Two separate attacks on banks in the United States and Pakistan revealed this week highlight once again the inherent weakness of a security practice that relies on passwords or knowledge-based credentials to protect critical information.
Tag: crime
Podcast Episode 88: Inside Russia’s DragonFly Group and How Cyber Crooks Launder Money
In this week’s Security Ledger Podcast (#88) we do a deep dive with researcher Vikram Thakur of the firm Symantec on “Dragonfly,” the Russian hacking group whose actions prompted the U.S. Department of Homeland Security and the FBI to issue a joint statement last week warning of intrusions into critical infrastructure in the US. Also: how do cyber criminals cash out all the loot they make from online scams? In our second segment we’ll talk to researcher Mike McGuire of the University of Surrey, who has been studying that question.
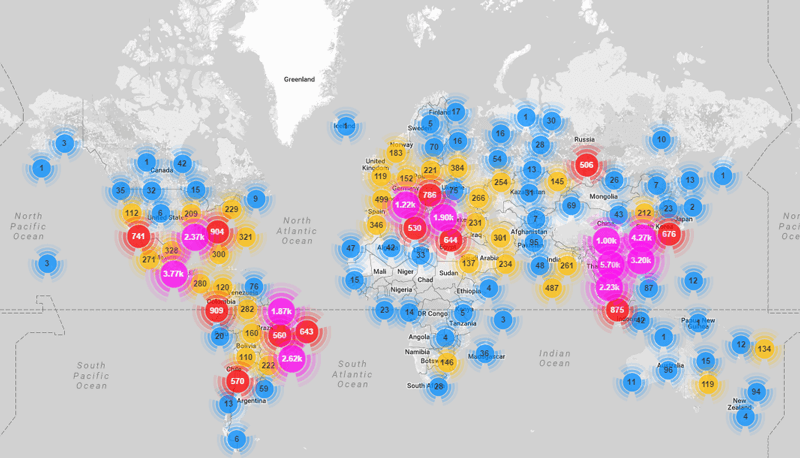
Cyber Criminals Launder Billions with Bitcoin, In-game Loot
Cyber criminals are laundering billions of ill-gotten gain using crypto currencies like Bitcoin and Monero and in-game currencies for popular online games like World of Warcraft, FIFA Soccer and Grand Theft Auto.
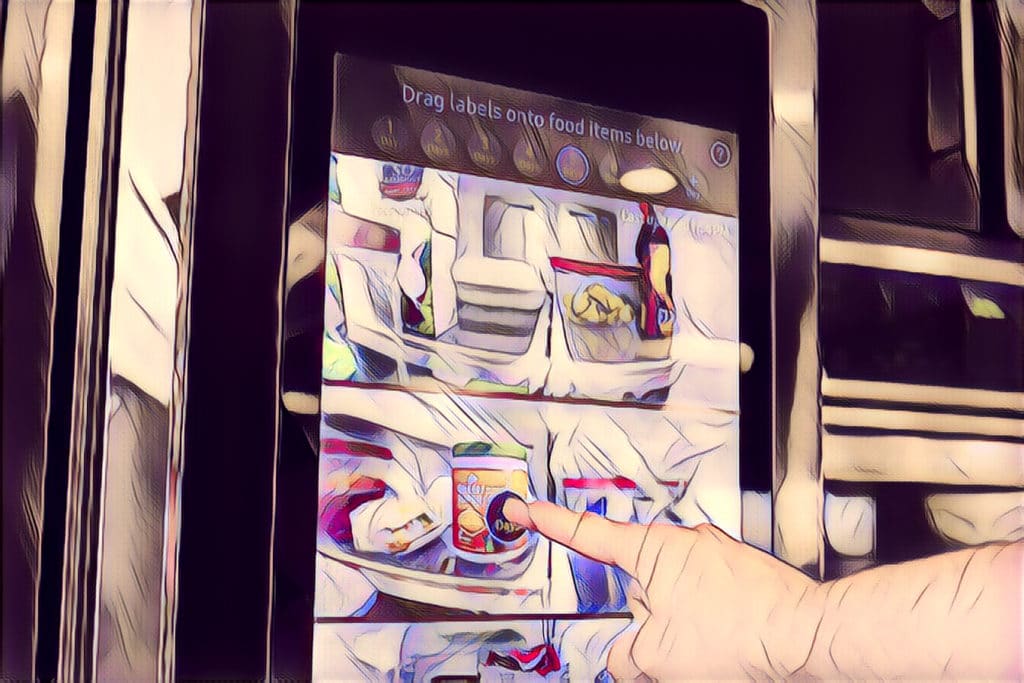
Smart Homes May Hide Crypto Mining Schemes
Loosely attended smart home appliances may be platforms for cryptocurrency mining scams, a researcher with the firm IOActive warns.
Mirai Botnet Authors Plead Guilty | Krebsonsecurity
Three men have pleaded guilty in U.S. federal court for their role creating and renting out the Mirai botnet, which launched damaging denial of service attacks against the U.S. firm Dyn and other online properties, the website Krebs on Security reports.