Bogus LinkedIn job postings for leading US organizations, including the US Army, the State of Florida and defense contractor General Dynamics, are popping up for Russian locales like St. Petersburg and Moscow, the firm Evolver has found. Is it AI-Gone-Wild, or is something more nefarious afoot?
Moscow, on the border between Idaho and Washington State, is probably about as far as you can get from Moscow, Russia–in miles, cultures or ideologies. However, the two “Moscows” have something in common: they are both listed as the location for a job position for a company called Enterprise Medical Service on LinkedIn.
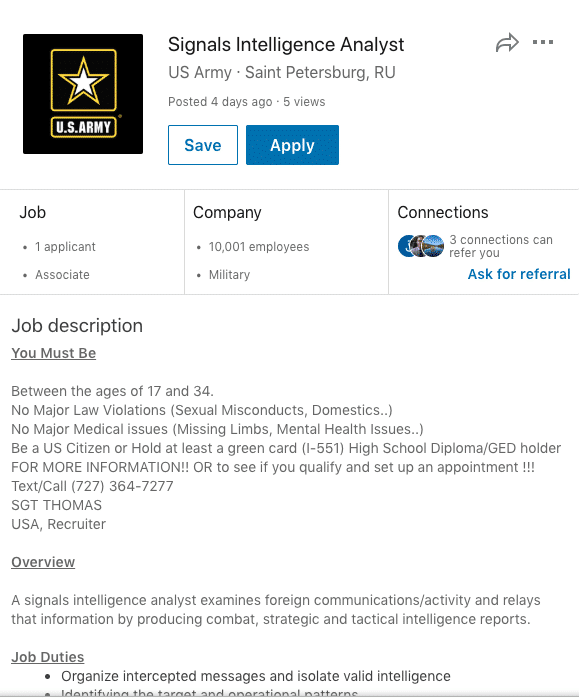
The company isn’t alone. Researchers at the firm Evolver say that they have spotted job posts for countless firms including the US Army, the State of Florida and defense contractor General Dynamics listing locations in the Russian Federation, including cities like St. Petersburg and Moscow. Most of the companies affected have no Russian offices listed on LinkedIn.
In a blog post, Evolver said it noticed the problem while doing work for its clients to monitor and evaluatessocial media to detect potential threats. The company noticed the issue with a number of its clients, and worked with LinkedIn on behalf of those clients to have the phony ads removed. Block said LinkedIn has moved quickly to remove the job postings Evolver called to its attention but that the problem extends far beyond Evolver’s client base.
“The number of ads is too many to count at this point. It is extremely widespread and ongoing,” Chip Block, vice president of Evolver, told Security Ledger in an email. Just within recent days, Block said Evolver discovered ads for US Army Intelligence Analysts listing Saint Petersburg, Russia as the location. Clicking on the Apply button brings you to a posting at Emprego.pt, a jobs website based in Portugal, that lists the correct location of the posting: St. Petersburg, Florida.
Block said the purpose of the bogus ads is unclear, but seems suspicious, if not malicious. “We are pretty sure this is a man-in-the-middle data capture scheme,” he told Security Ledger. “If you go to the links, you are asked to enter your e-mail before being redirected to the job site. This is not being done by LinkedIn, but someone external. Someone is using this to capture emails and create potential targets,” he said.
The Russian connection
Take the example of Enterprise Medical Recruiting headquartered in Missouri. The company–which does medical recruitment nationwide–does currently have an advertisement for a job opening for a family medicine provider on LinkedIn. The position is based in Moscow, Idaho. However, the location for the listing on LinkedIn is Moscow, Russian Federation–the Russian capital.
Moreover, when a potential applicant clicks on the “apply” link to do just that for the position, he or she is greeted not only in English, but in Russian.
Upon further digging, Block and his colleagues noticed more links to Russia in the Enterprise Medical Recruiting job posting for U.S. positions, with various advertisements surrounding the job posting also in Russian.
Moreover, the source of an ad in which a mix of Russian and English languages are shown in links is called Neuvoo, a Canadian job-search website. “However, if you go the Neuvoo site, these jobs do not exist in their search,” he told us.
At the very least, organizations caught up in this risk brand damage and the loss of potential job applications. Not just Enterprise Medical Group but the US Army and US defense contractor General Dynamics are being misrepresented as having a Russian connection. At the same time, applicants information is being improperly shared in other countries, and somebody is likely paying for clicks that are not going to the proper source,” Block said.
Enterprise Medical Recruitment is not the only company that appears to have offices in Russia on LinkedIn job ads. Listings for the State of Florida, University of Idaho and even Dollar Tree–among others–have ads that appear in searches when the location is set to Russian Federation.
When contacted, a LinkedIn representative thanked Security Ledger for calling the company’s attention to it.
“We’re investigating a potential issue with our job ingestion tool that seems to have incorrectly assigned the location of a job post on a small number of job listings,” the company said in an e-mailed statement. “Our team is working to resolve this issue.”
We contacted Enterprise Medical Recruitment repeatedly about the issue but the company did not respond by the time of this posting.
Potential ramifications
It is not immediately clear why the bogus ads are appearing but they do seem to cluster around postings in locations where a Russian namesake exists.
“Basically, if you look for any company posting jobs in St. Petersburg, FL and Moscow, ID, they will also be posted in Russia. From what we can tell, this has been going on for three months,” Block said.
Malicious actors could be using LinkedIn ads to collect personal user information or engage in click fraud – generating bogus traffic as part of a “pay per click” revenue generating scheme. The LinkedIn issue does appear to be a calculated attack, Block said. He outlined several reasons why the misinformation campaign could be dangerous for the companies involved.
“There are intermediary domains that are either capturing data from the person clicking on the post or providing data directly into the actual job posting company,” he noted. Additionally, Block said Evolver has traced the link patterns for job applicants and determined that there are redirects and intermediary links that make the scheme look like a traditional man-in-the-middle attack.
Malicious actors could be collecting the data of people responding to ads for U.S. job postings, as well as finding a way to infiltrate the companies themselves through links to those organizations, he said.
“That’s a great social-engineering mechanism,” Block told us. “If I clicked on this and went to someone in Russia and they are interviewing people–they think they’re interviewing with General Dynamics or Dollar Tree but they are not. But they’re giving up personal information as you would do in an interview.”
Block said his company has been focused on getting the fake job posts taken down. The underlying cause of the problem has not been addressed as of yet. However, given the current political climate, the companies misrepresented as having offices or jobs available in Russia also could face a branding issue that could tarnish the reputation of a business or its opportunity to hire qualified workers, he added.
“If people looking for jobs are looking at companies with operations in Russia, it’s considered a risk,” Block said.

Currently our company does not seem to be affected by this particular oddity. However, I did notice that when applicants apply for our jobs they are redirected to startwire.com which then asks them to create a profile. I was not aware this happened.
Spread the word!
Pingback: LinkedIn Says Glitch, Not FSB, to Blame for Russian Job Postings | The Security Ledger