Now that authorities in Spain, Costa Rica and the U.S. have taken down online money transfer service Liberty Reserve, the cyber underground is facing a serious liquidity crunch, as criminal gangs, botmasters, spammers and malicious hackers look for a safe platform on which to transact business. But finding a ready substitute may not be easy, with Liberty Reserve’s close competitors showing less tolerance of its “no questions asked” account creation policy, and less scrupulous outlets wary of the long arm of the U.S. Justice Department. Liberty Reserve (libertyreserve.com) went offline on Friday along with dozens of other domains operated by its founder, Arthur Budovsky – a.k.a. “Arthur Belanchuk” a.k.a “Eric Paltz.” Budovsky was arrested in Spain on May 24th. Spanish authorities acted at the request of authorities in Costa Rica, where Budovsky had set up shop, and the U.S. A three-count criminal complaint filed there by the U.S. Attorney for the […]
Tag: FBI
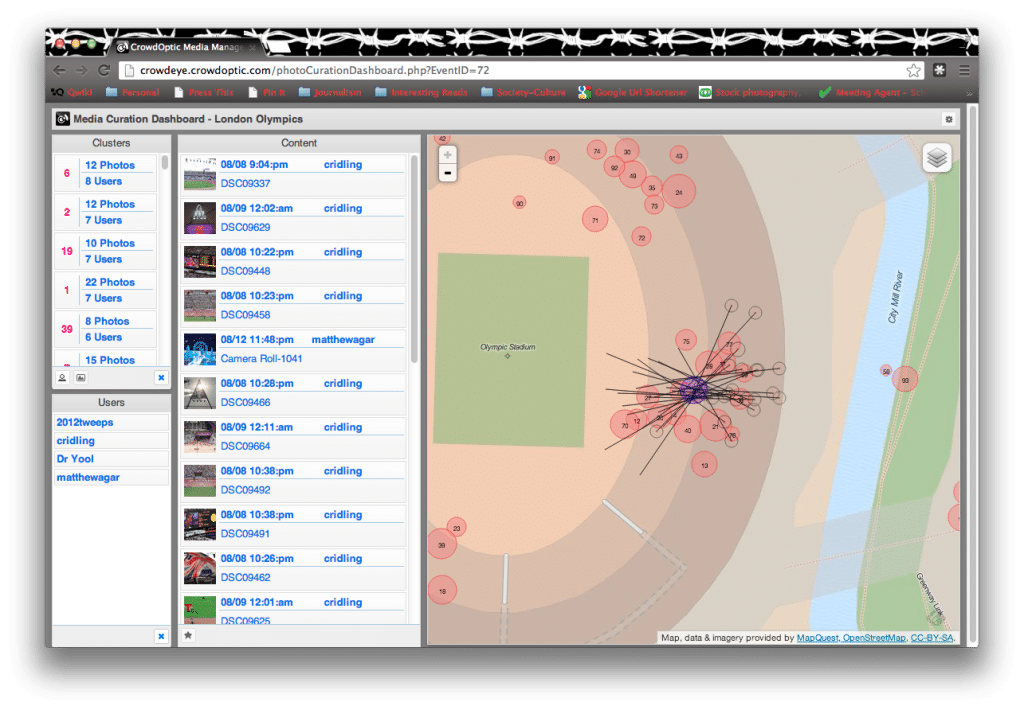
Meet The Software That Helped Catch The Boston Bombers
With one suspect in the Boston Marathon bombings dead and another on the run IN CUSTODY! the global, collective effort to identify those responsible for the crime has ended, and focus shifted to apprehending PROSECUTING Dzhokhor A. Tsarnaev, 19. He and his older brother, Tamerlan Tsarnaev, 26, were the subject of a massive manhunt, culminating in a firefight in the suburb of Watertown, Massachusetts, that killed the older Tsarnaev brother and set of a massive, daylong manhunt that shut down the metropolitan Boston area.(*) So how did crowdsourcing fare in the effort to catch the two? You’d have to say: not too well. High-profile collaborative efforts to crowdsource public images of the Boston Marathon bombing site, like those organized by the group 4Chan, assembled intriguing collections of material and clocked impressive pageviews (3.4 million and counting). In the end, those efforts yielded some clues: the type of clothing worn by the suspects, […]
Will Reddit Get Its Man? New Clues Come Fast As FBI Releases Boston Suspect Photos
The collective energies of a lot of pissed off people were given focus on Thursday, after the FBI released photos and a video of two men – identified as Suspect #1 and #2 – who were identified as the only suspects in the horrific bombing of The Boston Marathon on Monday. Within hours of releasing the photos, new clues to the identities of the suspects emerged on web sites like Reddit. Astute viewers flocked to the popular website Reddit.com to crowd source clues, with a special area or “subreddit,” dubbed “findbostonbombers” created to collect tips and analysis from the sea of fervent users. Their efforts paid off in short order, as contributors identified the brand of cap worn by both suspects (the white cap worn by Suspect #2 is believed to be by Ralph Lauren, while the black cap worn by Suspect #1 is believed to be a Bridgestone golf cap […]
Mobile Phone Use Patterns: The New Fingerprint
Mobile phone use may be a more accurate identifier of individuals than even their own fingerprints, according to research published on the web site of the scientific journal Nature. Scientists at MIT and the Université catholique de Louvain in Belgium analyzed 15 months of mobility data for 1.5 million individuals who the same mobile carrier. Their analysis, “Unique in the Crowd: the privacy bounds of human mobility” showed that data from just four, randomly chosen “spatio-temporal points” (for example, mobile device pings to carrier antennas) was enough to uniquely identify 95% of the individuals, based on their pattern of movement. Even with just two randomly chosen points, the researchers say they could uniquely characterize around half of the 1.5 million mobile phone users. The research has profound implications for privacy, suggesting that the use of mobile devices makes it impossible to remain anonymous – even without the use of tracking […]
Many Watering Holes, Targets In Hacks That Netted Facebook, Twitter and Apple
The attacks that compromised computer systems at Facebook, Twitter, Apple Corp. and Microsoft were part of a wide-ranging operation that relied on many “watering hole” web sites that attracted employees from prominent firms across the U.S., The Security Ledger has learned. The assailants responsible for the cyber attacks used at least two mobile application development sites as watering holes in addition to the one web site that has been disclosed: iPhoneDevSDK.com. Still other watering hole web sites used in the attack weren’t specific to mobile application developers – or even to software development. Still, they served almost identical attacks to employees of a wide range of target firms, across industries, including prominent auto manufacturers, U.S. government agencies and even a leading candy maker, according to sources with knowledge of the operation. More than a month after the attacks came to light, many details remain under tight wraps. Contacted by The Security […]