In this episode of The Security Ledger Podcast (#107): Hacker Summer Camp takes place in Las Vegas this week as the Black Hat, DEFCON and B-Sides conferences take place. We’re joined by DigiCert Chief Technology Officer Dan Timpson to talk about the presentations that are worth seeing. And, in our second segment, The Department of Homeland Security launched a new Risk Analysis Center that sounds a whole lot like some programs it already runs. Is this bureaucratic overkill or is DHS on to something?
B-Sides
Podcast: Infosec has a #MeToo Problem also TOR-ifying Wikipedia
In this week’s Security Ledger Podcast, we talk with Genevieve Southwick, CEO of the B-Sides Las Vegas hacker conference about the information security industry’s #metoo problem and what steps conference organizers are taking to stem sexual assault and harassment at information security events. Also: researcher Alec Muffet talks with us about making a TOR version of Wikipedia (and why it’s not sticking around). Finally, Martin McKeay of Akamai talks about the state of Internet security one year after Mirai. (Spoiler alert: Mirai is still a problem.)
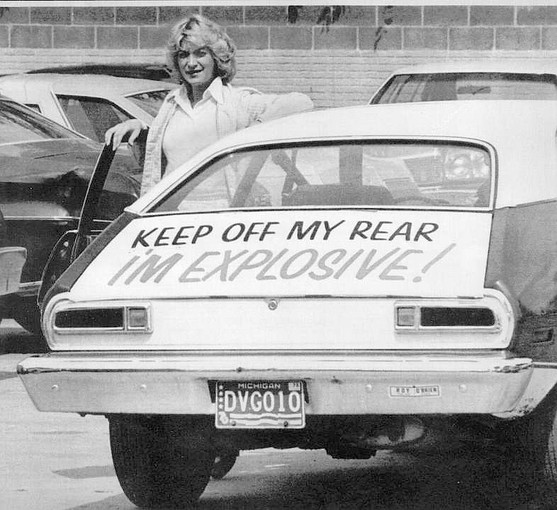
Exploding Gas Tanks: Risk, Liability and Internet of Things
We like to construct Hollywood friendly plots around a lot of the seminal moments in our collective history. For Civil Rights, we like to picture the integration of Little Rock High School, Rosa Parks’ courageous protest on a Montgomery bus or the March on Washington. For environmentalism, we talk about Rachel Carson’s Silent Spring or, maybe, the burning Cuyahoga River in Cleveland. (This vintage news footage of the 1969 fire calls it the fire that “sparked the environmental movement” without any apparent irony.) For automobile safety, we imagine Ralph Nader and the image of a 1972 crash test that shows the gas tank of the Ford Pinto exploding in a rear impact collision, engulfing both cars in flames. But those memories are often way oversimplified. Little Rock and the Montgomery bus boycott were just two battles in a fight for civil rights that went back to the end of the Civil War. Likewise, the Cuyahoga […]
McAfee sideshow eclipses Defcon’s real security breakthroughs | Security – InfoWorld
The onetime technology wunderkind, who left a job working for Lockheed to turn his curiosity about computer viruses into a thriving, global corporation showed up at two Las Vegas hacker cons last week: B-Sides Las Vegas and DEFCON. He offered some off-the-cuff rebukes to firms like Google. He also rambled long and hard about the dark forces that pursue him: the U.S. government, the government of Belize, Central American drug cartels and script kiddies desperate for his (virtual) scalp. Everywhere he goes, people take his picture. Who are they working for? The phones and computers he buys are bugged. His movements are being tracked. Those in attendance were admonished to beware of government snooping — especially via mobile applications. “Without privacy there is no freedom,” McAfee intoned. Listening to McAfee rant, it’s easy to forget there were plenty of folks walking the halls of Defcon, Black Hat, and B-Sides […]
PasswordsCon Preview: Passwords Are Dead. Long Live Passwords.
I had an opportunity to sit with Per Thorsheim, co-founder of PasswordsCon about next week’s Passwords14 Conference in Las Vegas, Nevada. If you haven’t checked it out before, PasswordsCon is the world’s premiere technical conference that is just focused on the security of passwords and pin codes. PasswordsCon is a one-of-a-kind event: bringing together folks whose specialty is cracking and defeating password security with security experts whose interest is in shoring up protections for sensitive data. This year’s conference, which is sharing space with the B-Sides Las Vegas Conference on August 5 and 6. PasswordsCon has earned a reputation for being the launching pad for some eye-popping new tools for password cracking. Back in 2012, we reported on a 25 GPU device that radically lowered the bar to cracking even the strongest passwords protected with weaker encryption algorithms, like Microsoft’s LM and NTLM, obsolete. Among other things, the Conference will feature […]