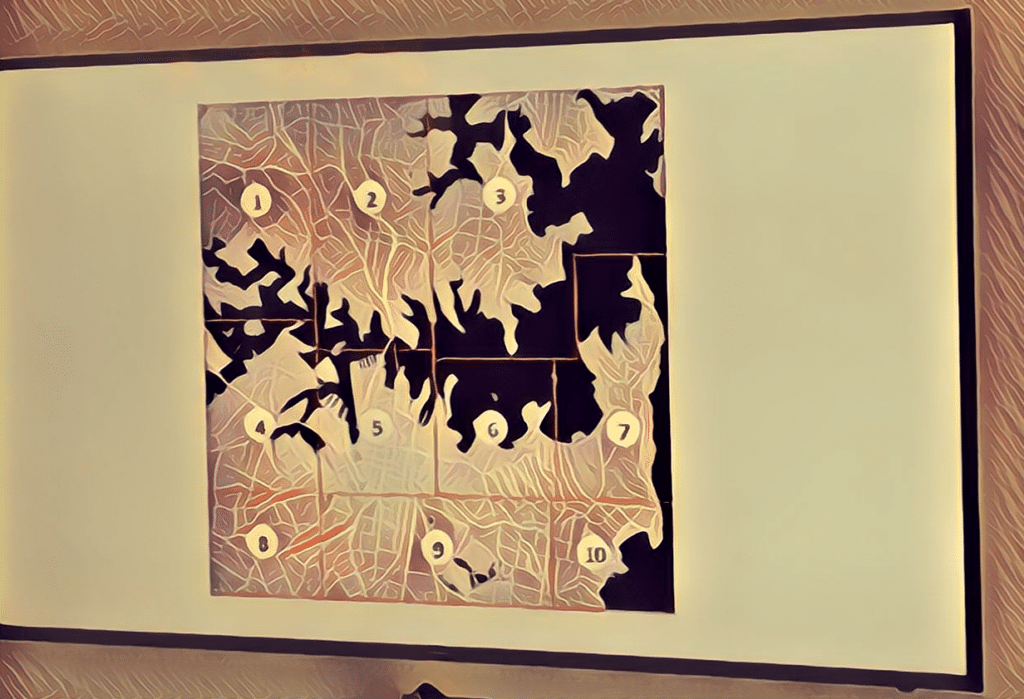
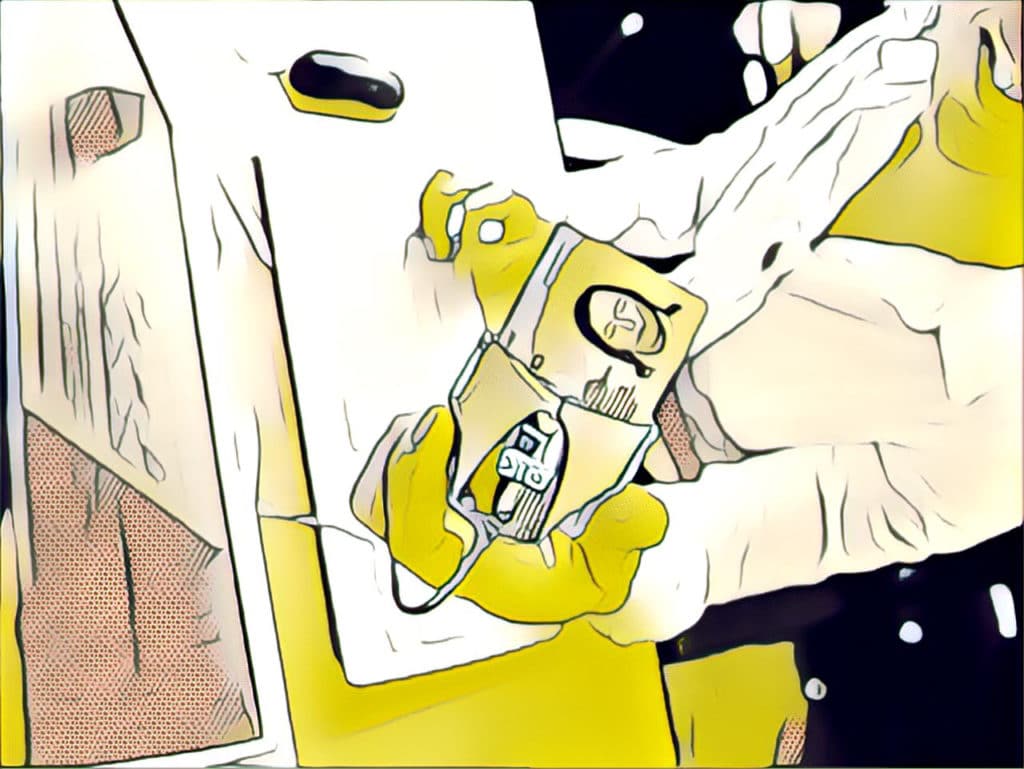
A new study by the firm Interos found that many hardware components in a popular touchscreen voting machine used in the U.S. originate in China or Russia.
voting
Podcast Episode 113: SAP CSO Justin Somaini and Election Hacks – No Voting Machines Required!
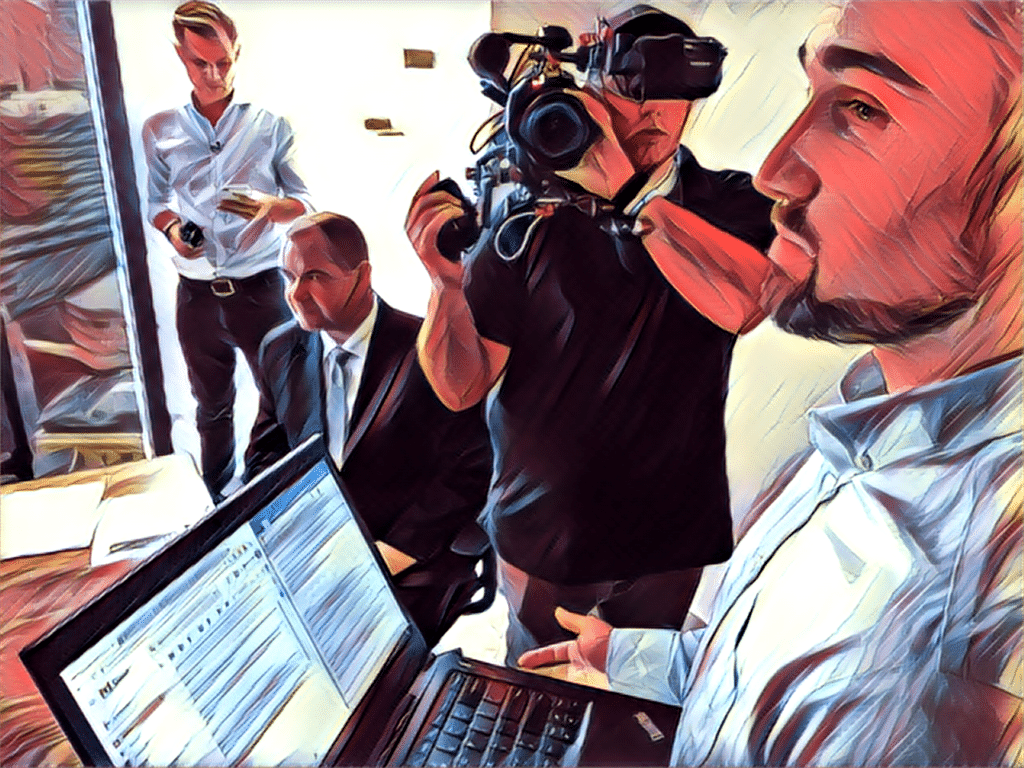
Everybody worries about hacked voting machines. But an exercise in Boston last week showed how hackers can compromise the vote without ever touching an election system. Also: October is just around the corner and that means Cyber Security Awareness Month is upon us. So what are top cyber security professionals “aware of” these days? We talk with Justin Somaini the Chief Security Officer at SAP to find out.
In Boston Exercise, Election Hackers Bypass Voting Machines
At an exercise in Boston that imagined a cyber attack designed to disrupt an important election in a “swing state,” voting machines were not an issue.
Opinion: The Corporate Lessons of Election Hacks
Recent demonstrations of election hacks are about more than ballots. They also contain important lessons for enterprises, Security Ledger Editor in Chief Paul Roberts argues in this opinion piece. (Note: this post first appeared on Hitachi Systems Security* web site.)
Episode 100: Estonia’s Former CIO talks about engineering a secure electronic vote
In this week’s episode of The Security Ledger Podcast (#100 – woot!): Taavi Kotka spent 4 years as the Chief Information officer for the nation of Estonia – whose government is widely recognized as among the most technologically advanced in the world. He talks about the Estonian model for e-governance and how the U.S. has ruined the term “e-voting” for everyone. Also: what happens when discussions about the security of bits and bytes have consequences measured in flesh and blood? Joshua Corman, the Chief Security Officer at the firm PTC joins us to talk about it, ahead of his featured presentation at next week’s Security of Things Forum in Boston.