Data-management Veeam found itself in need of some self-help after mismanaging its own data with a misconfigured server that exposed more than 440 million e-mail addresses and other types of customer information.
Security researcher Bob Diachenko discovered that a MongoDB server operated by Veeam was left wide open and searchable for some days in the early part of the month until Sept. 9, when the company secured it after being contacted by Diachenko and TechCrunch writer Zack Whittaker, who also published an account of the debacle.
Diachenko discovered the server exposure on Sept. 5, he said in a blog post. He used IoT search engine Shodan to find the Amazon-hosted resource, “a 200-GB database [that] included vast [amounts] of data that is apparently used by Veeam marketing automation team to reach out to their customers using Marketo solution,” he wrote. Marketo offers account-based marketing software, including email, mobile, social, digital ads, web management and analytics.
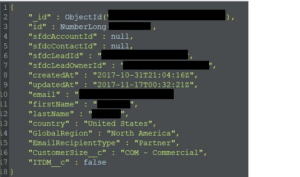
The server exposed a number of data collections–labeled “marketo,” “marketo_new” and “marketo-collect”–that in total stored more than 445 million records from a four-year period between 2013 and 2017, Diachenko said.
Information included in the collections and thus exposed were “non-sensitive” data such as customers’ first and last names; email addresses; email recipient types, i.e., whether they were customers or partners; and country or operation. The data inadvertently exposed also included what’s called attributes values–which in some cases have IP address, referrer URL address and user agent info–and the size of the customer organization, Diachenko said.
Mismanaging its own data is clearly a major faux pas for a company that heralds itself on its website as a pioneer in the evolving world of data management, aimed at helping customers “make data both intelligent, and ultimately, self-governing.”
Follow the data
At first Diachenko didn’t think the exposed database was one of Veeam’s, he said, believing it originated from a Marketo server. After further investigation and analysis, however, he realized he’d made the wrong assumption.
“I came to conclusion that data was part of Veeam marketing server infrastructure, rather than Marketo,” he said. Also, the fact that the database was secured shortly after he and Whittaker notified Veeam also seemed an obvious clue that it belonged to them, although as of Tuesday he said Veeam had yet to confirm his findings.
Veeam did not immediately reply to request for comment from Security Ledger on the exposure. However, the company did acknowledge to The Register in a statement that one of its marketing databases and therefore the data stored in it “was possibly visible to third parties for a short period of time.”
Even though the data exposed can be classified as non-sensitive, there still is ample room for bad actors to use the data for nefarious purposes, Diachenko said.
“The public availability of such large, structured and targeted dataset online could become a real treasure chest for spammers and phishers,” he wrote. “It is also a big luck that database was not hit by a new wave of ransomware attacks which have been specifically targeting MongoDBs (with much more extortion amount demand than it was last year).”
Data leaks involving both critical and non-critical information continue to be a persistent security issue, especially as data stores grow by orders of magnitude thanks to cloud-based storage and other more sophisticated technologies, and companies big and small try to wrap their heads around the security and management of it all.
Indeed, one researcher suggested it’s the growing pains of moving data to the cloud and new configurations based on services ke Amazon Web Services that caused glitches like this to happen, and suggested all companies take Veeam’s data exposure as a cautionary tale as they make these transitions.
“Transitioning to the cloud is a challenge, especially without a full understanding of the cloud’s security landscape,” said Pat Cable, senior infrastructure security engineer at cloud security company Threat Stack. “Organizations need to invest in strategies built around systems that monitor infrastructure in real-time and proactively identify risk hot spots before they are exploited.”
Earlier in the week in fact British Airways acknowledged that someone stole credit-card data from hundreds of thousands of its customers, while two weeks ago, China suffered its biggest data leak in five years when Huazhu Hotels Group admitted a breach affecting the phone numbers, e-mail addresses and other info from 130 million customers.


Pingback: Abine says Blur Password Manager User Information Exposed | The Security Ledger