Recent demonstrations of election hacks are about more than ballots. They also contain important lessons for enterprises, Security Ledger Editor in Chief Paul Roberts argues in this opinion piece.
(Note: this post first appeared on Hitachi Systems Security* web site.)
Did an 11 year old hack a state election website? Are voting machines easy prey for hackers? And does any of this matter to IT professionals charged with securing corporate networks from cyber attacks?
The answers to the above questions are: no, yes and YES!

As you probably have noticed, recent weeks have brought a flurry of news articles about the vulnerability of electronic voting machines and state election systems. They come ahead of important midterm elections in the U.S. in November and amid heightened anxiety about the integrity of elections systems.
Among the stories that made headlines: that it took an 11 year-old just minutes to change results displayed on the State of Florida’s website (or a facsimile of it) and this Politico op-ed from a 17 year old “not very good hacker” who also claimed to have hacked an election website. Both of those stories had their roots in the Vote Hacking Village, a staple of the annual DEF CON conference in Las Vegas, the massive gathering that some refer to as “hacker summer camp.”
News as they say is the “first rough draft of history.” The emphasis should be on “first” and “rough.” As Propublica pointed out: among the details in need of more explanation: the “state websites” that got hacked were not exact replicas of the sites that states like Florida use to display vote results, not to store the actual vote counts. Also, the kids hacking the sites were being coached by adults and provided with instructions and cheat sheets on how to find and exploit the vulnerabilities in the dummy web sites. Let’s call it an “open book test.”
[See also: As Election Threats Mount, Voting Machine Hacks are a Distraction]
Which isn’t to say that the Vote Hacking Village doesn’t have some important messages for IT professionals charged with securing enterprise networks from cyber attacks, insider threats and data loss. It does. Here are a couple Vote Hacking Village lessons for enterprises.
Take a risk-based approach, protecting what matters
Chief among the hidden lessons of the Vote Hacking Village is to protect what matters. Consider: elections are massively complicated, one-time events with a single purpose: to collect and tabulate votes for a range of candidates and issues on the ballot.
Attacks directed at state web sites that display unofficial vote counts are dramatic, yes. But they’re simply not as important as attacks directed at voting machines themselves (which collect votes) or the systems that tabulate and record votes at the state or local level. Such attacks could actually change the outcome of an election, which is a worst-case scenario if your job is protecting the integrity of the vote.
[See also: Voting Machine Maker Defends Refusal of White-Hat Hacker Testing at DEF-CON]
Professionals working in the enterprise also need to take a risk based approach to their own environment. As with elections officials: the challenge is to understand what IT assets and systems are critical to your organization’s mission and to direct human, financial and technology resources to securing those while not allowing yourself to be distracted by bright shiny objects.
As the Vote Hacking Village showed us, mission critical systems are often not those that are most visible or high profile. For example: if you work for a manufacturing firm, the hardware and software that keep your production line running, control the environmental conditions in your factories, manage your supply chain, employee payroll and so on are all mission critical. Your corporate website – while highly visible – is likely not a top priority. If, on the other hand, you’re an e-tailer whose business is (mostly) selling things online, the front door of the company website and e-commerce portal is everything. The lesson: identify your critical IT assets and prioritize them in both planning and resources.
Get a ‘hacker’s view’ of your environment
The other important lesson that the Vote Hacking Village has for enterprises and other organizations is that there is a benefit to having another set of eyes looking at your environment and assessing the security of your critical IT assets.
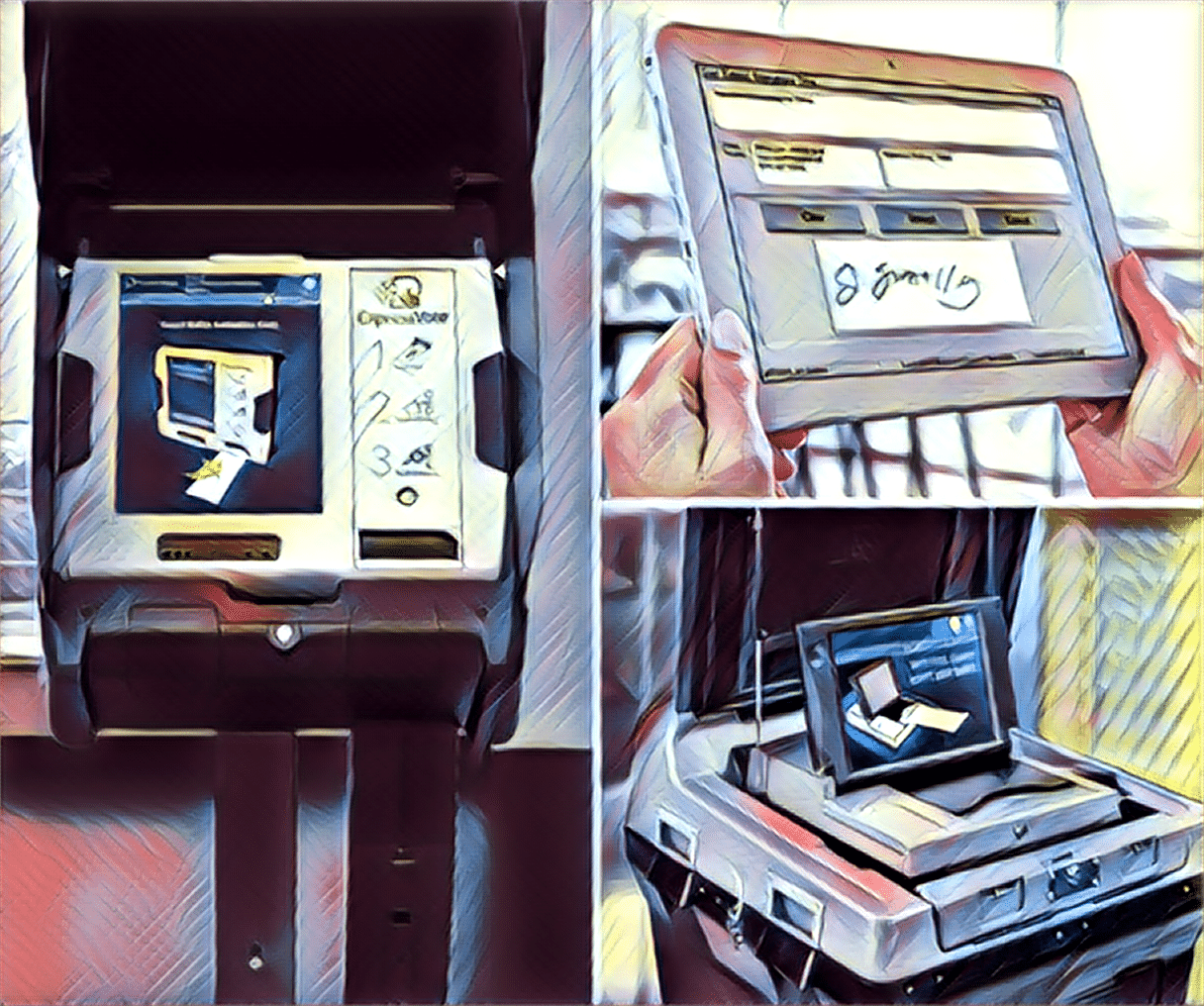
In the case of election security, our understanding of the vulnerability of elections systems is largely the product of the efforts of the organizers of Vote Hacking Village as well as of independent researchers who have purchased and analyzed electronic voting systems, poll books and other supporting technologies. In almost every case, these researchers were able to discover vulnerabilities or avenues of attack that the vendor and its customers had not considered, or knew about but chose to ignore.
Those efforts, which stretch back more than a decade, have caught the attention of lawmakers, prompted states and localities to reconsider or end their use of insecure voting platforms and prompted vendors to take steps to secure their hardware and share what they know via participation in groups like the Elections Infrastructure Information Sharing and Analysis Center (EI-ISAC).
The benefits of penetration testing and other “outside in” views are equally as valuable to enterprises and other organizations facing sophisticated cyber attackers. Cyber offense and cyber defense are wildly different skill sets, but only the largest and wealthiest firms can afford internal “insider threat” and pen testing teams. For everyone else, offensive skills like pen tests and red teams come as trusted outsiders. The value of such partners can be invaluable: helping you identify vulnerable systems within your environment or unconsidered avenues of attack.
Sure, unchecked, independent, crowd-sourced events like the Vote Hacking Village aren’t the kind of attention any company wants to invite. But there is real value in contracting with a team of skilled professionals to bring that level of scrutiny to your own environment and products: finding vulnerabilities in your cyber defenses and identifying gaps in your risk model.
The job of securing voting and elections is unique – and uniquely important. But that doesn’t mean we can’t absorb the lessons of The Vote Hacking Village as we look to secure our own environments from determined and sophisticated cyber adversaries!
(*) This post is sponsored by Hitachi Systems Security, which is a supporter of The Security Ledger. For more information on how Security Ledger works with its sponsors and sponsored content on Security Ledger, check out our About Security Ledger page on sponsorships and sponsor relations.