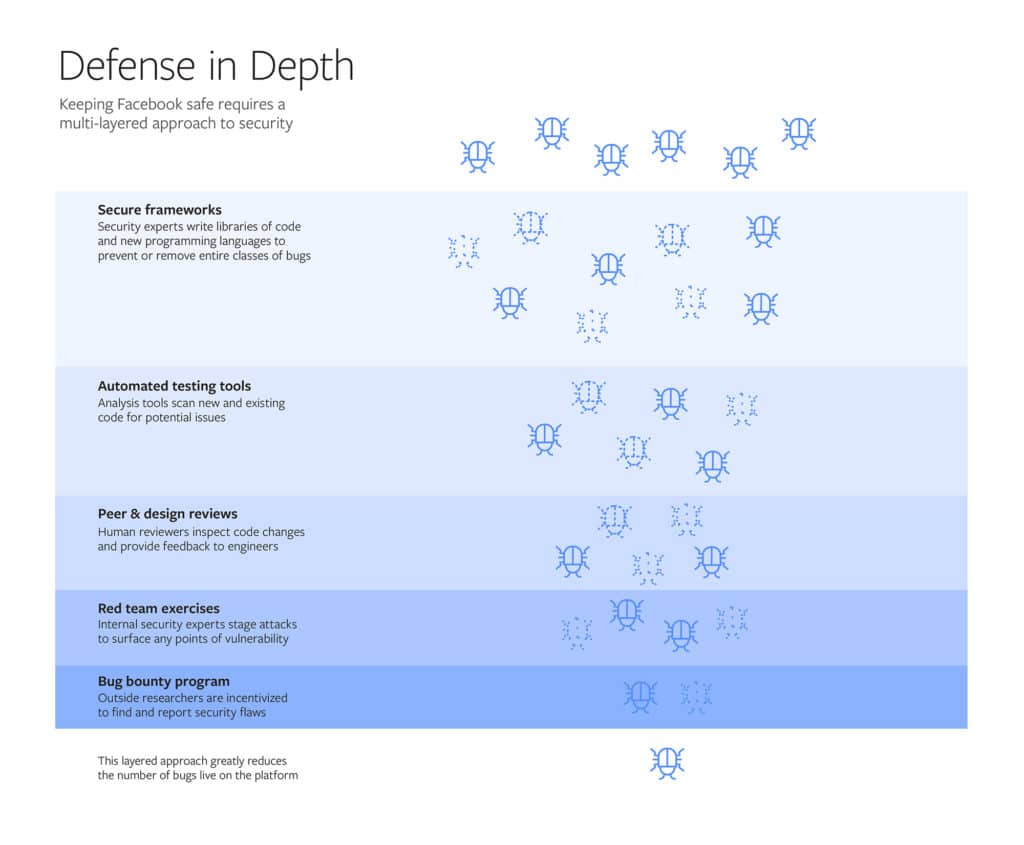
Facebook opens up on System that ‘protects Billions’
Facebook used a blog post on Friday to describe, in detail, the systems that it uses to secure its vast social network, including custom designed tools and so-called “red team” hacks.
Podcast Episode 122: will 5G increase Internet of Things Risk?
Telecommunications firms like to talk up all the great things that so-called 5G cellular networks will bring to smart phones. But what new kinds of Internet of Things use cases may become possible? And, just as important, what are the security implications of massively distributed IoT endpoints connected to capacious 5G cellular infrastructure? Jason Ortiz of the cybersecurity services firm Pondurance joins us to talk about the impact of 5G on the IoT.
From Mainframes to Connected Cars: How Software drives the Automotive Industry
Automakers must pay as much attention to the integrity and security of the software running modern vehicles as they pay to areas such as metallurgy, impact protection, seat belts, and materials science argues Gary Mcgraw, the Vice President of Security Technology at the firm Synopsis.