In this week’s Security Ledger Podcast (#88) we do a deep dive with researcher Vikram Thakur of the firm Symantec on “Dragonfly,” the Russian hacking group whose actions prompted the U.S. Department of Homeland Security and the FBI to issue a joint statement last week warning of intrusions into critical infrastructure in the US. Also: how do cyber criminals cash out all the loot they make from online scams? In our second segment we’ll talk to researcher Mike McGuire of the University of Surrey, who has been studying that question.
Crime
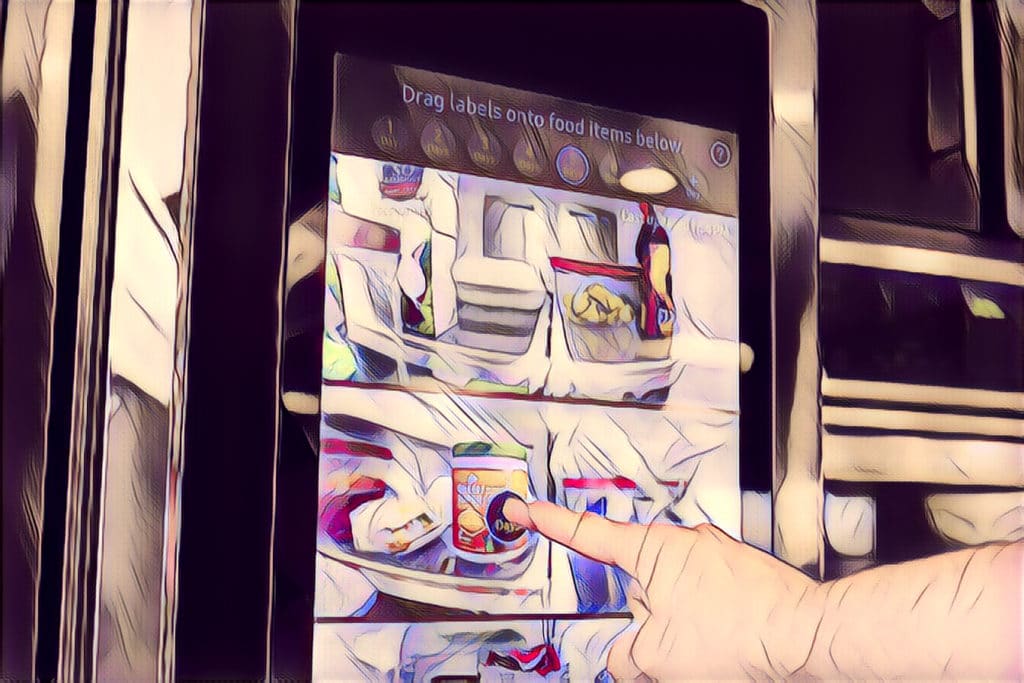
Smart Homes May Hide Crypto Mining Schemes
Loosely attended smart home appliances may be platforms for cryptocurrency mining scams, a researcher with the firm IOActive warns.
North Korea’s widening Net, pricing the Equifax Hack & Dark Markets in Turmoil
In this week’s podcast, after a string of reports about North Korea’s growing forays onto sensitive corporate networks, we speak with Adam Meyers of CrowdStrike about the widening net of North Korean offensive hacking and how the Hermit Kingdom is playing the part both of cyber criminal and nation-state actor. Also: we unpack the cost of the Equifax breach with Accenture and talk to Flashpoint about the turmoil on the deep, dark web following the shutdown of the AlphaBay marketplace.
Dark Markets do it better, surveying the Phishing underground and dissecting a Fancy Bear attack
In episode 69 of The Security Ledger podcast, we speak with Luca Allodi of The University of Eindhoven in The Netherlands about research on the functioning of dark markets. Also: DUO Security researched the trade in phishing toolkits – you’ll be surprised at what they learned. And we deconstruct a campaign against the citizen journalism website Bellingcat.com to understand how the Russian Group known as Fancy Bear works.
Six Cyber-Physical Attacks the World Could Live Without
In-brief: cyber attacks that affect physical systems are still a small minority of all incidents. But they’re becoming more common. What are some of the attacks we’ve seen to date and what do they tell us about what’s to come? Check out this slide show for an answer to those questions.