The pandemic accelerated the migration to digital services, with millions of U.S. consumers turning to the internet for everything from medical care to shopping and banking. But as consumers increasingly move their transactions online, criminals enjoy a landscape ripe for identity fraud.

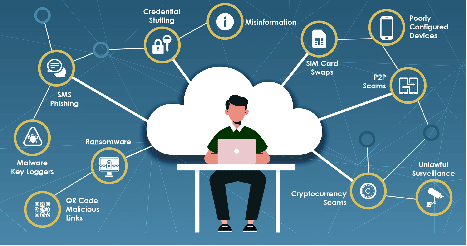
While the digital landscape offers convenience and accessibility, it also presents serious threats, particularly for companies and individuals who have failed to invest in appropriate security measures to counteract the risk presented by sophisticated cyber-attacks. Consumers, to a different degree, also represent risk for business enterprises because cyber criminals consider them an easy target for credential theft.
The Increasing Risk of Automated Threats
Criminals are evolving quickly to take advantage of new vulnerabilities in the digital landscape. Institutions, e-retailers and consumers need to exceed those efforts to stay ahead of the threat.
Spotlight Podcast: Flashpoint’s Allison Nixon on SIM Swapping and the Looming Online Identity Crisis
As we prepare for an increasingly digital future, everyone must factor in the persistent and growing risk of cyberattacks. Javelin’s 2022 Identity Fraud Report cites a noteworthy return to pre-pandemic criminal behavior. Automated threat vectors ranging from AI-powered bot networks to credential stuffing attacks represent threats that require expert business strategy.
Spotlight Podcast: RSA CTO Zulfikar Ramzan on confronting Digital Transformation’s Dark Side
Consumers, while vulnerable on multiple levels, are not security experts. That’s why, as professionals, we have to regain some ground on authentication by automating it to the extent that it blends into the background of every client experience so that access to sensitive accounts becomes smoother for the true accountholder and more of an impossibility for the cybercriminal.
The Virtual Battleground
Javelin research notes that consumer trust in advanced authentication practices is at an all-time high. Consumer respondents, for example, trust biometrics ranging from facial scans to fingerprint technology. With nearly 70% of consumers expressing their trust in advanced authentication methods it only makes sense for corporates to liberate the business enterprise from ineffective static passwords by deploying next-generation behavioral and device-based biometrics to the next roadmap iteration.
From analyzing keystroke cadence to mouse use, consumers’ natural behavior and characteristics provide multiple data sources to verify that users are who they say they are–and quickly shut down illicit attempts to create a flood of new accounts at once.
A Landscape of Opportunity
Identity fraud is a multi-pronged threat, and corporates can’t afford to combat it with a one-dimensional defense. Innovators in cybersecurity and fraud prevention have to be given the required amount of permission to build out a long-term layered approach to continuous authentication. Can this monumental effort be achieved in three to six months? Probably not. Consider, instead, a short term three-year plan that involves a logical approach to marrying new forms of technology together with your overall capability as an organization. The client experience cannot suffer stumbles throughout this period. When we say that all stakeholders have to be onboard –it is no exaggeration.
Technology is evolving quickly. Embrace this opportunity to lean into an entire universe of new security capabilities. Just remember that thoughtful and strategic planning is the only way to stay ahead of the virtual threats we are all facing today.


Pingback: The Concerning Statistics About Mental Health in Cybersecurity – Raymond Tec
Pingback: How Vulnerability Management Has Evolved And Where It’s Headed Next – Raymond Tec