In this industry perspective, Thomas Hofmann, the Vice President of Intelligence at the firm Flashpoint* warns that the effects of data breaches can often be felt months or years after the actual incident, as stolen data bubbles up in underground marketplaces. He has three pieces of advice for companies that want to develop an incident response plan that mitigates the damage of breaches in the short term and over the long term.
Flashpoint
How To Make Your Intelligence Program Ready for Executive Consumption
In this Industry Perspective, Thomas Hofmann of the firm Flashpoint* writes that cyber threat intelligence professionals from the government don’t just bring their skills when they migrate to the private sector – they bring their jargon, also. Communicating effectively with the C-suite, however, demands making threat intelligence ready for executive consumption.
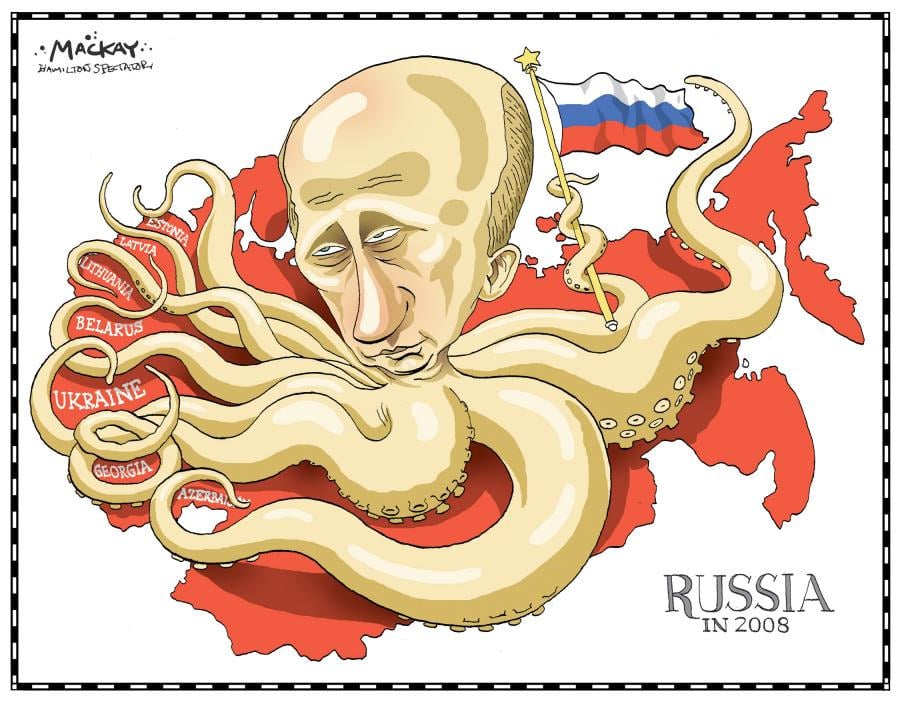
Spotlight Podcast: Is Russia rethinking its Cyber Offense?
If 2016 and 2017 saw aggressive efforts by the government of Russia to use hacking and online information operations to influence politics in the U.S. and Western Europe, 2018 may see the country reckoning with the aftermath of those campaigns. And that may result in a rethink of the utility of online information and hacking operations, says Flashpoint in its Business Risk Intelligence report.
Episode 79: Hackable Nukes and Dissecting Naughty Toys
In this week’s Security Ledger Podcast episode, the UK -based policy think tank Chatham House warned last week that aging nuclear weapons systems in the U.S., the U.K. and other nations are vulnerable to cyber attacks that could be used to start a global conflagration. We talk with Eddie Habbibi of PAS Global about what can be done to secure hackable nukes. Also: with CES raging in Las Vegas last week, we go deep with security researcher Jay Harris on flaws in connected toys being sold to children.
A New Great Game: Russia, China, North Korea heighten Cyber Risk
In-brief: Russia, China and North Korea are increasingly willing to use offensive cyber operations to weaken their enemies, including the United States, according to a report by the firm Flashpoint, which released its Business Risk Index report on Tuesday.