A group with links to the government of China was using hacking tools developed by the NSA even before they are believed to have been stolen, a new report contends.
New evidence has emerged that Chinese state-sponsored cyber criminals used hacking tools stolen from the U.S. National Security Agency (NSA) and released by the group Shadow Brokers in 2017 even before that leak occurred.
The news raises more questions about the cybersecurity at the beleaguered U.S. intelligence agency, which has struggled to keep sensitive information and its cyber arsenal under wraps.
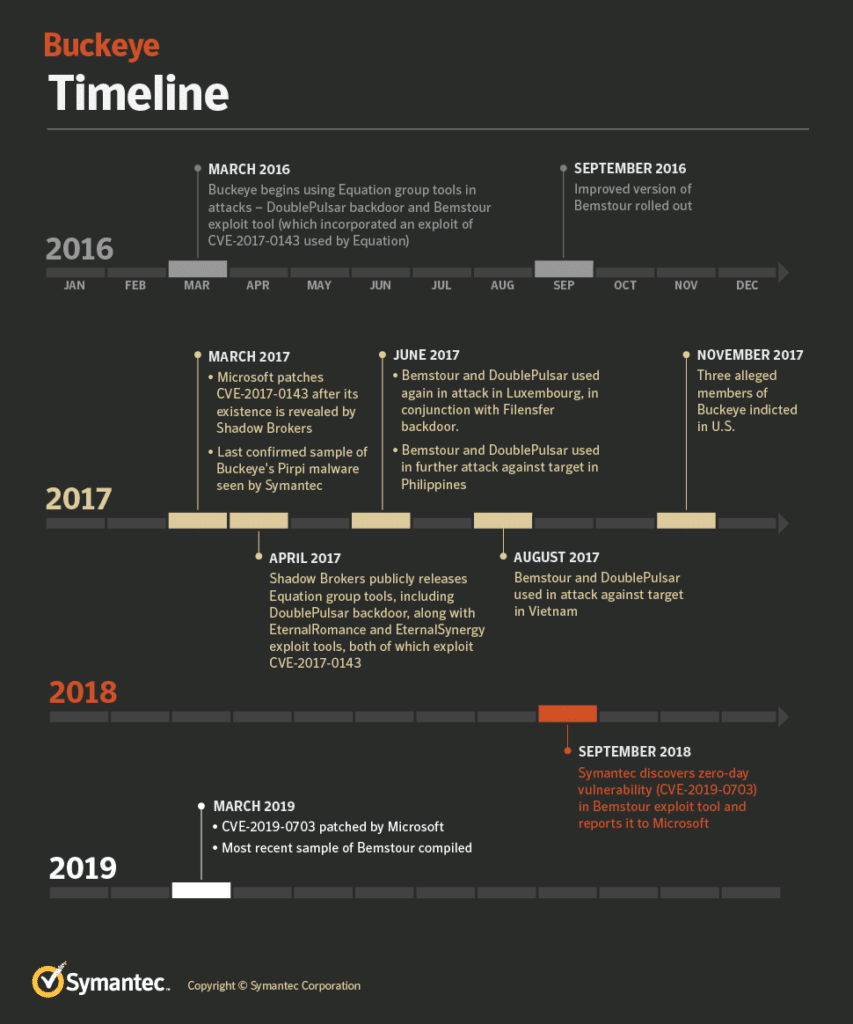
Security firm Symantec unveiled this week that in 2016, a Chinese-sponsored group called Buckeye, but also known as APT3 and Gothic Panda, used a variant the backdoor DoublePulsar, as well as a Windows exploit–both of which were released by Shadow Brokers as part of an Equation Group toolset the following year.
This suggests a potential breach at the NSA even sooner than the infamous Shadow Brokers’ release of the Equation Group tools, which “was one of the most significant cyber security stories in recent years,” researchers said in a blog post.
The Equation Group toolset was one of the NSA’s most valuable cyber assets: a package of powerful hacking tools with key exploits that, once released, were repurposed into two destructive pieces of malware: WannaCry and NotPetya. Both wreaked havoc across the globe, shutting down systems worldwide and resulting in hundreds of millions in damages for companies affected.
Collateral damage
However, losses like this seem to be collateral damage in the new era of cyber warfare, said Mounir Hahad, head of Juniper Threat Labs at Juniper Networks.
“Those who haven’t yet understood that confrontation between nations has already moved into the cyber space have to wake up,” he said.
It also shows how–just as in more traditional types of global conflicts—weapons being stockpiled by nation-states for cyber warfare can be turned against the nation that developed them if they fall into the wrong hands.
Mysterious Trisis Malware Strikes Again
“Unfortunately, in cyber warfare, you always run the risk of losing at least a portion of your weapons to the adversary. But it’s a price you have to pay because the alternative of just defending yourself is not an option,” Hahad said.
It does not appear that Buckeye actually stole the tools, however. Symantec researchers believe that the group merely fashioned its own tools after observing NSA’s use of the tools in the wild, researchers said.
“Based on the timing of the attacks and the features of the tools and how they are constructed, one possibility is that Buckeye may have engineered its own version of the tools from artifacts found in captured network traffic, possibly from observing an Equation Group attack,” researchers wrote.
What is clear is that in March 2016, Buckeye began using the DoublePulsar backdoor, using the Bemstour exploit tool to deliver it to targeted computers in Hong Kong. Bemstour exploits two Windows vulnerabilities to achieve remote kernel code execution–one is a zero-day vulnerability (CVE-2019-0703) discovered by Symantec. The second, CVE-2017-0143, was used by two exploit tools—EternalRomance and EternalSynergy–released as part of the Shadow Brokers leak. Microsoft patched the latter exploit in March 2017 after that leak, Symantec found.
Iran Taps Chafer APT Group amid Civil Aviation Crisis
“Bemstour is specifically designed to deliver a variant of the DoublePulsar backdoor,” researchers explained. “DoublePulsar is then used to inject a secondary payload, which runs in memory only. The secondary payload enables the attackers to access the affected computer even after DoublePulsar is removed.”
War games
While little is known about Shadow Brokers, Buckeye has a higher profile among security researchers. The group–known for exploiting zero-day vulnerabilities–has apparently been active since at least 2009, when it launched a flurry of espionage attacks against U.S.-based organizations, according to Symantec.
While Buckeye appeared to cease operations in mid-2017, the Equation Group tools it used continued to be used by unknown attackers until late 2018. Researchers said that either Buckeye gave them to another group or actually continued its cyber operations longer than researchers thought.
Back at ‘ya!
In the current cyber landscape, the lines between the “good guys” and the “bad guys” in the global cyber war is becoming blurred, with various nation states engaging in similar types of cyber espionage and cyber weapon stockpiling to get the upper hand on those launching cyber offensives against them.
Iran Taps Chafer APT Group amid Civil Aviation Crisis
This leads to scenarios in which outcomes–such as a massive cyber attacks like NotPetya and WannaCry–which the tools themselves were developed to try to prevent, said Ray DeMeo, co-founder and COO of application security firm Virsec.
We should be thinking a lot more about defense, rather than risky offensive moves.
Ray DeMeo, COO Virsec
“Unlike conventional weapons, most cyber weapons exploit long-dormant vulnerabilities in widely used applications and platforms like Microsoft Windows,” he said. “Keeping a widespread vulnerability secret and hoping that no other players discover it is inherently dangerous. Plus, if using a new cyber weapon allows your adversary to grab it, improve upon it, and turn it against you, then we should be thinking a lot more about defense, rather than risky offensive moves.”
That scenario and proof that China had NSA cyber weapons in advance of the Shadow Blocker leak shows that the world has “entered a new level in the cyber arms race,” which will continue to escalate as tools used in cyber war continue to become more sophisticated, DeMeo said.

