Podcast: Play in new window | Download (Duration: 34:11 — 39.1MB) | Embed
In this week’s episode (#130): we speak with security researcher Troy Hunt, founder of HaveIBeenPwned.com about his latest disclosure: a trove of more than 700 million online account credentials he’s calling “Collection #1.” Also we speak to Martin Hagen of the Norwegian device firm Tailit about how failing a security audit of the company’s GPS watch sparked a security make-over at the company.
Yes, you’ve been pwned!
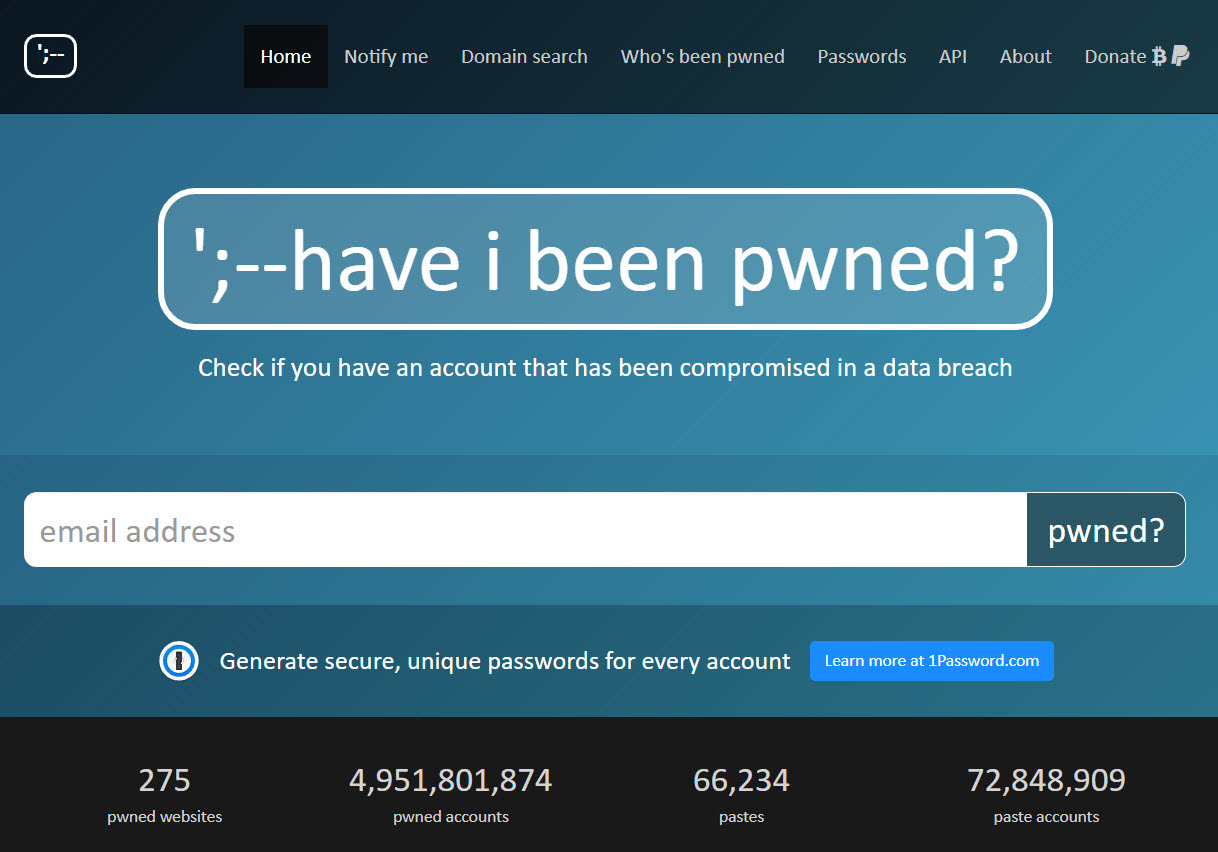
Troy Hunt made a name for himself calling attention to massive data leaks via his blog, troyhunt.com and – especially – haveibeenpwned.com, his online tool for checking to see if your credentials have been stolen. (They have.)
But even by Troy’s standards, the trove of email addresses, passwords and other data he uncovered last week was impressive: a 773 million strong archive of credentials spanning some 12,000 separate files that he dubbed “Collection #1.” A kind of “breach of breaches,” the collection represents the sum total of many leaks and credential thefts going back years. But Hunt said the treasure trove of credentials still poses a serious risk today. That’s especially true because we users aren’t learning the lesson about the need for strong, unique passwords to protect our accounts. One measure of that: despite containing credentials for more than 700 million accounts, Collection 1 revealed just 21 million unique passwords.
See also: Expert says: Hack your Smart Home to Secure It
Even more worrying: Collection #1 isn’t the only repository of stolen credential out there. In this interview Hunt talks about subsequent dumps he has come across since first publicizing Collection #1 last week. Collections 2-5 represent hundreds of gigabytes of data, Hunt told me, though it may be days or weeks before he has fully parsed it.
Troy last spoke with us back in Podcast Episode 123: HaveIBeenPwned’s Troy Hunt on Marriott’s Big Mess and GreatHorn on the Asymmetric Threat of Email. You might want to give a listen to that podcast, as well.
Tailit’s Tale of IoT Security Redemption
In our second segment this week: we’re used to hearing stories about connected device makers getting caught out with shoddy device security, insecure applications, dodgy data collection practices – or all three. But after the headlines have faded and the conversation has moved on, what is the best way for connected device companies to move on? Often it is by closing up shop, or by making apologies and then continuing as they were, in the hope of not getting caught again.
See also: More Questions as Expert Recreates Chinese Super Micro Hardware Hack

The Norwegian connected device maker Tailit is another example. In our second segment, we speak with Martin Hagen, the CMO at Tailit about how his company used revelations of a host of security flaws in a GPS smart watch for kids to accelerate security transformation at the company.
Among other things, Tailit hired teams of hackers to probe their personal GPS tracking devices. They invested heavily in software security, designing their own watch firmware to replace the default firmware of their China-based suppliers.
According to Hagen many of the biggest risks connected device makers face comes from third parties – the hardware and software suppliers they rely upon to create their product. Too often, he said, these devices lack basic security controls and sport default surveillance features that open device owners up to online exposure.
Check out our conversation in the second half of the podcast!

Pingback: Four More Collections, 700 Million Stolen Passwords Discovered | The Security Ledger
Pingback: Russian Cyber Criminal Named as Source of Massive Collection 1 Data Dump | The Security Ledger
Pingback: Waiting for Federal Data Privacy Reform? Don't Hold Your Breath. | The Security Ledger
Pingback: EU calls for End to Default Passwords on Internet of Things | The Security Ledger