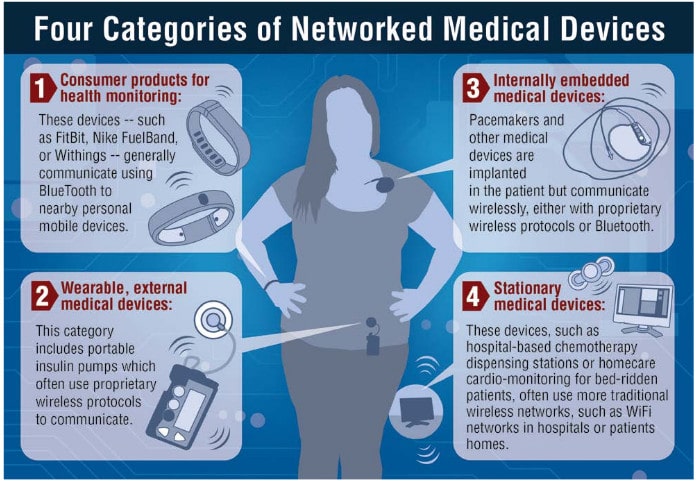
In-brief: connected medical devices pose a number of risks to patients, including the threat of “targeted killings,” according to a report by Intel Security. The fix: better application design and more public-private sector cooperation.
Infrastructure
At Summit, in search of Leadership on Cyber Security
In-brief: President Obama will address technology leaders at a Summit at Stanford University on Friday. But technology industry leaders say that much hinges on Washington’s ability to pass needed legal reforms.
Malware Campaign Against Industrial Systems Almost 3 Years Old
The U.S. Government’s Industrial Control System CERT (ICS-CERT) said on Thursday that a campaign targeting industrial control system (ICS) software began in January, 2012 and targeted industrial systems that were directly connected to the public Internet. ICS-CERT said in an alert published on Wednesday that “HMI” (or Human-Machine Interfaces) products from vendors including GE, Advantech/Broadwin and Siemens may have been infected with variants of the BlackEnergy malware since January, 2012. Infected firms were running versions of the GE’s Cimplicity, Advantech/Broadwin’s WebAccess or Siemens’ WinCC with what ICS-CERT called a “direct Internet connection.” In some cases, as with the GE Cimplicity attacks, hackers exploited a known vulnerability in the Cimplicity software to gain access. In others (as with WebAccess and WinCC) the method by which the software was compromised isn’t known, ICS-CERT said. CERT said it hasn’t documented any cases of control processes being modified by the malware. However, BlackEnergy is typically used […]
Is IoT Innovation Outpacing Our Ability To Keep It Safe?
GigaOm has an interesting, high-level piece that looks at the issue of law, liability and the Internet of Things. The article takes off from a discussion at the Download event in New York City earlier this month, wondering whether adoption of Internet of Things technologies like wearables is starting to run far ahead of society’s ability to manage them. Specifically: is the pace of technology innovation outstripping the ability of our legal system to reign in excess and protect public safety and civil liberties? On the list of ‘what-if’s’ are some familiar questions: How to assign liability. (“If one of Google’s automated cars crashes, is it the fault of the driver or Google?”) Read more Security Ledger coverage of Internet of Things here. What responsibility to users have to take advantage of safety features in connected products? (Does a parent’s failure to password-protect a baby monitor change the manufacturer’s liability when and […]
New York City Phone Booths Add Beacons, Stoke Controversy
The web site Buzzfeed has a scoop today about a stealthy deployment of beacon technology in Manhattan that has some privacy experts concerned. According to the exclusive report, by Buzzfeed’s Joseph Bernstein and Jeremy Singer-Vine, Titan a media company that sells ad space in more than 5,000 phone kiosk panels in New York City’s five boroughs, has installed about 500 beacons on its ad panels. The company went forward with the deployment with the blessing of New York City’s Department of Information Technology and Telecommunications (DoITT), but without any public input, Buzzfeed reported. Beacons are wireless devices that interact with mobile phones and other portable electronics. They’re used to provide location-specific data and interactions, such as advertisements linked to nearby businesses or to track the movements of an individual within a defined space (such as a show floor). In the case of the phone booth beacons, Titan and Sbordone, the company that provides the display […]