In this Spotlight podcast interview, David Monnier of Team Cymru talks about the evolution of the threat intelligence into actionable and target specific “threat reconnaissance.”
Team Cymru
The Future of Attack Surface Management: How to Prepare
Upwards of 70% of organizations have been compromised because of an unknown, unmanaged, or mismanaged visible asset. Improving your Attack Surface Management capabilities is critical, says David Monnier, a Fellow at Team Cymru.
Vigilante botnet highlights woeful state of embedded device security
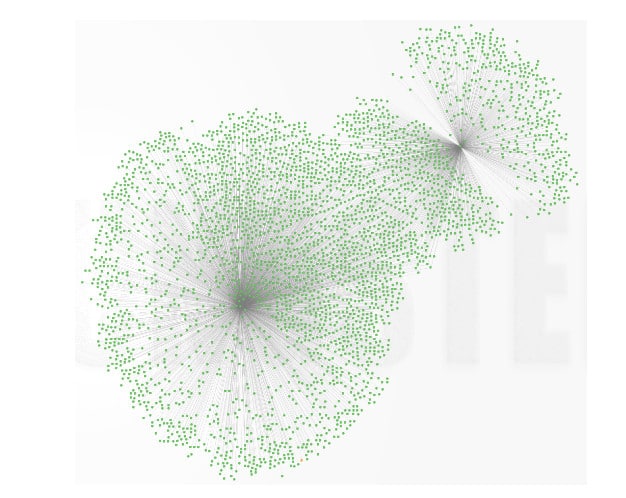
A mysterious piece of software, dubbed Wifatch, has been infecting tens of thousands of Linux-based home routers and, according to experts at Symantec, attempts to secure them from attack. But Wifatch’s benevolent intentions shouldn’t obscure its malicious actions, or the security problems that it takes advantage of. The malicious software runs on vulnerable, Linux-based home routers. There, it removes other malware infections, disables vulnerable services like Telnet and even prompts users to update their administrator user name and password to prevent compromise, according to a post on Symantec’s blog. But the malware is still spreading between vulnerable systems without the owners consent and could easily be pressed into service distributing spam or malicious software, experts note. According to Symantec, Wifatch is likely spreading between infected devices by targeting exposed Telnet interfaces and using brute force password attacks to gain access to the devices. Tens of thousands of devices may have been infected […]
EFF wants to make Wi-Fi routers more secure | theguardian.com
Home routers and wi-fi access points are the canaries in the coal mine for security on the Internet of Things. Simply put: they’re ubiquitous, Internet-connected and innocuous. Unlike mobile phones, wi-fi routers aren’t in your pocket – buzzing and ringing and demanding your attention. In fact, it’s safe to be that the vast majority of Internet users are concerned wouldn’t know how to connect- and log in to their router if they had to. But appearances can deceive. Broadband routers are, indeed, mini computers that run a fully featured operating system and are perfectly capable of being attacked, compromised and manipulated. We have already seen examples of modern malware spreading between these devices. In March, the security firm Team Cymru published a report (PDF) describing what it claimed was a compromise of 300,000 small office and home office (SOHO) wireless routers that was linked to cyber criminal campaigns targeting online banking customers. In January, […]
Heartbleed: Technology Monoculture’s Second Act
Say ‘technology monoculture’ and most people (who don’t look at you cross-eyed or say ‘God bless you!’) will say “Microsoft” or “Windows” or “Microsoft Windows.” That makes sense. Windows still runs on more than 90% of all desktop systems, long after Redmond’s star is rumored to have dimmed next to that of Apple. Microsoft is the poster child for the dangers and benefits of a monoculture. Hardware makers and application developers have a single platform to write to – consumers have confidence that the software and hardware they buy will “just work” so long as they’re running some version of Windows. The downside, of course, is that the Windows monoculture has also been a boon to bad guys, who can tailor exploits to one operating system or associated application (Office, Internet Explorer) and be confident that 9 of 10 systems their malicious software encounters will at least be running some version of the […]