In this episode of the Security Ledger Podcast, Paul speaks with Jill Moné-Corallo, the Director of Product Security Engineering Response at GitHub. Jill talks about her journey from a college stint working at Apple’s Genius bar, to the information security space – first at product security at Apple and now at GitHub, a massive development platform that is increasingly in the crosshairs of sophisticated cyber criminals and nation-state actors.
Apple
Episode 183: Researcher Patrick Wardle talks Zoom 0days and Mac (in)Security
You just reported a major security vulnerability in the Zoom platform. Now the CEO of Zoom wants to chat…via Zoom. What do you do? Security researcher Patrick Wardle of Jamf joins us to talk about it, his recent Zoom 0day, the state of Mac (in)security and his hot date in Moscow.
Episode 160 Right to Repair’s Summer of Love – Sort of.
call it Right to Repair’s “Summer of Love.” Summer 2019 saw developments on a number of fronts in the nation-wide battle to win a digital right to repair. In this podcast, we talk with Nathan Proctor of US PIRG’s Right to Repair campaign and Kyle Wiens of iFixit about the developments.
More Questions as Expert Recreates Chinese Super Micro Hardware Hack
Though the companies named in a blockbuster Bloomberg story have denied that China hacked into Supermicro hardware that shipped to Amazon, Apple and nearly 30 other firms, a recent demonstration at hacking conference in Germany proves the plausibility of the alleged hack.
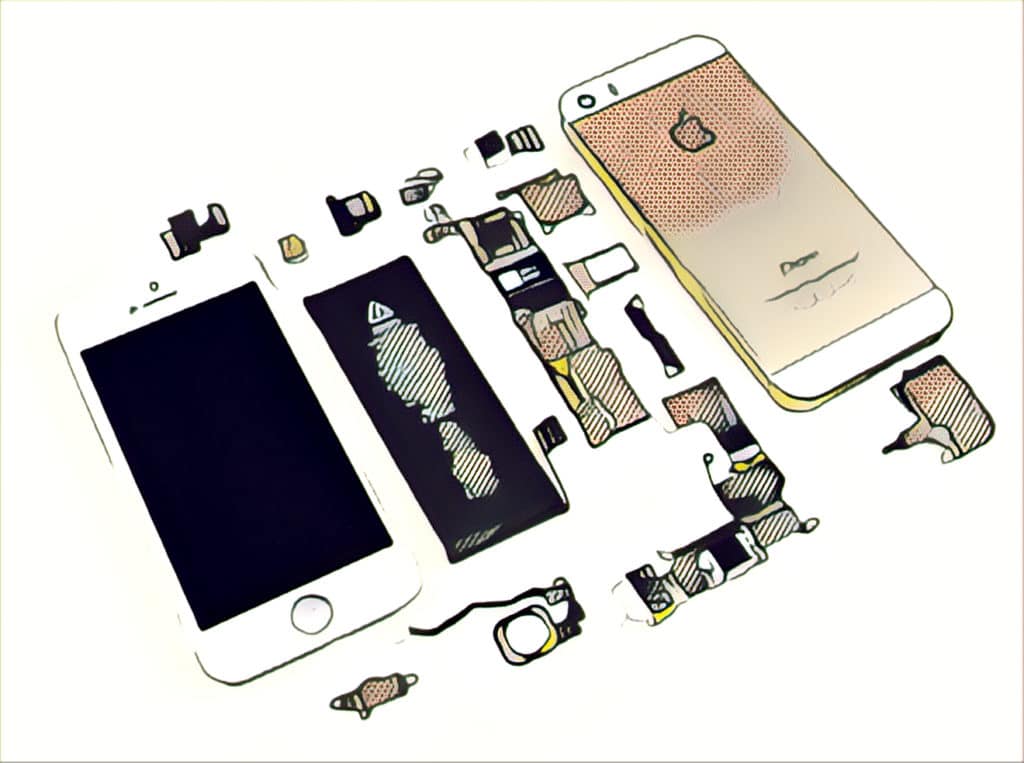
Apple Urges iPhone Users to Upgrade to Latest iOS Amid Cellebrite Unlock Claims
In-brief: Apple is urging iPhone and iPad users to upgrade to the latest version of iOS amid published claims by Israeli firm Cellebrite that its engineers can unlock basically any iPhone model, including those running the new iOS 11. Apple again finds itself at the center of controversy surrounding the ability to hack into iPhones to extract protected user information. The company is urging iPhone users to upgrade their devices to the latest version of iOS amid claims by an Israeli mobile-device surveillance firm that its engineers can unlock virtually any iPhone model in the world. However, the Cupertino, Calif.-based company is remaining mum on what, if anything, it might do now or in the future to resolve the issue. Citing anonymous sources, Forbes reported Monday that Cellebrite, based in Petah Tikva, Israel, is telling customers that its engineers already can bypass the security of devices running iOS 11, the […]