Steve Lawson at IDG News Service has an interesting article that notes AT&T’s certification of the U-blox SARA-U260 model, which is dubbed “the world’s smallest 3G module.” The 16 x 26 millimeter device is seen as a harbinger of the kind of low power device that will greatly expand the Internet of Things. The SARA-U260 is designed to transmit small amounts of data over 3G networks and could enable a new generation of even smaller and smarter devices – from Smartmeters to wearable technology to connected cars. The U260 has features that support applications from voice calling to auto industry telematics to retail point-of-sale terminals and handheld devices, according to U-blox. It uses A-GPS (Assisted Global Positioning System) and a technology called CellLocate that uses nearby cellular towers to triangulate a location in situations where GPS isn’t available. 3G and 2G networks are being replaced by 4G and even 5G networks for most consumer smart phones. But the technology still works great […]
quantifiable self
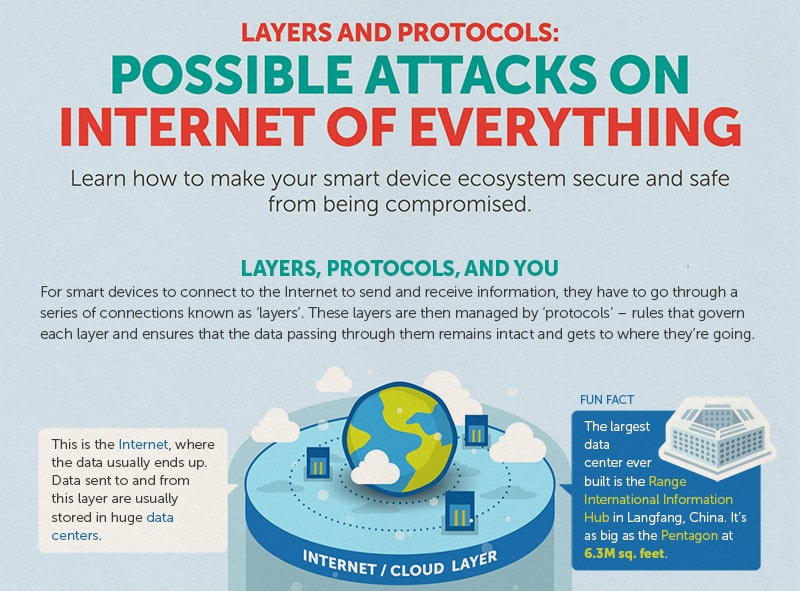
Infographic: Possible Attacks on The Internet of Things
The folks over at Trend Micro have put together a nice infographic that reminds us that all those smart devices connected to the Internet communicate through some well worn channels, namely: standard communications protocols like Wi-Fi, Ethernet and Bluetooth that connect devices to each other and the global Internet, as well as HTTP that are used to transmit data to and from cloud based resources like management interfaces. Of course those standard protocols also leave IoT devices vulnerable to a wide range of commodity attacks: from brute force password cracking on web based management consoles to Man in the Middle attacks that can sniff out authentication credentials and hijack sessions. Trend’s infographic does a good job of depicting the various layers in the IoT stack and some of the likely attack vectors for each layer. It also gives advice on how to protect yourself (use encryption, patch software vulnerabilities, disable unused ports). Nothing ground breaking […]
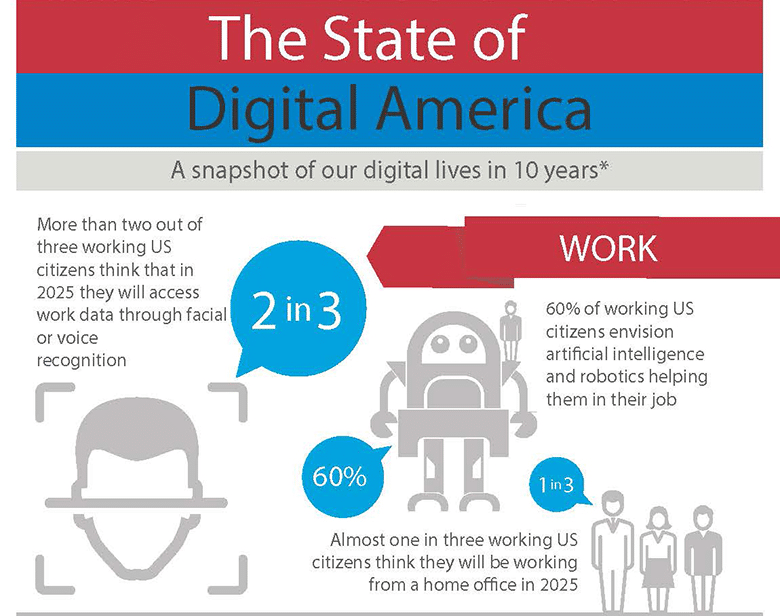
Infographic: The State of Digital America in 2025
Consumers Embrace IoT And Wearables, Worry About Security Consequences
A new survey of consumer attitudes and expectations about technology finds that a strong majority of Americans expect wearable technology and biometric security to be common within the next decade. The survey, sponsored by the security company McAfee, asked 1,500 U.S. consumers about lifestyle and technology trends in the home and workplace. The results suggest that consumers are already adjusting their expectations about the future to include pervasive connectivity, a wealth of intelligent devices – and some of the problems that come with both. More than 60% of those surveyed by McAfee said they anticipate having connected appliances like refrigerators that will “automatically add food to a running grocery list if the product is running low.” A strong majority of those polled – 84% – said they were convinced their home security systems will be connected to their mobile device. “As technology, especially the Internet of Things, continues to rapidly advance and […]
Apple’s Platform for Wellness Arrives | Life as a Healthcare CIO
John Halamka, the CIO of Beth Israel Deaconness Medical Center in Boston has an interesting post on his blog about Apple’s big unveiling yesterday and its implications for connected health applications. With the image of naked Jennifer Lawrence still fresh in our minds, Halamka points out that Apple is taking steps to make sure no such slip-ups happen in the context of protected health information – a promising new market for wearable technology. As Halamka sees it, we’re on the cusp of revolution that will see the consumerization of what he calls “healthcare middleware.” That refers to software and services, like Apple’s recently announced HealthKit, that aggregates data about your body from multiple sensors in your clothing, your body and environment. Unlike the nude selfies that recently made the rounds online, however, health data is protected by Federal legislation – HIPAA. For that reason, Apple keeps that data local to the mobile […]