In-brief: A new report from the firm Websense finds that financial services firms are being hit hard by cyber attacks, including targeted attacks aimed at luring employees into installing malicious software on corporate networks.
downloader
Clues Point to Long-Duration Hack at Sony
With each passing day, evidence mounts that the attack on Sony Pictures Entertainment was a long-duration hacking event that gave malicious actors extensive access to the company’s network and data. The hack started out looking like a particularly nasty example of hacktivism – with thousands of SPE systems wiped of all data. Going on two weeks after revelations of the hack, however, the incident appears to be something much more dire: a massive breach of corporate security that gave malicious attackers access to gigabytes – and possibly terabytes- of sensitive data. With only a fraction of the allegedly stolen data trove released, the ripple effects of the incident are already washing up against other Sony divisions and firms with direct or indirect ties to the company. The latest developments in the saga include publication of some 40 gigabytes of internal files. As described by buzzfeed.com, the files include: “email exchanges with employees regarding specific […]
Discrete Malware Lures Execs At High-End Hotels
Kaspersky Lab has a fascinating write-up of malware it is calling “DarkHotel.” The information-stealing software is believed to target traveling executives. Curiously, Kaspersky says the malware may be almost a decade old and is found only on the wireless networks and business centers of select, high-end hotels. Reports about targeted attacks on traveling executives are nothing new. However, the Kaspersky report (PDF version here) may be the most detailed yet on a specific malicious software family that is devoted to hacking senior corporate executives. According to Kaspersky, the DarkHotel malicious software maintained a presence on hotel networks for years, with evidence of its operation going back as far as 2007. The malware used that persistent access to target select hotel guests, leveraging check-in/check-out and identity information on guests to limit attacks to high value targets. Targeted guests were presented with iFrame based attacks that were launched from the hotel’s website, […]
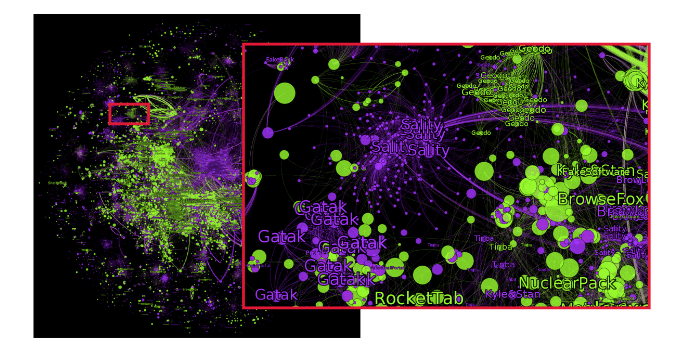
Dusting For Malware’s Bloody Prints
Malicious software is nothing new. Computer viruses and worms have been around for decades, as have most other families of malware like remote access tools (RATs) and key loggers. But all our experience with malware hasn’t made the job of knowing when our organization has been hit by it any easier. In fact, recent news stories about breaches at Home Depot, Target, Staples and other organizations makes it clear that even sophisticated and wealthy corporations can easily overlook both the initial compromise and endemic malware infections – and at great cost. That may be why phrases like “dwell time” or “time to discovery” seem to pop up again and again in discussions of breach response. There’s no longer any shame in getting “popped.” The shame is in not knowing that it happened. Greg Hoglund says he has a fix for that latter problem. His new company, Outlier Security, isn’t “next generation […]
Europol Warns of Internet of Things Risk
In a newly released report, Europol’s European Cybercrime Center (EC3) warns that the growth of the Internet of Things (IoT) threatens to strengthen the hand of organized cyber criminal groups and make life much more difficult for police and governments that wish to pursue them. EC3’s latest Internet Organized Crime Threat Assessment (iOCTA) says the “Internet of Everything” will greatly complicate the work of law enforcement creating “new opportunities for everything from cyber criminals to state actors to child abusers. The growing numbers of connected devices will greatly expand the “attack surface” available for cyber criminal activity, the EC3 warns. Cyber criminals may co-opt connected devices for use in common criminal activity (like denial of service attacks and spam campaigns). However, advancements like connected (“smart”) vehicles and infrastructure create openings for large scale and disruptive attacks. The report, which was published late last months, is a high level position paper and pulls data mostly […]