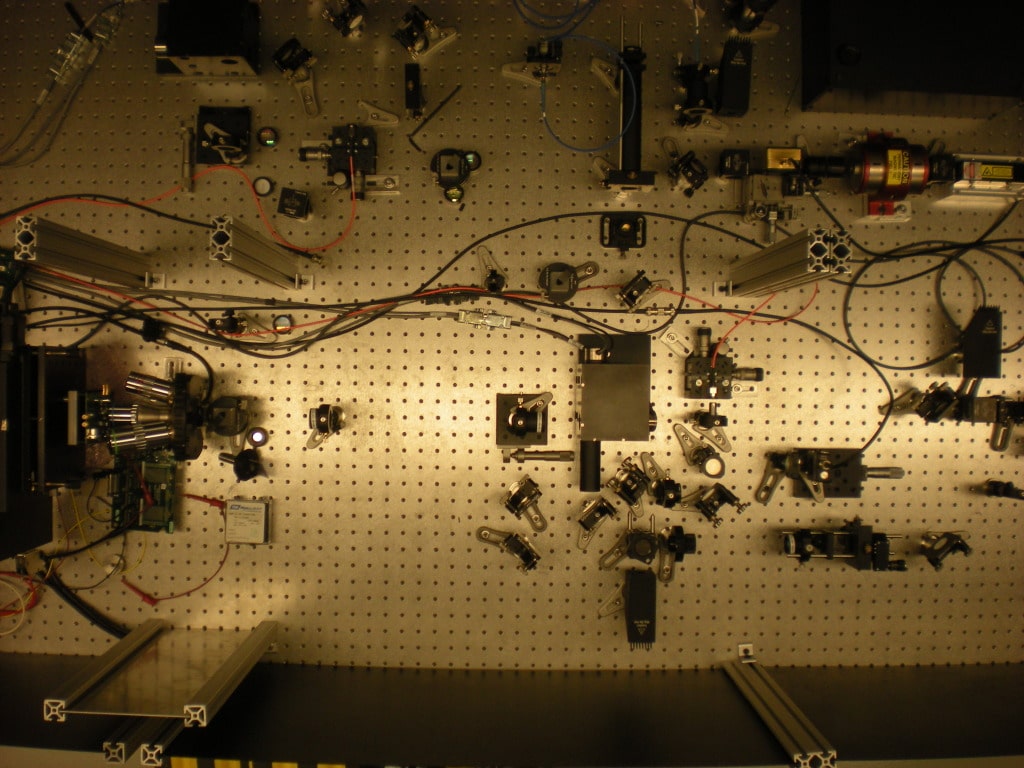
The U.S. Defense Advanced Research Projects Administration (DARPA) announced on Wednesday that advanced software and equipment it developed to spot counterfeit microelectronics in U.S. weapons and cyber security systems has been handed over to military contractors to continue development. DARPA said the product of its Integrity and Reliability of Integrated Circuits (IRIS) program: the Advanced Scanning Optical Microscope (ASOM) technology was transferred to the Naval Surface Warfare Center (NSWC) in Crane, Indiana, where it will be used to inspect microelectronics for signs of tampering or compromise. The technology was developed with the help of SRI International, an IRIS contractor. Read more Security Ledger coverage of supply chain risks. “The ASOM technology housed at NSWC Crane will help engineers provide forensic analysis of microelectronics, including integrated circuits (IC) confiscated by law enforcement officials,” DARPA said in a statement. The DoD is a major buyer of integrated circuit chips, which are mainly manufactured outside the U.S. […]
Infrastructure
With Cars Connected to the Internet, What about Privacy? | Computerworld
Lucas Mearian has a long and quite thorough article over at Computerworld weighing the possible security and privacy risks posed by connected vehicles. Among other things, Mearian weighs the recent past and likely future of connected vehicles, noting that, “once mobile devices are connected to car infotainment systems and cars are connected to the Internet, vehicles will become a rich source of data for manufacturers, marketers, insurance providers and the government.” They’ll also be a target for hackers. The problem is that, unlike mobile phones, cars have useful lives that are measured in decades, not years – or even months. That makes it difficult for manufacturers, who want to make their vehicles state of the art, but also must deal with the reality of much longer development cycles and complex interactions between non-critical and critical on board systems. [Read more Security Ledger coverage of connected vehicles here.] A couple issues worth noting: […]
New England IoT: A Conversation Next Week On Cloud, Security and Internet of Things
One of the challenges of talking about security in the context of Internet of Things is that the Internet of Things (IoT) isn’t a discrete technology, but an umbrella phrase that encompasses a lot of separate innovations: mobility, inexpensive sensors, wireless connectivity, Big Data and so on. One of the biggest moving parts in the IoT puzzle is cloud computing. Cloud infrastructure – whether its Amazon’s Elastic Compute Cloud (EC2) or Google or any of the thousands (millions?) of private cloud – is the back end for almost every IoT product. That presents both opportunities and real challenge for companies that are looking to leverage IoT in their workplace. Next week, I’m going to moderate a panel at an event here in Boston where we’ll tackle some of these issues head-on. The event: The Connected Cloud Summit is taking place in Boston on Thursday, September 18 at The State Room in downtown Boston. […]
Cyber Insurance Is Sexy
So bland is the insurance business perceived to be, that it’s the stuff of Hollywood comedy. In the 2004 film Along Came Polly, Ben Stiller played a skittish, risk averse insurance adjuster with actuarial data on bathroom hygiene at his fingertips (no pun). Woody Allen famously depicts his hapless criminal Virgil Starkwell locked in solitary confinement with an eager insurance salesman in the 1969 mocumentary Take the Money and Run. Cruel and unusual punishment, indeed. Boring though they may be, insurance markets are incredibly important in helping society manage risks of all sorts. Insurance markets also have a funny way of shaping behavior – both personal and commercial – in ways that serve the public interest. Take the response to Hurricane Sandy as just one example. Law makers in Washington D.C. may never agree on whether that storm was a product of a warming climate. In fact, they may debate the […]
Must Read: How Russian Hackers Stole the Nasdaq – Businessweek
If there’s one story you should read this week, its Michael Riley’s extensive report over at Businessweek on the 2010 compromise of systems belonging to the Nasdaq stock exchange, “How Russian Hackers Stole the Nasdaq.” The incident was extensively reported at the time, but not in great depth. Obviously, the parties involved weren’t talking. And Nasdaq’s public statements about the compromise woefully downplayed its severity, as Riley’s report makes clear. Among the interesting revelations: the Nasdaq may have fallen victim to a third-party compromise – similar to the hack of Target earlier this year. In the case of Nasdaq, investigators from the FBI, NSA and (eventually) CIA found discovered that the website run by the building management company responsible for Nasdaq’s headquarters at One Liberty Plaza had been “laced with a Russian-made exploit kit known as Blackhole, infecting tenants who visited the page to pay bills or do other maintenance.” What’s clear is […]