A school that never sleeps? Cameras that go dark? A dead company hacked back to life? Welcome to the growing Internet of Zombie devices that threatens the security of the Internet.
Tag: data privacy
Beware: Images, Video Shared on Signal Hang Around
A researcher is warning that photos and video files shared in Signal chats may be hanging around on devices, even when they deleted the messages in which the images were shared.
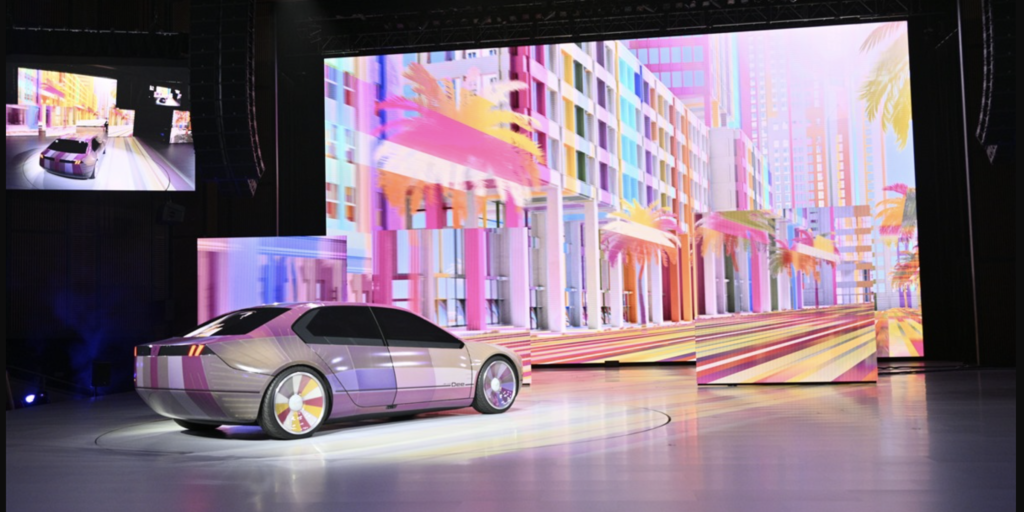
New Report Finds Auto Cyber Is A Dumpster Fire
Automakers swear that the security of their connected vehicles is their top priority. So how come researchers just found dozens of software flaws that could give hackers access to millions of cars?
Why digital certificates are critical to 5G security
As 5G gains traction, service providers need to be able to trust their networks’ security to truly take advantage of 5G’s capabilities. Digital certificates are critical to that, writes Alexa Tahan of Nokia.
The Future of IoT Security Standards
When it comes to measuring the security level of a device, a checklist of security ‘low hanging fruit’ is a good place to start. But more is needed, says Mike Sheward of Particle.io