Podcast: Play in new window | Download (Duration: 49:53 — 68.5MB) | Embed
In this week’s episode of the podcast (#223), we are joined by Josh Corman and Lisa Young of the COVID task force at CISA to talk about the agency’s work to improve the security of critical sectors of the U.S. economy. Job #1: erase the so-called security “poverty line” that keeps small, poorly resourced firms from obtaining the skills and talents they need to protect their networks, data and IT assets.
The phrase “let them eat cake” may have never been uttered by the French Queen Marie Antoinette. But the phrase has stuck to her for centuries – less because of its historical accuracy than for an attitude it epitomized: the detachment and callousness of the French monarchy and landed aristocracy in the face of widespread, abject poverty and hunger.
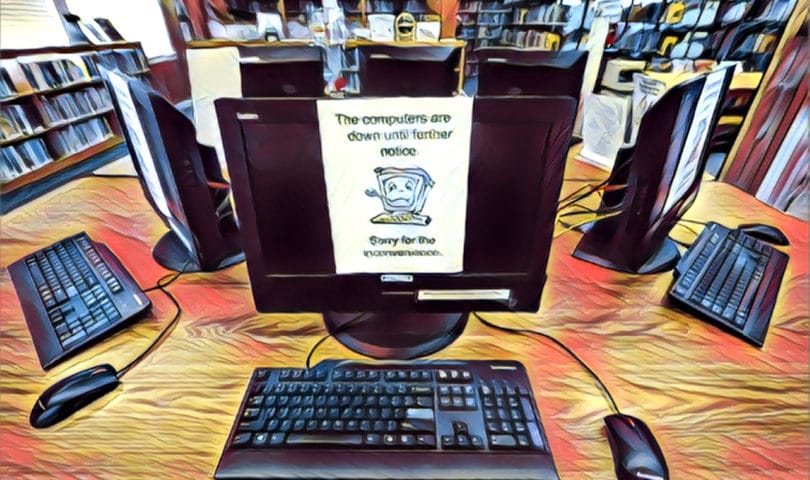
But a very similar attitude is at work these days in the information security space. Rather than standing on a balcony and calling for cake today’s cyber security cognoscenti instead mount stages at events like Black Hat and RSA and serve up rich desserts like “zero trust” to throngs of fellow cognoscenti. Outside the conference ballrooms, however technologically impoverished organizations in the for-profit, non-profit and public sectors are being ravaged by ransomware, data theft and corporate espionage, business email compromise scams and denial of service attacks.
Laissez-les utilizer ‘zero trust’!
Just as the aristocracy failed to apprehend the depths of hunger and poverty in society at large, large and wealthy information security firms, Industry ISACs and even federal agencies these days have failed to appreciate how unattainable “zero trust” networking is for a company with a constrained budget and without a dedicated security staffer – let alone a team.
Microsoft adds voice to calls for federal cybersecurity agency
Those gaps – between a small number of wealthy and sophisticated firms and everyone else- are getting wider. Sadly, much of what passes for official guidance is targeted to the 1% of firms that can afford the latest technology and services, not the 99% of firms that can’t. Cybersecurity, it turns out, has an equity problem, also.
One agency that is trying to change that is CISA, the Cybersecurity and Infrastructure Security Agency. The federal government’s point agency for cyber is young enough to be in the teething stage, but in recent months it has taken steps to address what analyst Wendy Nather termed the “security poverty line” head on. As we noted back in episode 204: that started with work to shore up the COVID vaccine supply chain, which was heavily reliant on a large number of small, specialized equipment and component makers, most of whom lacked any permanent IT security staff.
Now the agency is expanding its work to other “NCFs” or “national critical functions. The agency is offering hygiene services like free vulnerability and application security scans for critical infrastructure providers. CISA is also trying to simplify the conversation around cybersecurity and best practices. A new site on the agency website is collecting “bad practices” – behaviors that are common and “exceptionally risky” that organizations should avoid at all costs.
RSA Recap: CTO Zulfikar Ramzan talks about Trust, Zero Trust and the Debate over Going Dark
But bridging the wealth gap in infosec is a big project with a lot of moving parts. In this episode of the podcast, I sat down with two people who are in the trenches of that effort.

Lisa Young is an Analyst on the CISA COVID Taskforce 
Josh Corman is the Chief Strategist of the CISA COVID Task Force.
Josh Corman is the Chief Strategist for CISA COVID Task Force. Lisa Young works alongside Josh as an analyst. She is the VP of Cyber Risk Engineering at Axio. In this podcast Josh, Lisa and I talk about the monumental challenge of not just identifying and advocating best practices, but of operationalizing them – broadly – across the economy. Doing that, they say, means confronting the information security poverty that is rampant across industries and meeting companies “where they are” rather than preaching to them about what they should be.
I started off by asking Josh and Lisa to talk about CISAs latest initiative: “Get your Stuff off Search” a program to educate rank and file IT admins about IoT search engines like Shodan and Thingly that can find exposed industrial control systems and other specialized hardware that malicious actors use to target organizations.
As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. You can also listen to it on iTunes and check us out on SoundCloud, Stitcher, Radio Public and more. Also: if you enjoy this podcast, consider signing up to receive it in your email. Just point your web browser to securityledger.com/subscribe to get notified whenever a new podcast is posted.

Pingback: Episode 223: CISA Looks To Erase The Security Poverty Line | Ad Blocker Testing
Pingback: Spotlight: E-Commerce’s Bot and Mouse Game – Raymond Tec
Pingback: Episode 231: Solving the US Endemic Cybersecurity Worker Shortage