In-brief: Google is pushing an approach to network security dubbed “tiered access,” demoting the trusted password, which is now just one piece of data that is needed to get access to sensitive data and resources on Google’s network.
Tag: Google
When Cybercrooks Chat, Privacy isn’t Everything
In-brief: a survey of cyber criminal groups by Flashpoint revealed that secure messaging apps are becoming more popular, but that security isn’t the only thing motivating online criminals.
WiFi Chip Flaw in iPhone is Really Bad News for IoT
In-brief: a remotely exploitable flaw in a common hardware component used in phones by Apple, Samsung and others underscores the risk posed by software embedded in system on chip components that are found in almost every connected device, experts warn.
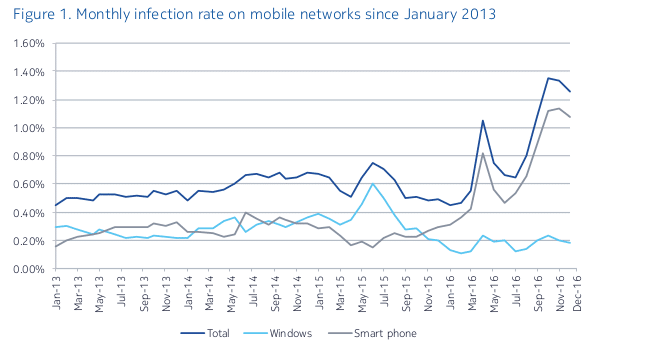
Android Malware Doubled in 2016, Adding to Mobile Malware Problem
In-brief: Smart phones infected with Android malware jumped 95 percent between 2015 and 2016, part of a steady increase in mobile phone infections in recent years, Nokia said on Monday.
Google Busts Symantec-Issued Certificates and Its a Big Mess
In-brief: Google’s rebuke of Symantec over its sloppy and problem-plagued certificate authority business risks upsetting some of the Internet’s biggest brands.