Facebook used a blog post on Friday to describe, in detail, the systems that it uses to secure its vast social network, including custom designed tools and so-called “red team” hacks.
Securing a network with more than 1.5 billion users is no small feat. Just how big a job it is, however, became clearer on Friday after Facebook posted an extensive blog post describing its multi-layered approach to securing its platform.
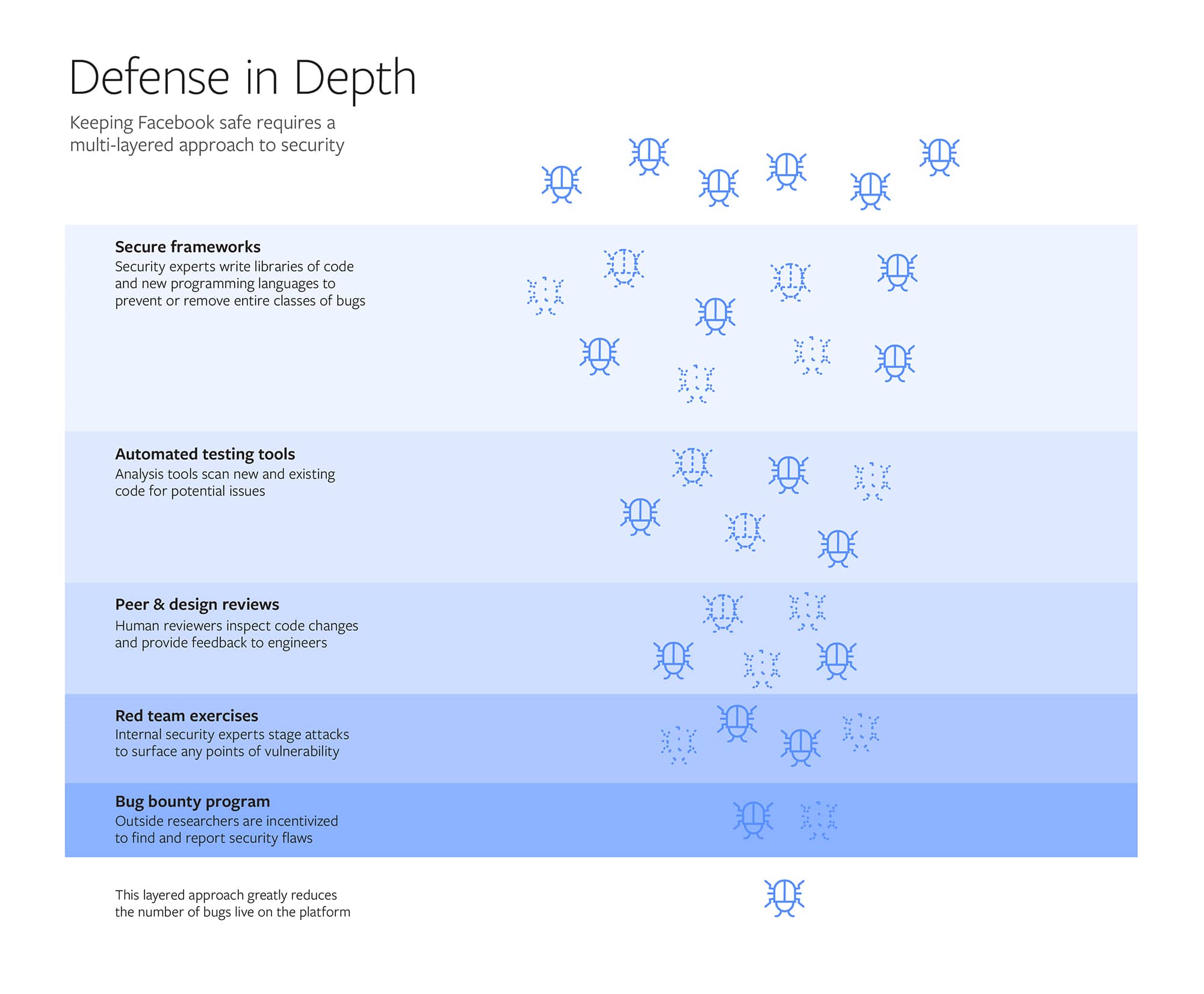
In a post on the company’s newsroom blog, Collin Greene, Facebook’s Manager of Product Security, describes what he calls a multi-layered system of defenses spanning everything from intensive developer education to the use of Facebook-developed secure coding languages like HACK (first introduced in 2014) to public bug bounty programs that invite the public to try to find holes in the social network’s technology.
Starting early: developer training
Facebook said its program starts early, with a mandatory, six week secure development “boot camp” for all engineers that teaches the fundamentals of secure development. That ensures that every engineer who joins the company knows “foundational security processes” used at the company.
Before Senate Facebook, Twitter Defend Efforts to Stop Fake News
And, while many companies must rely on the “kindness of strangers” (or third parties) to secure their products, a company with Facebook’s development resources has the luxury of designing their own. The company also program for new hires.
The company has invested in frameworks that eliminate entire classes of bugs when engineers write code, Greene explained. Likening the frameworks to “bumpers” on a bowling lane, he said Facebook frameworks like Hack, an extension of the PHP programming language, and XHP help developers avoid introducing errors by requiring them to explicitly define and type out certain variables and parameters in their code that might otherwise create vulnerabilities that external actors could exploit.
Report: Cybercriminals target difficult-to-secure ERP systems with new attacks
Post development, static and dynamic code analysis as well as a custom vulnerability scanning tool locates vulnerabilities in developed code, with Facebook performing a root-cause analysis on all flaws. “This analysis then feeds back into the other phases of our defense-in-depth approach. For example, it may lead to us building new coding frameworks, new tools or new training,” Greene wrote.
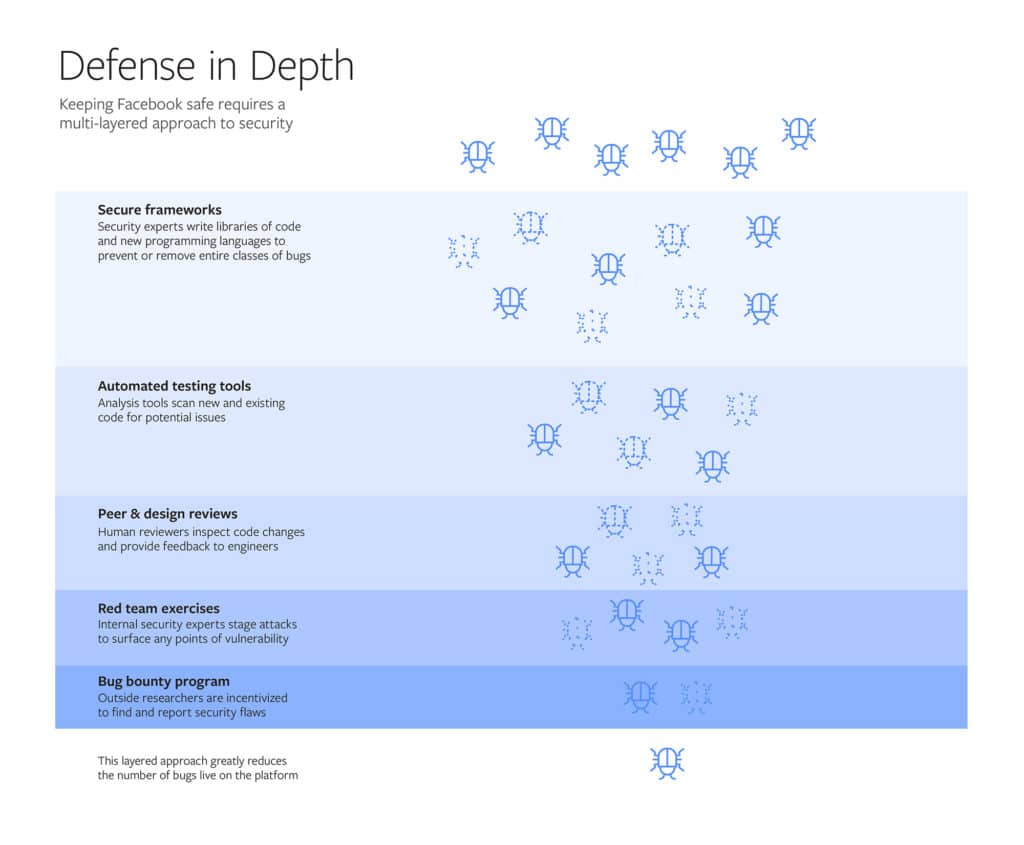
Facebook also makes extensive use of an internal “red team” to try to break software and systems it has developed as well as threat modeling and table top exercises that mimic how actual attackers would try to compromise the company’s network and systems.
Finally, Facebook offers both public and private bug bounties to skilled, “white hat” hackers. The company has paid over $7.5 million in bounties to researchers from more than 100 countries who have found flaws in its software and site, he said.
Facebook has faced intense scrutiny for security lapses in recent years. In addition to ongoing Congressional and law enforcement investigations into the misuse of its platform by operatives working on behalf of the Russian government, the company was forced to reset millions of user accounts in September after discovering a security flaw that exposed around 90 million user accounts to the risk of account takeover.
The sheer size and complexity of the Facebook platform makes security a challenge, said Gary McGraw of the firm Synopsys in an October, 2018 interview on Security Ledger podcast. That’s especially true at social media firms like Facebook, where the early push for rapid and agile development of new features often came at the cost of thoughtful planning and design.
You can listen to my full conversation with Gary in Episode #114 of our podcast here!

Thank you for sharing valuable and good information.