In-brief: Samsung isn’t alone in asking customers to consent to the collection and transmission of “voice data.” But questions about the ethics and legality of the practice remain.
Smart TV
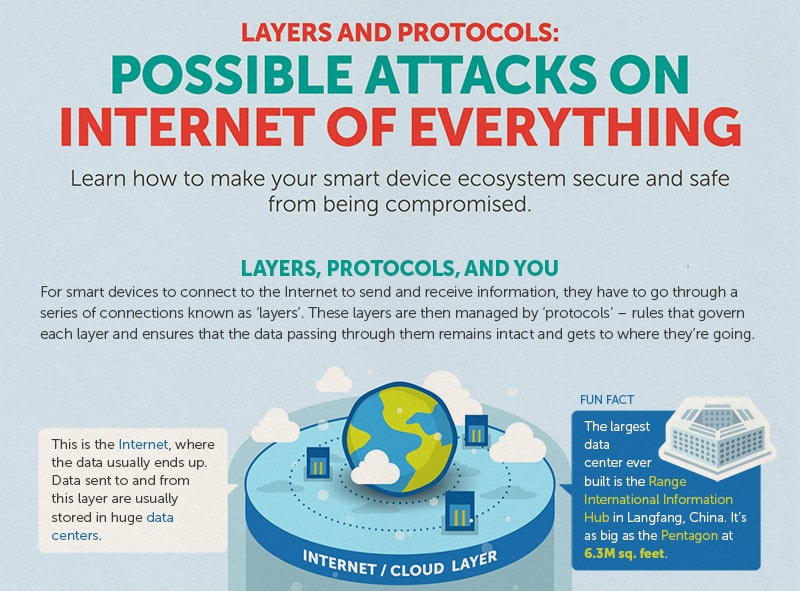
Infographic: Possible Attacks on The Internet of Things
The folks over at Trend Micro have put together a nice infographic that reminds us that all those smart devices connected to the Internet communicate through some well worn channels, namely: standard communications protocols like Wi-Fi, Ethernet and Bluetooth that connect devices to each other and the global Internet, as well as HTTP that are used to transmit data to and from cloud based resources like management interfaces. Of course those standard protocols also leave IoT devices vulnerable to a wide range of commodity attacks: from brute force password cracking on web based management consoles to Man in the Middle attacks that can sniff out authentication credentials and hijack sessions. Trend’s infographic does a good job of depicting the various layers in the IoT stack and some of the likely attack vectors for each layer. It also gives advice on how to protect yourself (use encryption, patch software vulnerabilities, disable unused ports). Nothing ground breaking […]
Micro Survey of Smart Home Devices Finds Much To Fault
Larry Dignan over at ZDNet is writing about a new survey by HP’s Fortify application security division that finds 70 percent of Internet of things devices have exploitable software vulnerabilities. Some caveats: HP makes its conclusions based on scans of “10 of the most popular Internet of things devices.” That’s a very small sample size that could (greatly) skew the results one way or the other. So take this with a grain of salt. You can download the full survey here. (PDF) [Read Security Ledger coverage of Internet of Things here.] According to Dignan, HP found 25 vulnerabilities per device. Audited devices included TVs, Webcams, thermostats, remote power outlets, sprinklers, door locks, home alarms, scales and garage openers. One of each, from the sound of it. The findings, assessed based on the OWASP Internet of Things Top 10 list and vulnerability categories, account for the devices as well as cloud and […]
ARM Eyes Role as Supplier to the Internet of Things
Writing for Fortune this week, Katherine Noyes has an interesting piece that looks at how ARM is looking to parlay its success in the mobile phone market into a dominant role as a supplier for the Internet of Things (IoT). “There’s a real opportunity here,” Noyes quotes Ian Ferguson, ARM’s vice president of segment marketing saying. AMD licenses designs to silicon makers like Qualcomm and AMD. Already, some of those designs are showing up in IoT products like fitness bands. That could expand – and mobile phones are the management interface for many IoT products, which also stokes ARM’s business. But the company thinks the real opportunity lies in commercial technology for verticals like infrastructure (smart cities), manufacturing and oil and gas exploration. “You’ve got highly valued assets, so preventative mechanical services can help improve efficiency by detecting problems before they break down,” Ferguson said. ARM acquired Sensinode Oy in August, 2013. Sensinode pioneered software and […]
Is It Time For Customs To Inspect Software? | Veracode Blog
If you want to import beef, eggs or chicken into the U.S., you need to get your cargo past inspectors from the U.S. Department of Agriculture. Not so hardware and software imported into the U.S. and sold to domestic corporations. But a spate of stories about products shipping with malicious software raises the question: is it time for random audits to expose compromised supply chains? Concerns about ‘certified, pre-pwned’ hardware and software are nothing new. In fact, they’ve permeated the board rooms of technology and defense firms, as well as the halls of power in Washington, D.C. for years. The U.S. Congress conducted a high profile investigation of Chinese networking equipment maker ZTE in 2012 with the sole purpose of exploring links between the company and The People’s Liberation Army, and (unfounded) allegations that products sold by the companies were pre-loaded with spyware. Of course, now we know that such […]