In-brief: The hack of VTech, a maker of technology products for children, has exposed sensitive data on hundreds of thousands of children, the company acknowledged this week. Also exposed: the toy industry’s growing and unregulated appetite for information on the children who play with their toys.
Education
Study: Energy, Utilities Struggle with Security Readiness
In-brief: a survey of key sectors found that energy and utilities firms are struggling to reduce their risk of an attack.
On the Internet of Things, Failure is a Virtue
In-brief: Cisco’s Marc Blackmer argues that fail fast, fail often is as relevant to securing the IoT as it is to developing new IoT products.
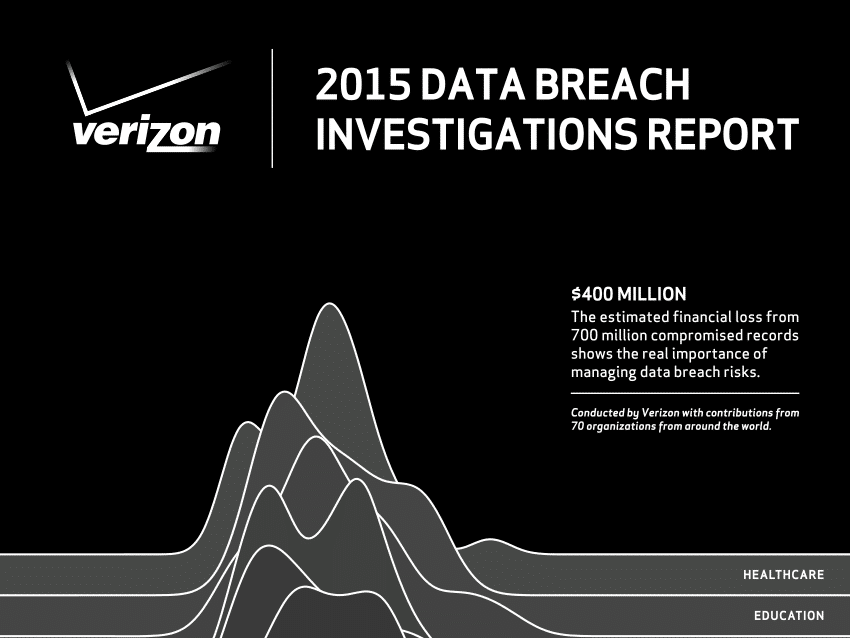
Verizon: Internet of Things Hacks Pose Little Risk – For Now
In-brief: Verizon said in its latest Data Breach Investigations Report that threats from Internet of Things technologies were more theory than practice in 2014, but that 2015 could see IoT devices play a role in breaches.
MIT Does Full Court Press on Cybersecurity Research
In-brief: MIT, the East Coast’s leading technical university, will announce three, major cyber security initiatives aimed at web-based security, critical infrastructure and cyber policy.