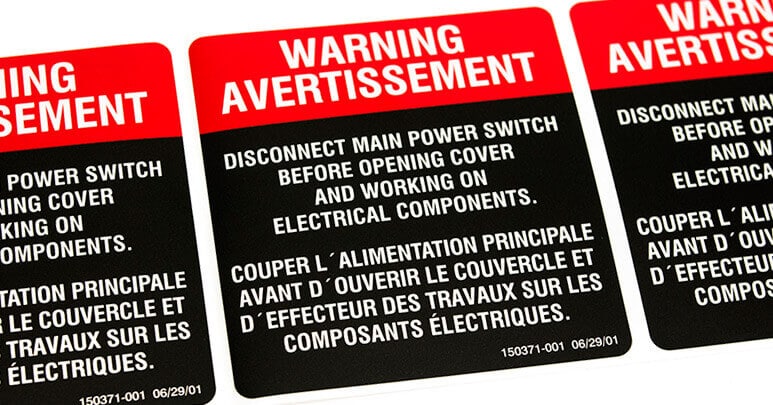
The web site EurActiv.com is reporting that the European Commission (EC) is getting ready to propose new legislation to protect machines from cybersecurity breaches. Among the steps they’re considering: labels for Internet-connected devices that tell consumers they are “approved and secure.” Products across industries from energy and consumer goods to automotive and healthcare could eventually be required to use the labels on their products, just as electrical devices currently contain labels that inform consumers how much power they use, EU officials said. Digital policy chiefs Günther Oettinger and Andrus Ansip presented a plan three weeks ago to speed up internet connections to meet the needs of big industries like car manufacturing and agriculture as they gradually use more internet functions. But lawmakers recognize that the transition to more and faster internet connections has caused many companies to worry that new products and industrial tools that rely on the internet will be more vulnerable […]
European Parliament
Brexit: A Cybersecurity Perspective | ABI Research
In-brief: The UK’s decision to leave the EU will have vast implications in the area of information security: from the standing of laws governing cyber crime and e-commerce to the decisions made by information security and technology firms that use the UK as their base for EU Operations, according to an analysis by ABI Research.
Internet of Things Demands New Social Contract To Protect Privacy
Changes brought about by the Internet of Things demands the creation of a whole new social contract to enshrine the right to privacy and prevent the creation of technology-fueled Orwellian surveillance states in which individual privacy protections take a back seat to security and “control.” That, according to an opinion piece penned by the head of the European Commission’s Knowledge Sharing Unit. Gérald Santucci, in an essay written for the web site privacysurgeon.org, argues that technology advances, including the advent of wearable technology and the combination of inexpensive, remote sensors and Big Data analytics threaten to undermine long-held notions like personal privacy and the rights of individuals. The essays says that current approaches to data protection are “largely inadequate” to the task of reigning in the asymmetrical changes wrought by new technology. “Data collection and video surveillance will continue to grow as ubiquitous computing pervades almost all areas of our […]