In-brief: The Electronic Frontier Foundation warned that it has evidence of man-in-the-middle attacks that take advantage of the same encryption-busting technology that Lenovo and Superfish implanted on consumer laptops.
man in the middle attack
Update: Superfish is the Real End of SSL
In-brief: Outrage over Lenovo’s promotion of privacy busting adware continued to grow amid lawsuits and more spying revelations. The big question: is this the final – final straw for the beleaguered Secure Sockets Layer (SSL) technology? (Updated to add comment from Kevin Bocek of Venafi.)
Microsoft Fixes 18 Year-Old Windows Hole Used In Attacks
At this late date, you’d like to think that all the really nasty vulnerabilities in legacy Windows systems have been identified. Wishful thinking. On Tuesday, Microsoft issued a patch for a critical, remotely exploitable vulnerability affecting Windows systems going back to Windows 95, one of 14 software fixes the company released. The vulnerability in Microsoft’s OLE (Object Linking and Embedding) code is associated with CVE-2014-6332 and is already being used in targeted attacks online. It is among the most serious discovered in recent years, exposing Windows systems to remote attacks that can bypass Microsoft’s Enhanced Mitigation Experience Toolkit (EMET) and Enhanced Protected Mode sandbox in the Internet Explorer browser. The vulnerability was discovered six months ago and patched, officially, on Tuesday with MS14-064, which fixes a related OLE vulnerability, CVE-2014-6352). Microsoft has also released a stop-gap tool that customers can use in lieu of the full patch. Microsoft has also issued an […]
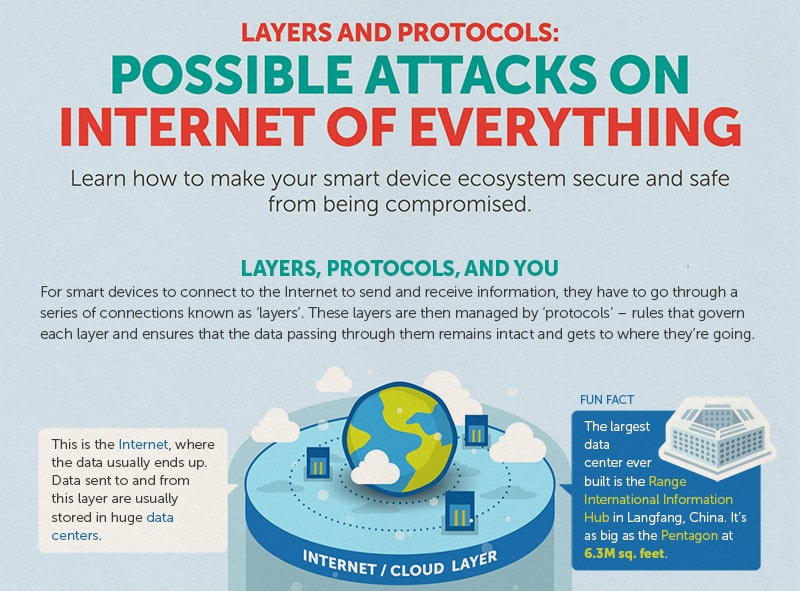
Infographic: Possible Attacks on The Internet of Things
The folks over at Trend Micro have put together a nice infographic that reminds us that all those smart devices connected to the Internet communicate through some well worn channels, namely: standard communications protocols like Wi-Fi, Ethernet and Bluetooth that connect devices to each other and the global Internet, as well as HTTP that are used to transmit data to and from cloud based resources like management interfaces. Of course those standard protocols also leave IoT devices vulnerable to a wide range of commodity attacks: from brute force password cracking on web based management consoles to Man in the Middle attacks that can sniff out authentication credentials and hijack sessions. Trend’s infographic does a good job of depicting the various layers in the IoT stack and some of the likely attack vectors for each layer. It also gives advice on how to protect yourself (use encryption, patch software vulnerabilities, disable unused ports). Nothing ground breaking […]
Ahead of Apple’s Announcement: The Security Implications of Wearables | Trend Micro
The world’s attention will be focused on Apple this week and on the topic of wearables. In an event on Tuesday, the Cupertino company is planning to unveil the latest additions to its popular iPhone line along with a wearable device that most folks are just calling the ‘iWatch.’ But as Apple wrestles with the security of its growing stable of mobile devices and the cloud infrastructure that supports them, what will the impact of wearables be? Well, the folks over at Trend Micro are putting together a series of blog posts that look at that very question. Namely: the (information) security implications of wearables. It makes for some interesting reading. Among other things, Trend There are three very broad categories that we can use to describe what we are talking about. The posts, by Senior Threat Researcher David Sancho, break down the wearables space into three categories: ‘IN’ devices like sensors, ‘OUT’ […]