The folks over at SANS Internet Storm Center are pointing to a new study by Symantec that warns of threats posed by malicious code to virtual environments and warns that threats such as that the network traffic within virtual containers may not be monitored by services such as IDS or DLP. The paper covers how malware behaves in virtual environments. Specifically, the report examines W32.Crisis, a malicious program that is known to target virtual environments. The Crisis malware doesn’t exploit any specific vulnerability, SANS notes. Rather: it takes advantage of how the virtual machines are stored in the host system to manipulate that environment for malicious purposes while escaping detection. via InfoSec Handlers Diary Blog – Threats to virtual environments.
virtualization
Vulnerable Mobile Software Management Tool Reaches Into IoT
You could be forgiven for never having heard of Red Bend Software. The company is small – just 250 employees- and privately held. Red Bend’s headquarters is a suite of offices in a nondescript office park in Waltham, Massachusetts, just off Route 128 – America’s “Silicon Highway.” But the company’s small profile belies a big footprint in the world of mobile devices. Since 2005, more than 2 billion devices running the company’s mobile management software have been sold worldwide. Today, the Red Bend is believed to control between 70 and 90 percent of the market for mobile software management (MSM) technology, which carriers use to service mobile devices. The software enables mobile carriers to do critical tasks, including firmware-over-the-air (FOTA) software updates, mobile device configuration and other on-device changes. Red Bend counts many of the world’s leading companies in the mobile, enterprise and manufacturing sectors as clients, including Intel, Qualcomm, Samsung, Sharp, LG, Sony, Huawei, China Mobile and Lenovo. For the most part, Red […]
Intel Promotes ‘Trustlets’ To Secure Embedded Devices
The integrity of data stored on- and transmitted between Internet-connected embedded devices is one of the biggest technical hurdles standing in the way of widespread adoption of Internet of Things technology. For one thing: embedded devices like wearable technology and “smart” infrastructure are often deployed on simple, inexpensive and resource constrained hardware. Unlike laptops or even smart phones, these are purpose-built devices that, by design, run for long periods in remote deployments, with extremely constrained features and low power consumption that is the result of limited processing power and memory. [Read Security Ledger’s coverage of connected vehicles.] Now Intel is promoting a platform that it says can bridge the gap and provide robust security features even for resource-constrained Internet of Things devices like wearables and connected vehicles. Back in April, the Intel Labs unveiled the results of joint research with Technische Universität Darmstadt in Germany. The researchers have developed a platform, dubbed TrustLite […]
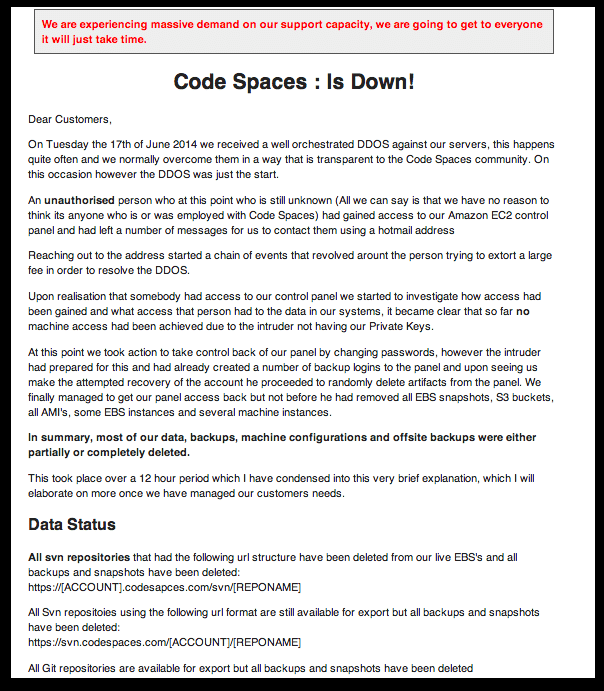
Code Spaces Probably A ‘Target of Opportunity’
The spectacular collapse this week of Code Spaces, a cloud-based code repository, may have been the result of a an unspectacular “opportunistic” hack, rather than a targeted operation, according to one cloud security expert. The sudden demise of the online application repository has sent shock waves through the tech industry, laying bare what some say are lax practices among many cloud-based application and infrastructure providers. But the attack itself was almost certainly the result of a larger, indiscriminate cyber criminal campaign, said Jeff Schilling, the Chief Security Officer of Firehost, a Texas-based secure cloud provider. “This is something we pretty frequently: companies get held ransom with a DDoS attack, and if that doesn’t work, (the attackers) will resort to doing other things,” Schilling told The Security Ledger. But Code Spaces almost certainly wasn’t the only company the extortionists worked on, Schilling said. Instead, the company was likely caught up in a wide net […]
Pew: IoT Will Take Off By 2025, Despite Security Woes
A survey of technology experts by the Pew Research Center and Elon University predicts that the Internet of Things will take off in the next decade despite serious concerns about the security of IoT devices and the data they hold. The IoT will gain wide adoption in the next decade, with the result that many aspects of day-to-day life will be transformed by a combination of inexpensive sensors, cloud based computing and data analytics. The report cites a number of likely innovations that will become commonplace by 2025 – from “smart” food products that can report when they are exhausted or spoiled, to smart roads and infrastructure to “subcutaneous sensors or chips that provide patients’ real-time vital signs to self-trackers and medical providers.” The Pew Center canvassed more than 1600 technology leaders and analysts about the Internet of Things and published the findings of the survey on Wednesday. The survey population included […]