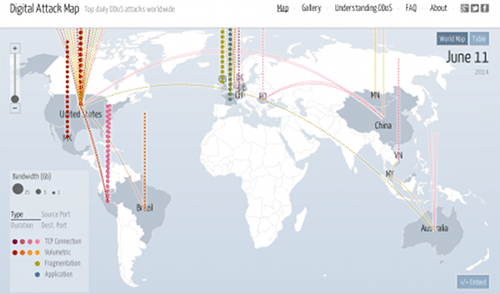
Large-scale attacks knocked two prominent, web-based services offline late Tuesday, as cyber criminals attempted extort money from the owners of news aggregation site Feedly and the hosted productivity tool Evernote. Feedly – a web site that pulls together news feeds from across the web – remained unreachable early Wednesday, while Evernote was back online. Both companies issued statements confirming that they were the victims of a massive distributed denial of service (DDoS) attack. “We’re actively working to neutralize a denial of service attack. You may experience problems accessing your Evernote while we resolve this,” read a message sent from Evernote’s Twitter account Tuesday evening at around 8:00 PM Eastern Time. And, around 5:00 AM Eastern on Wednesday, Feedly posted a blog entry that reads: “Criminals are attacking feedly (sp) with a distributed denial of service attack (DDoS). The attacker is trying to extort us money to make it stop. We refused to give […]
Arbor
History Suggests Heartbleed Will Continue To Beat
The SANS Internet Storm Center dialed down the panic on Monday, resetting the Infocon to “Green” and citing the increased awareness of the critical OpenSSL vulnerability known as Heartbleed as the reason. Still, the drumbeat of news about a serious vulnerability in the OpenSSL encryption software continued this week. Among the large-font headlines: tens of millions of Android mobile devices running version 4.1 of that mobile operating system (or “Jelly Bean”) use a vulnerable version of the OpenSSL software. Also: more infrastructure and web application players announced patches to address the Heartbleed vulnerability. They include virtualization software vendor VMWare, as well as cloud-based file sharing service Box. If history is any guide: at some point in the next week or two, the drumbeat will soften and, eventually, go silent or nearly so. But that hardly means the Heartbleed problem has gone away. In fact, if Heartbleed follows the same […]
Update: Retail Breaches Spread. Point of Sale Malware A Suspect.
Reuters is reporting on Monday that the recently disclosed hack of box store retailer Target Inc. was just one of a series of attacks against U.S. retailers, including Target, the luxury department store Neiman Marcus and other, as-yet-unnamed companies.* The story adds to other, recent revelations, including the breach at Neiman Marcus, which was first disclosed by the security blog Krebsonsecurity.com on Friday. Also on Monday, Target CEO Gregg Steinhafel confirmed that his company was the victim of malicious software installed on point of sale (PoS) systems at the store. According to the Reuters report, Target Corp and Neiman Marcus are just two retailers whose networks were breached over the holiday shopping season. The story cites unnamed sources “familiar with attacks,” which have yet to be publicly disclosed. Breaches of “at least three other well-known U.S. retailers took place and were conducted using similar techniques as the one on Target,” according […]
Welcoming A New Sponsor: Duo Security
Those of you who pay close attention to The Security Ledger may have noticed some new artwork gracing our home page in recent days. It is with great pleasure that I note the addition of our newest sponsor: Duo Security Inc., a maker of two-factor authentication technology. I followed Duo from its earliest days, but my interactions with the company picked up after last year’s RSA Conference in San Francisco, when I had the chance to get briefed by CEO Dug Song about the company’s technology and how Duo was leveraging consumer-driven trends like BYOD (bring your own device) to solve vexing enterprise identity and authentication problems. Duo, which is based in Ann Arbor, Michigan, sells a hosted two-factor authentication service that leverages the cloud and mobile devices to provide a secure login experience using something you know (a password) and something you hold (a mobile phone). The Duo platform […]
US CERT Warns About Point-of-Sale Malware
With news of the breach of big-box retailer Target Inc. still in the headlines, the U.S. Computer Emergency Readiness Team (CERT) issued a warning about the danger posed by malicious software targeting Point of Sale (POS) systems. CERT issued an advisory (TA14-002A) on Thursday asking POS owners to take steps to secure the devices, and telling consumers to beware. The warning comes after a string of reports that suggest that malware attacking point of sale systems is on the rise. In December, researchers from Arbor Networks said they had detected an “active PoS compromise campaign” to steal credit and debit card data that used the Dexter and Project Hook malware. Dexter is a Windows-based program that was first discovered in December, 2012 by Seculert, an Israeli security firm. It is still not known whether malware played a part in the huge theft of credit card data from Target Inc. That […]