Researchers at the firm ReversingLabs* reported on Thursday that they discovered two open source packages on the npm open source registry that contained malicious code. It is just the latest instance of malicious packages being discovered on a popular open source platform.
The packages have since been removed. However, the researchers warn that they lurked, undetected, on npm for months. Each had been downloaded hundreds of times before they were removed, raising questions about what other threats may lurk on popular open source platforms like npm, PyPI and GitHub.
In a blog post, ReversingLabs researcher Lucija Valentić said she discovered the open source packages while scanning npm, the popular open source package manager for node.js, the Javascript runtime environment. The first, nodejs-encrypt-agent, caught Valentić’s attention due to a number of characteristics that are typical of packages that are “typosquatting” – or imitating other, legitimate open source packages.
npm package names, numbers signal trouble
For example, the name of the npm page hosting the package didn’t line up with the name listed in the readme.md file, Valentić noted. Beyond that, the name in the readme.md file, agent-base, was the same as a popular npm package that is used to create the underlying socket that an application’s HTTP client requests will use.The nodejs-encrypt-agent also used suspicious version numbering. Though the earliest instance of the package dated to just two months prior, that package had a relatively high version number, 6.0.2 for what amounted to a version 1.0 release.

See also: Drive-By Malware Uses Google Sites for Drive by Download Attacks
Both techniques are characteristic of so-called “typo squatting” attacks in which malicious actors create malicious open source packages that closely mimic legitimate packages in the hope of fooling developers into integrating their wares. Upon further investigation, Valentić realized that the choice of that high version number was intentional: version 6.0.2 of the agent-base package that the malicious actors were squatting on has been downloaded over 20 million times – a large population of developers who might be fooled into downloading the malicious twin.
After analyzing the suspect package, ReversingLabs found that the package mostly reproduced the agent-base code, with one exception: the addition of a malicious PE (portable executable) that, upon further analysis, was identified as TurkoRat, an open source “info stealer” capable of a wide range of malicious actions, from writing and deleting files to executing commands and stealing sensitive information such as user credentials. ReversingLabs made the connection by correlating the javascript files extracted from the PE to the files found in the TurkoRat GitHub repository. The files matched almost perfectly, with minor variations, the company reported.
TurkoRat doubles up
Analysis of the nodejs-encrypt-agent also led to the discovery of a second malicious npm package that was hiding the TurkoRat malware: nodejs-cookie-proxy-agent. As with the nodejs-encrypt-agent package, the nodejs-cookie-proxy-agent was squatting on another legitimate package, node-cookie-proxy-agent.
ad a few versions available on npm, and was first published to npm two months ago. Our analysis show that the malicious package was removed from npm soon after it was discovered by ReversingLabs researchers and marked as malicious, which may explain why the last two versions of nodejs-cookie-proxy-agent (1.2.3 and 1.2.4) switched to embedding the nodejs-encrypt-agent, instead.
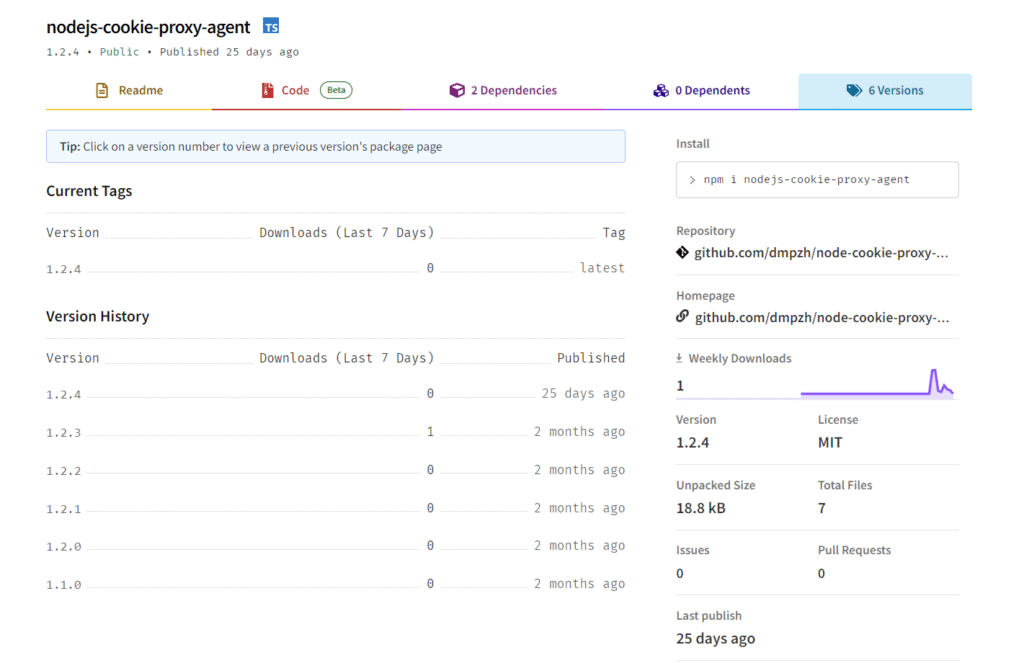
As with the nodejs-encrypt-agent, the code found in nodejs-cookie-proxy-agent also mirrors a commonly used, legitimate package node-cookie-proxy-agent. The timelines of the two attacks also were similar. The first version of nodejs-cookie-proxy-agent was published to npm two months ago and went undetected. Unlike the other package, however, attackers disguised TurkoRat as a dependency, axios-proxy, that was imported into every file found inside nodejs-cookie-proxy-agent versions 1.1.0, 1.2.0, 1.2.1 and 1.2.2. before switching to embedding the TurkoRat infected nodejs-encrypt-agent in the most recent versions.
Related: Want To Prevent Another SolarWinds? Start With Developers
Malicious npm packages had hundreds of downloads
The impact of the attack was limited. ReversingLabs said it saw evidence of around 700 downloads of the malicious nodejs-cookie-proxy-agent and around 500 downloads of the malicious nodejs-encrypt-agent over the last two months. Those would have placed the TurkoRat malware on developer systems and, potentially, those of downstream consumers of applications that relied on the malicious packages.
npm: not properly minded?
The larger question is how two open source packages containing clearly malicious code escaped detection by npm for more than two months. This isn’t the first time malicious packages were found lingering on the platform. However, like other open source registries, npm has boosted security capabilities in the face of growing threats to software supply chains. A subsidiary of GitHub (which is, itself a subsidiary of Microsoft), npm has introduced an audit feature that identifies vulnerabilities and dependencies that could pose security risks. GitHub has introduced automated code scanning to identify vulnerabilities.
Npm did not respond to a request for comment prior to publication on how the malicious packages escaped notice. We will update this story should the company respond.
Related: Episode 216: Signed, Sealed and Delivered: The Future of Supply Chain Security
Organizations struggle to identify threats such as malicious- or tampered with code in otherwise unremarkable packages. For example, a ReversingLabs analysis of the 3CXDesktopApp, a client VoIP application from the firm 3CX that was compromised by unknown actors found that attackers appended RC4 encrypted shellcode into the signature appendix of d3dcompiler.dll, a standard library used with OpenJS Electron applications such as 3CXDesktopApp. Another standard Electron application module, ffmpeg was modified with code to extract and run the malicious content from the d3dcompiler file. Such techniques are common among supply chain-focused cybercriminals and nation-state actors, but often escape the notice of existing application security testing technologies that are tuned to look for exploitable code flaws and vulnerable or out of date software packages.
All eyes on supply chain security
Software supply chains are becoming a preferred target of malicious actors. A report by the firm Sonatype said that number of documented supply chain attacks involving malicious third-party components increased 633% in 2022, with more than 88,000 known instances of supply chain attacks.
The federal government has taken notice. The FDA will require medical device manufacturers to attest to their cybersecurity and submit software bills of materials for devices seeking FDA approval. CISA, the Cybersecurity and Infrastructure Security Agency, recently published a guide with recommendations for secure development practices. In the meantime, the U.S. Congress is weighing whether to expand the agency’s responsibilities to include the security of open source software, according to reports.
Read about my ongoing work with ReversingLabs here.

