In-brief: President Barack Obama highlighted cyber security as a top policy priority in the final budget proposal of his presidency, seeking a massive expansion in funding for federal information security and the creation of a new federal chief information security officer (CISO).
Sony
With Executive Order, Cyber Criminals Join Terrorists, Traffickers on Sanctions List
In-brief: An Executive Order signed by President Obama on Wednesday will clear the way for cyber criminals to face the same sanctions as terrorist groups, illegal arms dealers and drug traffickers. One expert called the Order “momentous.”
Report: Chaos of Sony Response Prompts Creation of New Cyber Agency | The Washington Post
In-brief: The Washington Post reports that the Obama Administration will announce the creation of a new agency to coordinate intelligence about cyber attacks. The move is, in part, a response to confusion following the hack of Sony Pictures Entertainment in November.
White House Backs Raft of New Cyber Security Laws
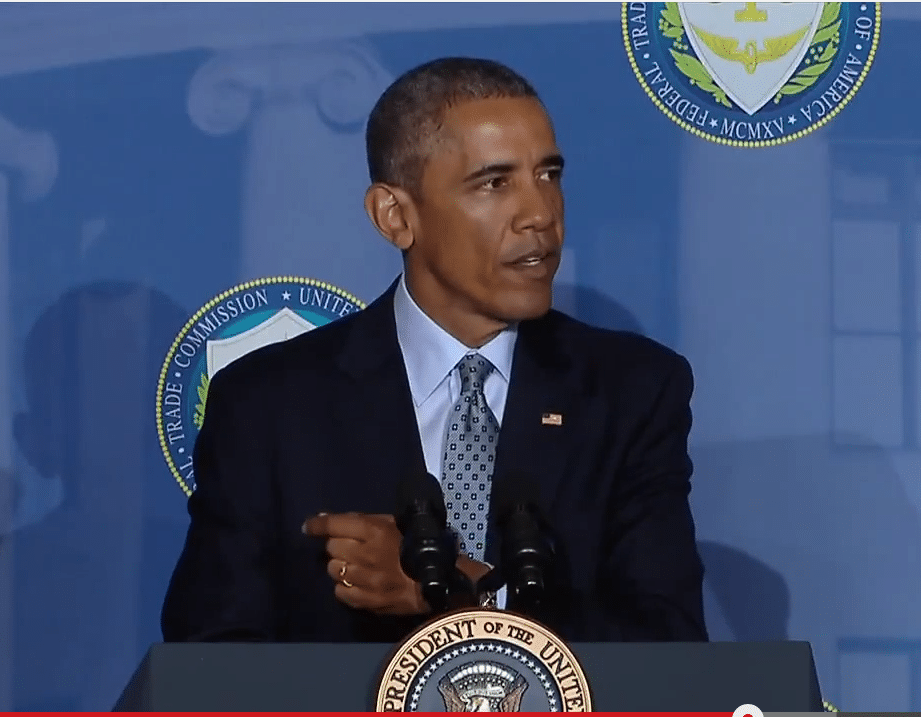
President Obama used a speech at the Federal Trade Commission on Monday to call for a raft of new laws and reforms that would protect the privacy and online security of U.S. citizens and corporations. Speaking at the FTC, President Obama highlighted a number of policies that he will propose in his State of the Union address to Congress. They include new laws aimed at endemic problems like identity theft and online tracking of consumer behavior. The visit was notable for being the first time a sitting President has visited the FTC in 80 years, since 1937 and the administration of Franklin D. Roosevelt. Obama, who has been highlighting issues and ideas he will unveil in his State of the Union Address, said the address is one of a series of talks he will give this week focused on computer and online privacy. The President said he will follow his speech aimed at […]
Sony: A Game Changer for Cyber Attribution
We’ve been writing a lot about the issue of cyber attribution in recent weeks, following the attack on Sony Pictures Entertainment in November. That incident has become something of a Rorschach Test for those in the information security field: revealing as much about the individual attempting to explain the Sony hack as about the attack itself. Rid and a Ph.D student, Ben Buchanan, have authored a paper in the Journal of Strategic Studies. In their paper, Rid and Buchanan note that one of the biggest challenges of cyber attribution: bridging the technical and political or cultural issues that often surround cyber attribution. As Rid notes: the individuals doing the basic forensic work on the incident may not have a grasp of the larger cultural or political issues at play. That’s a dynamic we’ve seen at play (in spades) in recent news about the hack of Sony Pictures. In this podcast, Rid […]