The Consumer Electronics Show – or CES- kicked off last week in Las Vegas. In the last decade, CES has become one of the premiere venues for consumer device makers to launch new products and to show off prototypes of technology they hope to introduce to the public. Home entertainment megafauna dominate the coverage of CES — there was Samsung’s 85-inch LED LCD model with 4K resolution that can transform from flat-screen to curved display. But this year’s show is also a showcase for the next wave of connected devices, including wearable technology, smart appliances and connected vehicles. All these new platforms raise important questions about security, privacy and reliability. I sat down to talk about some of those issues with Mark Stanislav, the lead security evangelist at the firm Duo Security. Mark is a frequent contributor to The Security Ledger who last joined us to provide an end of year […]
Duo Security
Welcoming A New Sponsor: Duo Security
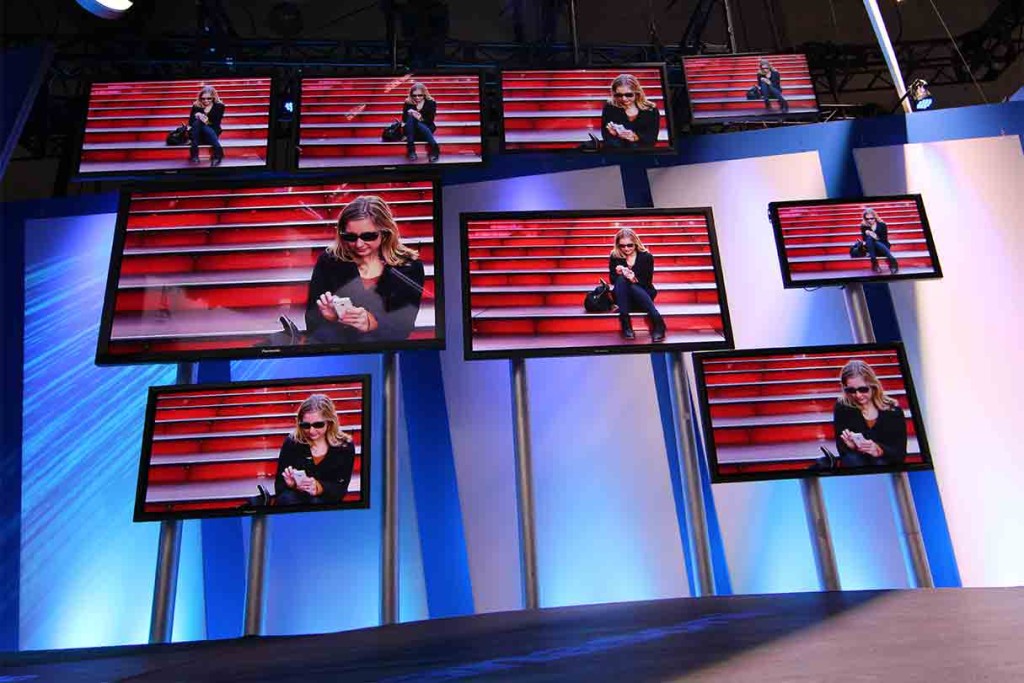
Those of you who pay close attention to The Security Ledger may have noticed some new artwork gracing our home page in recent days. It is with great pleasure that I note the addition of our newest sponsor: Duo Security Inc., a maker of two-factor authentication technology. I followed Duo from its earliest days, but my interactions with the company picked up after last year’s RSA Conference in San Francisco, when I had the chance to get briefed by CEO Dug Song about the company’s technology and how Duo was leveraging consumer-driven trends like BYOD (bring your own device) to solve vexing enterprise identity and authentication problems. Duo, which is based in Ann Arbor, Michigan, sells a hosted two-factor authentication service that leverages the cloud and mobile devices to provide a secure login experience using something you know (a password) and something you hold (a mobile phone). The Duo platform […]
What Will 2014 Bring For Internet of Things? Some Thoughts.
As we’ve noted before, The Internet of Things is figuring prominently in both year-end round ups and year-end predictions. Many technology pundits saying that the IoT and security issues related to Internet-connected devices will be a major trend to watch this year. Here are some interesting takes on what 2014 holds for The Internet of Things. Better Design (Wired) While superbly designed products like the NEST Thermostat get much of the attention when folks talk about the potential of The Internet of Things, good design isn’t a prerequisite for making a “smart” device – nor is it even that common in the nascent IoT, as a casual reading of some of our coverage will show you. But good design – or at least better design – that includes robust security will be necessary if the IoT market is to mature. That’s the argument Jermoe Nadel makes in this article on […]
Prediction: Rough Road Ahead in 2014 For Security and Internet of Things
With the New Year fast approaching, it’s (unofficially) ‘prediction season,’ when everyone worth their salt stares into the crystal ball and tries to imagine what the world will look like 12 months hence. To sort through our 2014 predictions, we called on Mark Stanislav, the chief Security Evangelist at Duo Security. Mark is a seasoned security researcher who has taken an interest in the security of the Internet of Things. Earlier this year, we wrote about research Mark did on the IZON Camera, an IP-enabled home surveillance camera that is sold by big-box retail stores like Best Buy, as well as by the Apple Store. Beneath the IZON’s polished exterior, the IZON was a mess of sloppy coding and poor security implementation, Stanislav discovered. Like many IoT devices, IZON cameras punted security to those responsible for the wireless network that it was deployed on – essentially trusting any connection from […]
For SANS Critical Controls: Authentication Missing In Action
Authentication is the gateway to privilege and authorization. Consider how many portions of your life, digital and otherwise, revolve around authentication. Whether you want to do Internet banking, tweet a friend, or buy a present, some sort of authentication likely occurred to allow you to do so. But when it comes to one of the most widely used sources of advice for organizations to improve their security, authentication is absent. I’m speaking about The SANS Institute’s “20 Critical Security Controls.” This list represents a great public-private partnership effort with SANS, the Center for Internet Security, and Center for Strategic and International Studies all involved in its production and maintenance. The goal of the document is to help provide organized guidance and actionable improvements for organizations wanting to strengthen their security posture. Because of the separation of subject matter into individual control areas, the document is quite useful at conveying […]