Kaspersky Lab has a fascinating write-up of malware it is calling “DarkHotel.” The information-stealing software is believed to target traveling executives. Curiously, Kaspersky says the malware may be almost a decade old and is found only on the wireless networks and business centers of select, high-end hotels. Reports about targeted attacks on traveling executives are nothing new. However, the Kaspersky report (PDF version here) may be the most detailed yet on a specific malicious software family that is devoted to hacking senior corporate executives. According to Kaspersky, the DarkHotel malicious software maintained a presence on hotel networks for years, with evidence of its operation going back as far as 2007. The malware used that persistent access to target select hotel guests, leveraging check-in/check-out and identity information on guests to limit attacks to high value targets. Targeted guests were presented with iFrame based attacks that were launched from the hotel’s website, […]
Defense Industrial Base
The IoT Comes To Chicago: IoT World Forum
The Internet of Things is increasingly an industry unto itself, with the conferences to prove it. And “no,” I’m not just talking about The Security of Things Forum – Security Ledger’s own IoT and security show. (Videos from our first annual show are now available, by the way. Register to view them here.) No: there are forums and symposiums focused on all different aspects of IoT: smart cities, design, wearables, and so on. There’s O’Reilly’s Solid, GigaOm Structure and any number of smaller, regional events. I’m at one of the more prominent IoT shows this week: The Internet of Things World Forum (IoTWF), which is sponsored by Cisco Systems. I’m moderating a really interesting panel that addresses a critical issue: the ways in with information technology (IT), operations technology (OT) and consumer technology (CT) converge in the IoT. These are three areas that, until recently, were separate. But a variety of developments […]
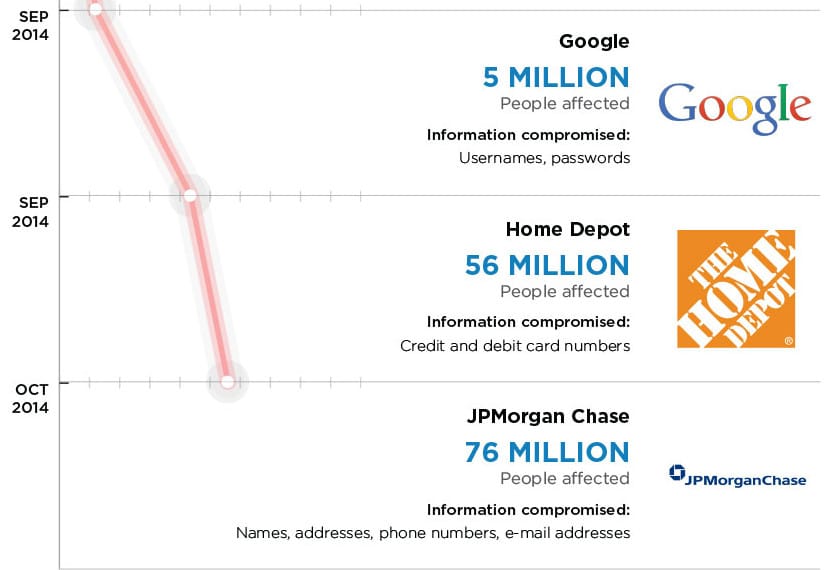
White House Cyber Chief: JP Morgan Underscores Critical Infrastructure Risk
The White House’s cyber security czar, Michael Daniel, said the Obama Administration is deeply concerned about the reported hack of systems belonging to banking giant JP Morgan Chase & Co. but sees the incident as part of a larger trend of attacks against U.S. critical infrastructure. Asked about the targeted attack against JP Morgan and other banks and financial institutions, Daniel said that the White House was concerned, but not surprised by the incident. “We have watched for several years the trend of malicious actors in cyber try to figure out how to target critical infrastructure,” he said. “Financial services is critical infrastructure.” The White House was concerned that a major U.S. bank would fall victim to hackers, but sees it in the context of a “broad trend,” rather than an isolated incident, he said. Speaking with Michael Farrell, the Cybersecurity Editor at Christian Science Monitor, Daniel hit on many of the now-common talking […]
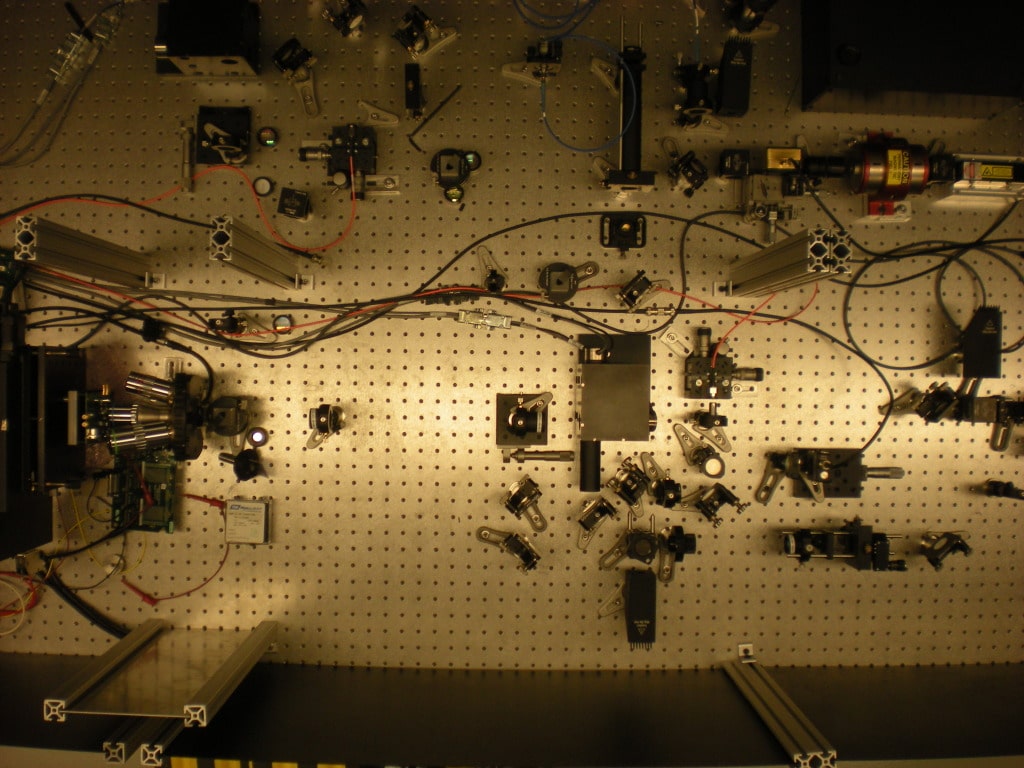
DARPA Tech Identifies Counterfeit Microelectronics
The U.S. Defense Advanced Research Projects Administration (DARPA) announced on Wednesday that advanced software and equipment it developed to spot counterfeit microelectronics in U.S. weapons and cyber security systems has been handed over to military contractors to continue development. DARPA said the product of its Integrity and Reliability of Integrated Circuits (IRIS) program: the Advanced Scanning Optical Microscope (ASOM) technology was transferred to the Naval Surface Warfare Center (NSWC) in Crane, Indiana, where it will be used to inspect microelectronics for signs of tampering or compromise. The technology was developed with the help of SRI International, an IRIS contractor. Read more Security Ledger coverage of supply chain risks. “The ASOM technology housed at NSWC Crane will help engineers provide forensic analysis of microelectronics, including integrated circuits (IC) confiscated by law enforcement officials,” DARPA said in a statement. The DoD is a major buyer of integrated circuit chips, which are mainly manufactured outside the U.S. […]
Senate Report Warns of Attacks on Military Transport Contractors
A Senate Armed Services Committee investigation has found evidence that hackers associated with the Chinese government compromised the computer systems of U.S. Transportation Command contractors at least 20 times in a single year. The attacks pose a serious risk to the system that moves military troops and equipment. The Committee released the report on Wednesday. (PDF copy here.) It presented the results of a year-long investigation of U.S. Transportation Command, or “TRANSCOM,” found a serious gap in awareness and reporting requirements. TRANSCOM was only aware of two of the 20 intrusions, while U.S. Transportation Command remained mostly unaware of the computer compromises of contractors during and after the attacks. “These peacetime intrusions into the networks of key defense contractors are more evidence of China’s aggressive actions in cyberspace,” said Sen. Carl Levin, D-Mich., the committee’s chairman in a published statement. “Our findings are a warning that we must do much more to protect strategically significant […]