Neopets, a website that allows children to care for “virtual pets,” has exposed a wide range of sensitive data online including credentials needed to access company databases, employee emails, and even repositories containing the proprietary code for the site, according to information shared with The Security Ledger.
The data includes the IP addresses of Neopets visitors, information that could be used to target Neopets users, according to independent researcher John Jackson, who said he discovered the information after scanning the company’s website with a security tool.
Stolen Accounts For Sale
Neopets is a “virtual pet website” that first launched in 1999. It permits users – many of them children – to care for virtual pets and buy virtual items for them using virtual points earned in-game (Neopoints) or with “Neocash” that can be purchased with real-world money, or won in-game. Purchased by Viacom for $160 million in 2005, in 2017, it was acquired by the Chinese company NetDragon.
In an email to The Security Ledger, Jackson said that he noticed Neopets accounts being offered for sale on an online forum. That prompted him to run a scan on the Neopets site using a forensics tool. That scan revealed a Neopets subdomain that exposed the guts of the Neopets website, Jackson said via instant message.
China Using Big Brother-Like System to Track, Monitor Minorities
“We looked through and found employee emails, database credentials and their whole codebase,” he said.
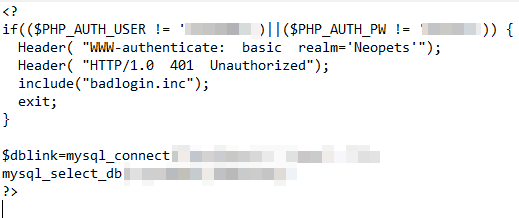
Jackson shared screen shots of the Neopets directory as well as snippets of code captured from the site that suggest credentials were “hard coded,” or embedded in the underlying code of the website. Working with security researcher Nick Sahler, Jackson was able to download Website’s entire codebase, revealing database credentials, employee emails, user IP addresses and private code repositories. The two researchers also uncovered internal IP addresses and the underlying application logic for the entire Neopets application.
“This is extremely bad because even though we didn’t attempt to access PII (personally identifying information), with these codebases we can undoubtedly do so,” Jackson said. “They need to fix the root issues, otherwise they will suffer yet another threat-actor related breach.”
U.S. Customs Data Breach Is Latest 3rd-Party Risk, Privacy Disaster
Jackson and Sahler said they have reported their findings to Neopets and provided copies of email exchanges with a support tech at the company who said he would pass the issue to “one of our coders.”
In an email statement to The Security Ledger, Neopets acknowledged finding some information exposed via an “old monitoring server,” but asserted that no user information was exposed.
This is the second serious security incident involving the Neopets site. In 2016, the company acknowledged a breach that spilled usernames, passwords, IP addresses and other personal information for some 27 million users. That breach may have occurred as early as 2013, according to the website HaveIbeenPwned.
The issue appears to be related to a misconfigured Apache web server, Jackson said. Though many web-based applications are hosted on infrastructure owned by cloud providers such as Amazon, Google or Microsoft’s Azure, leaked documents indicate that the 20 year-old Neopets website continues to operate from infrastructure it owns and operates.
Episode 145: Veracode CTO Chris Wysopal and Life After Passwords with Plurilock
Misconfigured web servers are a frequent source of security breaches -whether self-hosted or hosted by a third party. In 2017, credit rating agency Equifax acknowledged that a hole in the Apache Struts platform first identified in March, 2017 and patched in August of that year was used by hackers to compromise a web application and gain access to the information which included names, email addresses and, for US residents, Social Security Numbers. The vulnerability, identified as CVE-2017-5638, was associated with a string of attacks in 2017 and 2018.
Neopets: Old Server To Blame. No User Information Exposed
In an email to The Security Ledger on Monday, a Neopets spokesperson acknowledged that the company “found that some information that was publicized was from an old monitoring server with some folders of web page code exposed.” The code in question “only contained old internal testing data, including fake email and street addresses for internal testing purposes, which are no longer in use.”
The company “did find that an Industry Standard Server Status Page” containing “very limited current connectivity information” was “able to be accessed in specific instances.” Neopets has “cleaned up some areas that were found with old data and reviewed all touchpoints involved,” according to the email statement.
The spokesperson wrote that no user information was exposed in the breach. “After looking into the claim, we’ve verified that all personal user information remains securely protected, and no current data was exposed.”
“User data and the security of our site is extremely important to us. As we continue to make sure all data is completely secure, we’d like to reassure the community that no user or account information was accessed,” Neopets said in its statement.
High Bar for Collecting Information on Children
The breach could spell legal trouble for Neopets and its parent company, NetDragon. Online firms that manage information on children are held to a high standard under the federal Children’s Online Privacy Protection Act (“COPPA”).
In June, the U.S. Federal Trade Commission (FTC) announced that it reached a settlement with children’s mobile application developer HyperBeard Inc. that included a $4 million fine for COPPA violations for obtaining parental consent before processing children’s personal information for targeted advertising. (HyperBeard ultimately paid just $150,000 of that penalty, citing an inability to pay the full amount.)
In September, 2019 Google and its YouTube subsidiary agreed to pay a record $170 million fine to settle allegations by the Federal Trade Commission and the New York Attorney General that the YouTube video sharing service violated COPPA by illegally collecting personal information from children without their parents’ consent.
Editor’s Note: this story was updated to include comment from a Neopets spokesperson. PFR 12/29/2020


Pingback: Neopets Is Still A Thing And Its Exposing Lots of Sensitive Data | OSINT
“Jackson was able to download Website’s entire codebase”
Isn’t that illegal?
Like, once you find the vulnerability or bug, aren’t you supposed to privately report it to the affected party instead of making use of it to obtain private data?
Pingback: Update: Neopets Is Still A Thing And Its Exposing Sensitive Data – Yet Another News Aggregator Channel
thank you for sharing such great article with us