John Halamka, the CIO of Beth Israel Deaconness Medical Center in Boston has an interesting post on his blog about Apple’s big unveiling yesterday and its implications for connected health applications. With the image of naked Jennifer Lawrence still fresh in our minds, Halamka points out that Apple is taking steps to make sure no such slip-ups happen in the context of protected health information – a promising new market for wearable technology. As Halamka sees it, we’re on the cusp of revolution that will see the consumerization of what he calls “healthcare middleware.” That refers to software and services, like Apple’s recently announced HealthKit, that aggregates data about your body from multiple sensors in your clothing, your body and environment. Unlike the nude selfies that recently made the rounds online, however, health data is protected by Federal legislation – HIPAA. For that reason, Apple keeps that data local to the mobile […]
iPhone
Samsung Expanding Mobile Management To Court Enterprise
Editor’s Note: this story was updated to note that Centrify is now known as Delinea. PFR Sept. 18, 2022 Apple stole the show this week, unveiling its new, larger iPhones and a smart watch that everyone is just calling iWatch, whether that’s the product’s name or not. But the rush of new products from Cupertino doesn’t change the fact that, behind the scenes, the battle for the hearts and minds of business users (aka “enterprises”) rages on between Apple, Google, Microsoft and Blackberry. iPhone 6 or no, the outcome of that battle is anything but clear. Case in point: Samsung will roll out new features this week for its KNOX-powered Android phones and tablets that are designed to appeal to security and privacy conscious business users. The new KNOX solution offerings, which will become public on Thursday, promise enterprises and government organizations the tools to simplify the implementation of BYOD (or Bring Your Own Device) programs. In […]
Ahead of Apple’s Announcement: The Security Implications of Wearables | Trend Micro
The world’s attention will be focused on Apple this week and on the topic of wearables. In an event on Tuesday, the Cupertino company is planning to unveil the latest additions to its popular iPhone line along with a wearable device that most folks are just calling the ‘iWatch.’ But as Apple wrestles with the security of its growing stable of mobile devices and the cloud infrastructure that supports them, what will the impact of wearables be? Well, the folks over at Trend Micro are putting together a series of blog posts that look at that very question. Namely: the (information) security implications of wearables. It makes for some interesting reading. Among other things, Trend There are three very broad categories that we can use to describe what we are talking about. The posts, by Senior Threat Researcher David Sancho, break down the wearables space into three categories: ‘IN’ devices like sensors, ‘OUT’ […]
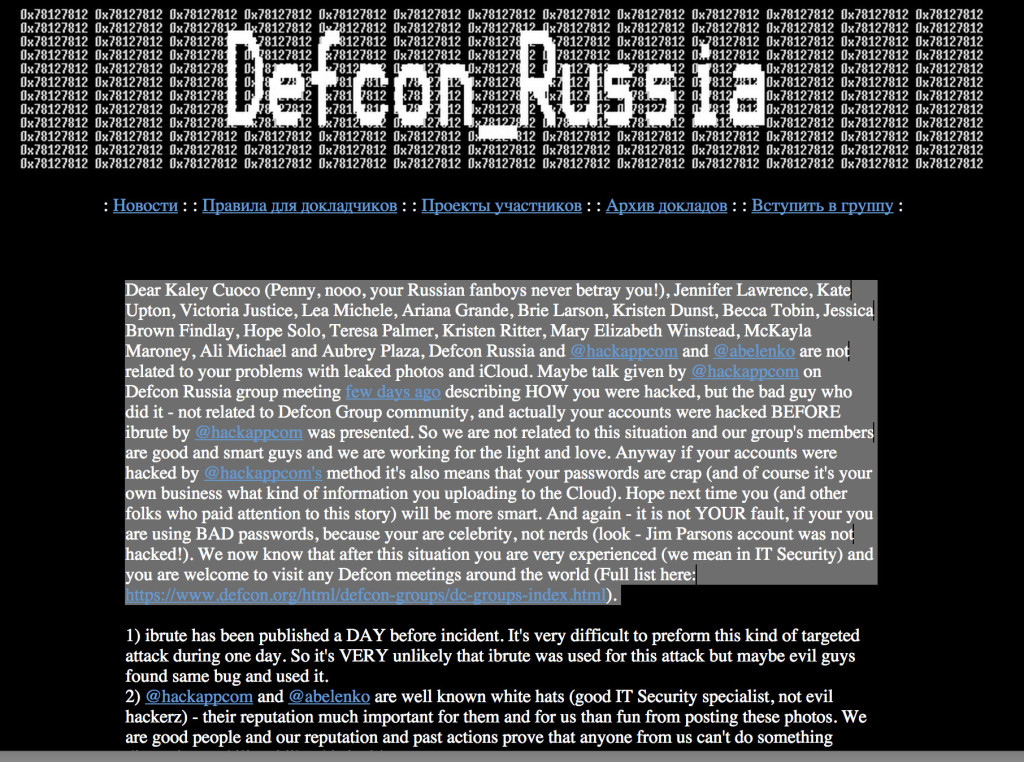
Hack Tool Authors Deny Link To Celeb Photo Leaks
With some of Hollywood’s biggest stars issuing statements on Monday condemning the leak of personal photographs online, attention has turned to identifying the source of the leaks. But more than 24 hours after the photos appeared, there are more questions than answers about its source. Early attention has focused on an automated tool that exploited an apparent vulnerability in Apple’s FindMyiPhone feature. But by Monday, there were denials from the makers of that tool that it played any role in the massive privacy breach that saw photos of A-list celebrities like Jennifer Lawrence, Kate Upton and others leaked online. Within hours of the photos’ appearance on the image sharing site 4chan, attention shifted to the cause of the leak and the coincidence of the leaked photos with the publication of iBrute, a simple tool available on GitHub in recent days. According to this published report by Owen Williams over at TheNextWeb, the […]