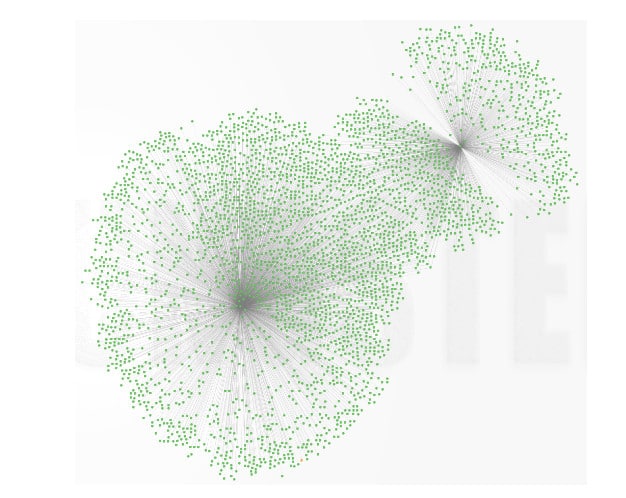
A mysterious piece of software, dubbed Wifatch, has been infecting tens of thousands of Linux-based home routers and, according to experts at Symantec, attempts to secure them from attack. But Wifatch’s benevolent intentions shouldn’t obscure its malicious actions, or the security problems that it takes advantage of. The malicious software runs on vulnerable, Linux-based home routers. There, it removes other malware infections, disables vulnerable services like Telnet and even prompts users to update their administrator user name and password to prevent compromise, according to a post on Symantec’s blog. But the malware is still spreading between vulnerable systems without the owners consent and could easily be pressed into service distributing spam or malicious software, experts note. According to Symantec, Wifatch is likely spreading between infected devices by targeting exposed Telnet interfaces and using brute force password attacks to gain access to the devices. Tens of thousands of devices may have been infected […]
hub
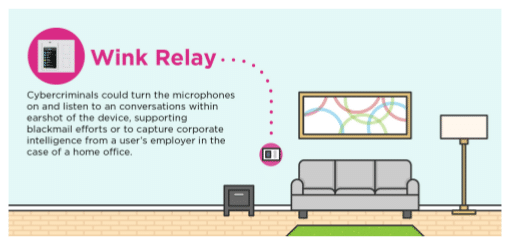
Research: IoT Hubs Expose Connected Homes to Hackers
In-brief: A study of common connected home gateways finds lax security that could expose consumers to snooping or even malicious attacks, according to the application security firm Veracode.
Nest, Samsung and AMD Back Thread For Home Automation
A week that has already been full of standards news for the Internet of Things added more with the unveiling of Thread, a proposed communications standard backed by Google’s NEST group that promises a “new and better way to connect products in the home.” Google was joined by Samsung, Freescale Semiconductor, ARM, smart lock maker Yale Security and Big Ass Fans (favorite company name ever) in forming The Thread Group to promote Thread. In a press release on Tuesday, the group said that the Internet of Things presents unique challenges that are not well met by existing wireless communications technologies such as Wi-Fi, ZigBee and Z-Wave. In contrast to those technologies, Thread focuses exclusively on network connectivity, not application-layer exchanges and connection management. Thread Group says existing application protocols and IoT platforms can easily run on Thread networks. Specifically, it uses 6LoWPAN (IPV6 over Low power Wireless Personal Area Networks) to create 802.15.4-standard mesh networks of smart […]
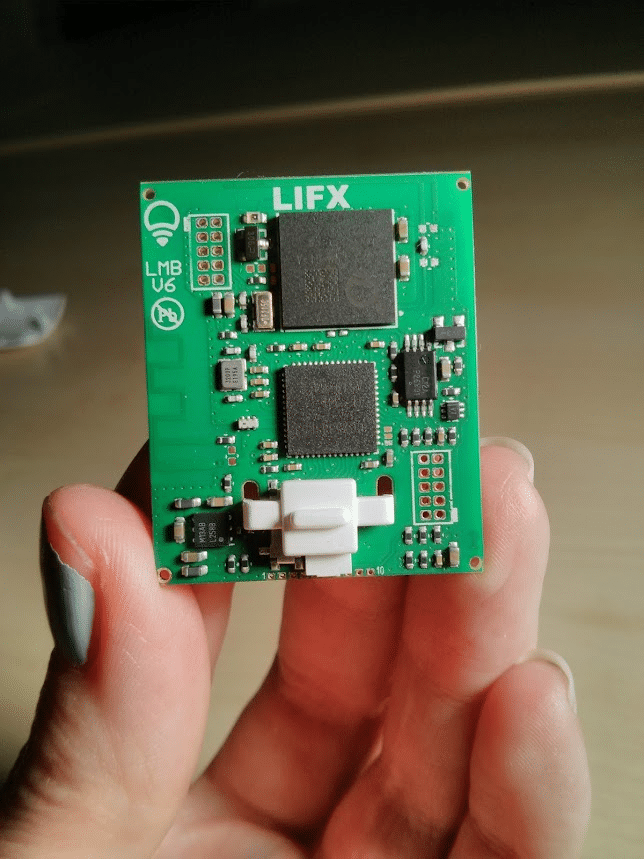
That LIFX Smart Lightbulb Hack Wasn’t Easy
If you’ve been following your Internet of Things security news, you probably read about the latest hack of a consumer-oriented ‘smart home’ device: Context Information Security’s analysis of security holes in LIFX-brand smart light bulbs. The top line on this is scary enough. As The Register reported: researchers at Context discovered that, by gaining access to a “master bulb” in LIFX deployments, they could control all connected lightbulbs and expose user network configurations. That’s scary – and recalls research on hacking Philips HUE light bulbs that was published last year. But read down in the Context research and you’ll realize that, while the LIFX technology wasn’t perfect, the job of hacking the technology wasn’t child’s play, either. LIFX connected its smart bulbs using a 6LoWPAN-based mesh network. The company made the mistake of transmitting most bulb-bulb communications in the clear, which made analyzing traffic sent between master- and slave bulbs easy. Context researchers found […]
Is HyperCat An IoT Silo Buster? | ZDNet
Steve Ranger over at ZDNet has an interesting write-up on HyperCat, a UK-funded data sharing open specification for Internet of Things devices. The new specifications has the backing (or at least interest) of major players and could become an alternative to proprietary standards such as Apple’s HomeKit or Google Nest. HyperCat is described as an “open, lightweight, JSON-based hypermedia catalogue” that is designed to “expose information about IoT assets over the web.” The goal is to provide a set of open APIs and data formats that startups and other smaller firms can use to built ecosystems of connected objects. Smart devices are typically developed using common technologies and platforms: RESTful APIs, JSON (Javascript Object Notation) for data formatting and HTTP (or secure HTTP) as the main communications protocol. However, the Internet of Things is badly “silo’d” – meaning that interoperability between IoT devices happens only when those smart devices happen to use the […]