Podcast: Play in new window | Download (Duration: 26:19 — 30.1MB) | Embed
Countless Congressional hearings, 48 state data privacy laws and GDPR and mega breaches like the discovery of data on 500 million Facebook users just keep happening. Why? In this episode of the podcast, Paul is joined by experts from the firm BitSight and BigID to discuss why we can’t seem to stop the breaches.
“Never again” is a common refrain you hear uttered after tragedies like wars, financial scandals, famine or other man-made disasters. Alas: you don’t hear the phrase often after a data breach. That’s for good reason. As terrible and eye-popping as they may be, massive data breaches JUST. KEEP. HAPPENING, with a regularity and severity that are numbing.
Last week was a good example of what has become the new normal. In the space of a few days, the firm UpGuard Security disclosed the discovery of data on more than half a billion Facebook users that had been abandoned on Amazon’s S3 cloud based storage service. Around the same time, there was news of 300,000 more records from Voter Voice, a grassroots advocacy group , were left exposed on a misconfigured server. Also: FEMA, the federal emergency management agency leaked data on 2.5 million disaster victims.
Asus ShadowHammer suggests Supply Chain Hacks are the New Normal
Despite countless congressional hearings and data security and privacy laws in 48 states, and the advent of GDPR, data breaches show no signs of fading into memory like small pox or polio. Why? To find out, we invited two experts into the SL studio this week:
Jacob Olcott is the Vice President of Communications and Government Affairs at Bitsight, a firm that tracks third party cyber risk. Also joining us on this podcast is Dimitri Sirota, the CEO of the firm BigID, which does data governance for sensitive data.
To hear Jake and Dimitri talk: the key to understanding why data breaches continue to happen, you have to understand the underlying causes of such breaches, including the difficulty organizations have understanding what sensitive data they own and how it is used.
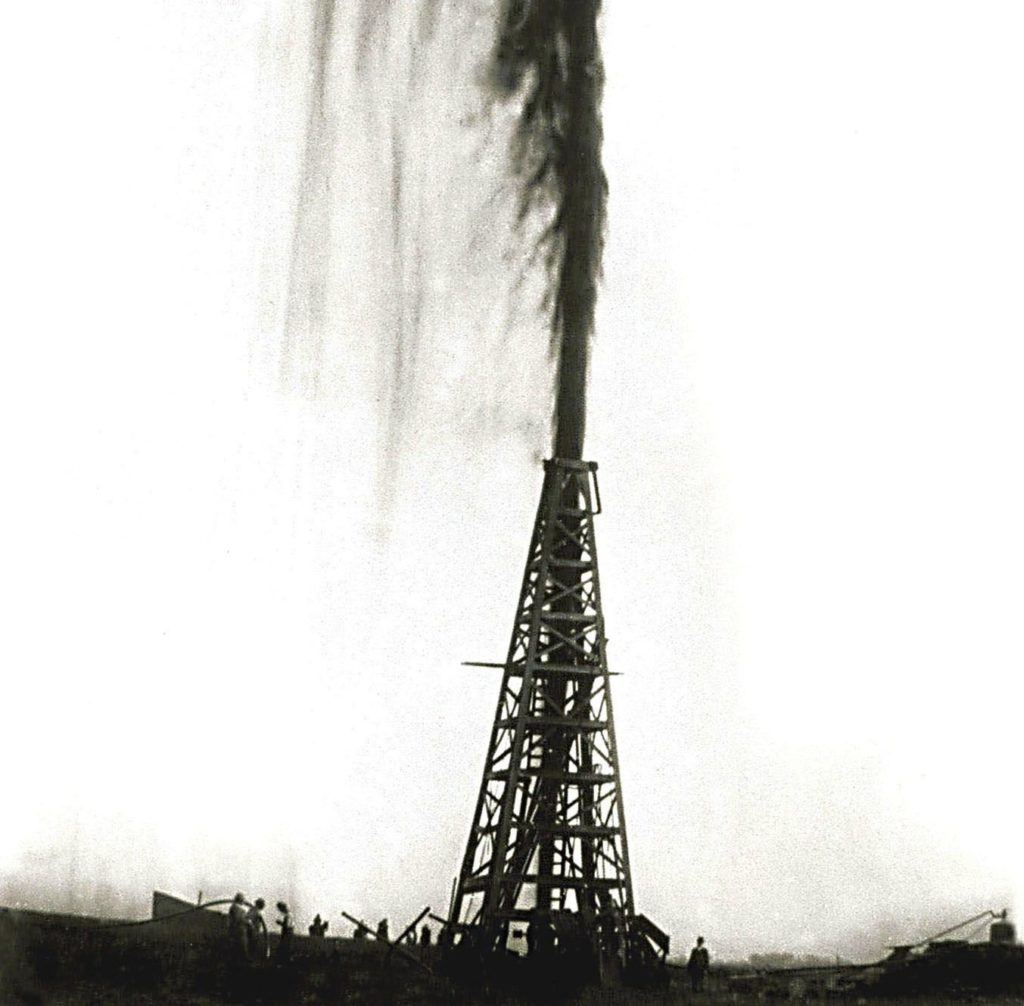
Gushers of Data
One major cause of breaches is simply a lack of sophistication among corporations and other organizations. Sirota notes that data is often described as “the new oil,” but there may to be more to that metaphor than meets the eye.
Taking the Long View of Breach Fallout
Data is an exploitable resource, yes. But like oil, its easy for data to leak and seep from one container to another. When it leaks, it can cause a big mess that’s difficult to clean up. And, increasingly, companies are having difficulty tracking those movements and keeping a lid on their data reserves, he notes.
Supply Chain Complexity bites
The other issue is complexity, says Olcott. Specifically: organizations’ growing use of third party service and application providers, mobile workers and contractors. Modern organizations might have hundreds or even thousands of third party providers, he said.
That complex supply chain is a fat target for malicious actors bent on obtaining sensitive data or access.
“As folks have spent more time and effort on their own cyber security performance, the bad guys have realized that the other thing that has taken place is the expansion of the business ecosystem and all the outsourcing that has taken place over the last number of years,” Olcott told me. “The bad guys are just looking at how to exploit the weak links in the supply chains.”
Check out our full conversation above!
As always, you can check our full conversation in our latest Security Ledger podcast at Blubrry. You can also listen to it on iTunes and check us out on SoundCloud, Stitcher, Radio Public and more.

