Iran’s Chafer hacking group is targeting aviation repair and maintenance firms in an apparent effort to obtain information needed to shore up the safety of that country’s fleet of domestic aircraft, according to research by the firm Symantec.
published research
Consumer Reports: Flaws Make Samsung, Roku TVs Vulnerable
Consumer Reports warns that smart TVs by Samsung and other vendors are vulnerable to disorienting remote attacks.
Episode 81: Hacking IoT with Physics, Poor Grades for Safety Wearables and Peak Ransomware
In this week’s podcast: researcher Kevin Fu of University of Michigan discusses his work on attacks that use physics to manipulate connected devices. Also: Mark Loveless of DUO discusses his research into how poor implementation of wireless protocols make personal security trackers a privacy risk. And have we seen peak ransomware? Adam Kujawa of the firm Malwarebytes joins us to talk about the findings of that company’s State of Malware Report.
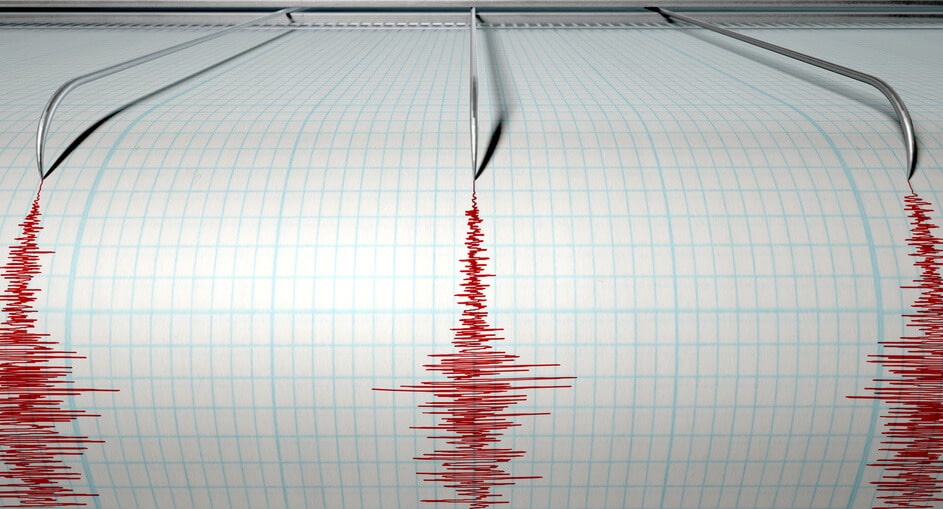
Researchers Warn of Physics-Based Attacks on Sensors
Billions of sensors that are already deployed lack protections against attacks that manipulate the physical properties of devices to cause sensors and embedded devices to malfunction, researchers working in the U.S. and China have warned.
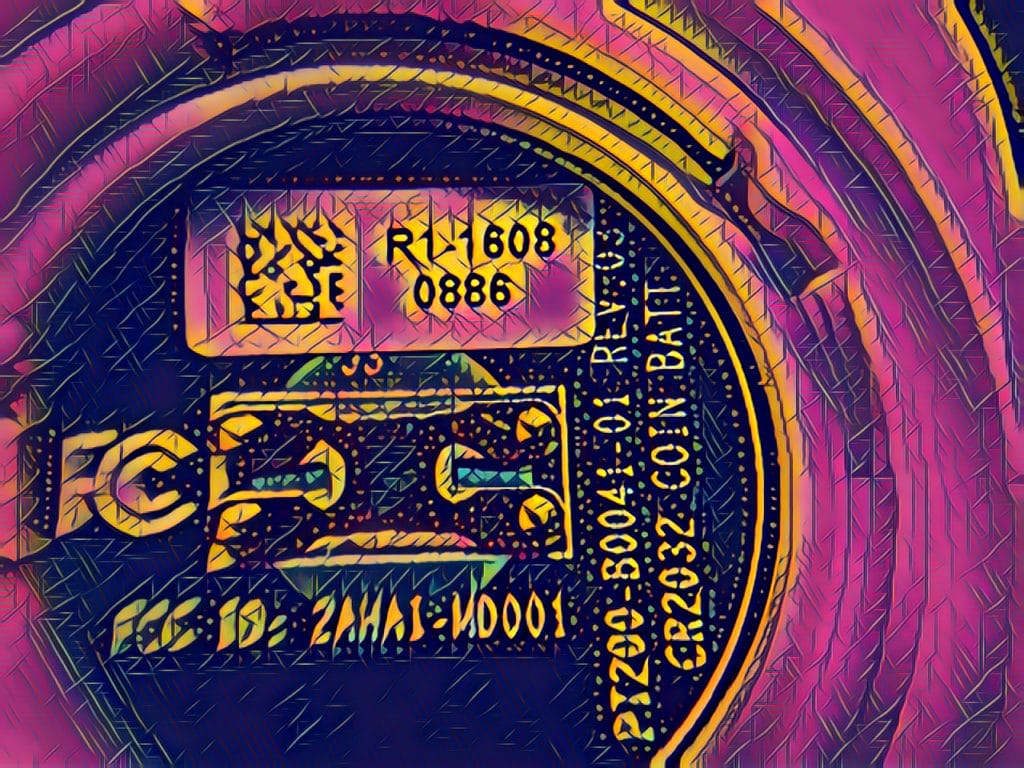
Podcast: Why Germany wants Smart Watches destroyed and One Nation Under Trolls
In this week’s Security Ledger podcast, sponsored by our friends at CyberArk, we talk about the German government’s recent decision to declare kids smart watches “surveillance devices” and to order their destruction. Also: Adrian Shabaz of Freedom House comes in to talk to us about the latest Internet Freedom report, which finds that governments are increasingly manipulating online content to shape online discussions and even the outcome of elections at home and abroad. And finally: leaked credentials in a GitHub repository may have been behind Uber’s loss of information on some 50 million customers. In a preview of a Security Ledger spotlight podcast, we hear from Elizabeth Lawler of CyberArk about the proliferation of so-called “Dev Ops secrets” and how companies need to do a better managing the permissions assigned to applications.